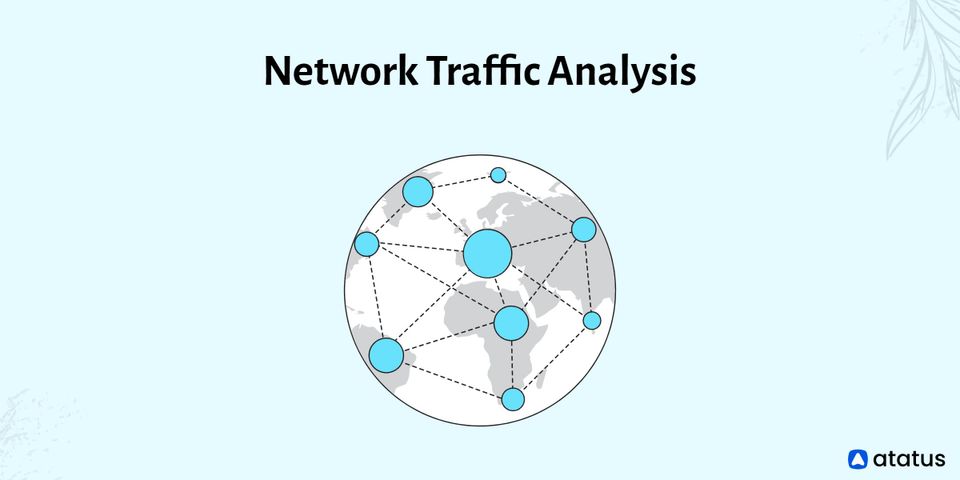
As networks become more complex, expansive, and smart, networks and network-related technologies are always evolving. The Internet of Things (IoT), software-defined networking, and the cloud all help to accelerate this rise.
Businesses must discover strategies to adjust to and manage the configurations of their numerous connected devices in this world of technology that is advancing quickly. The network configuration management tools that support them must evolve at the same rate as the wider market.
We will cover the following:
- What is Network Configuration?
- What is Network Configuration Management?
- Why is Network Configuration Important?
- Network Configuration Manager (NCM) Functions
- Benefits of Network Configuration Manager
- What Qualities Should a Network Configuration Manager Have?
What is Network Configuration?
Network configuration is the process of allocating network configurations, policies, flows, and controls. It is simpler to perform network configuration changes in a virtual network since real network appliances are replaced by software, eliminating the need for labor-intensive manual configuration.
A centralized configuration manager and network configuration manager can also automate and manage network configuration, significantly decreasing manual IT workload and making it simpler to:
- Maintain a network
- Make configuration changes
- Relaunch devices
- Track and report data
Switch/router configuration, host configuration, software, firewall setup, and network topology are some fundamentals of network configuration that can be managed using rest APIs.
What is Network Configuration Management?
Network configuration is the act of initially configuring a network's operation, flow, and controls–basically, keeping and organizing the data related to every component of your network.
Therefore, network configuration management is the continual activity of controlling the installation of all network devices' software and firmware and their configuration and maintenance. It includes finding devices, keeping track of their setup and condition, and keeping track of their inventory.
The network configuration management database is at the heart of this procedure. The network manager will search the database when something goes wrong and the network has to be fixed, modified, or updated so they can decide on the best course of action.
Every physical device's IP address, location, information about its software, versions, upgrades, and default settings are all kept in the database.
The presence of a reliable network configuration management solution is crucial for businesses. A network configuration manager enables management to keep track of any changes made to device settings and how those changes may affect the network's overall security.
Some changes may endanger the privacy of your users or result in a weak spot in your network security. Additionally, devices may become vulnerable to attacks due to the firmware that has been loaded on them. Software for managing network settings keeps track of all the firmware on your equipment and releases updates.
Why is Network Configuration Important?
The proper network configuration can support and enhance network security, increase network stability, and support the flow of data via a network. Additionally, using configuration tools and/or network configuration management can offer a variety of advantages, such as:
- Automated data tracking and reporting make it possible for administrators to detect configuration changes, potential threats, or other problems
- A quick method to implement large-scale changes, like changing all passwords at once if passwords are hacked
- The ability to quickly restore network configuration to a previous state
- Reduced downtime as a result of improved visibility and the capacity to recognize changes immediately
- Streamlined upkeep and repair of network connections, hardware, and software
- The capacity to restart a device when it malfunctions thanks to unified configuration management
Network Configuration Manager (NCM) Functions
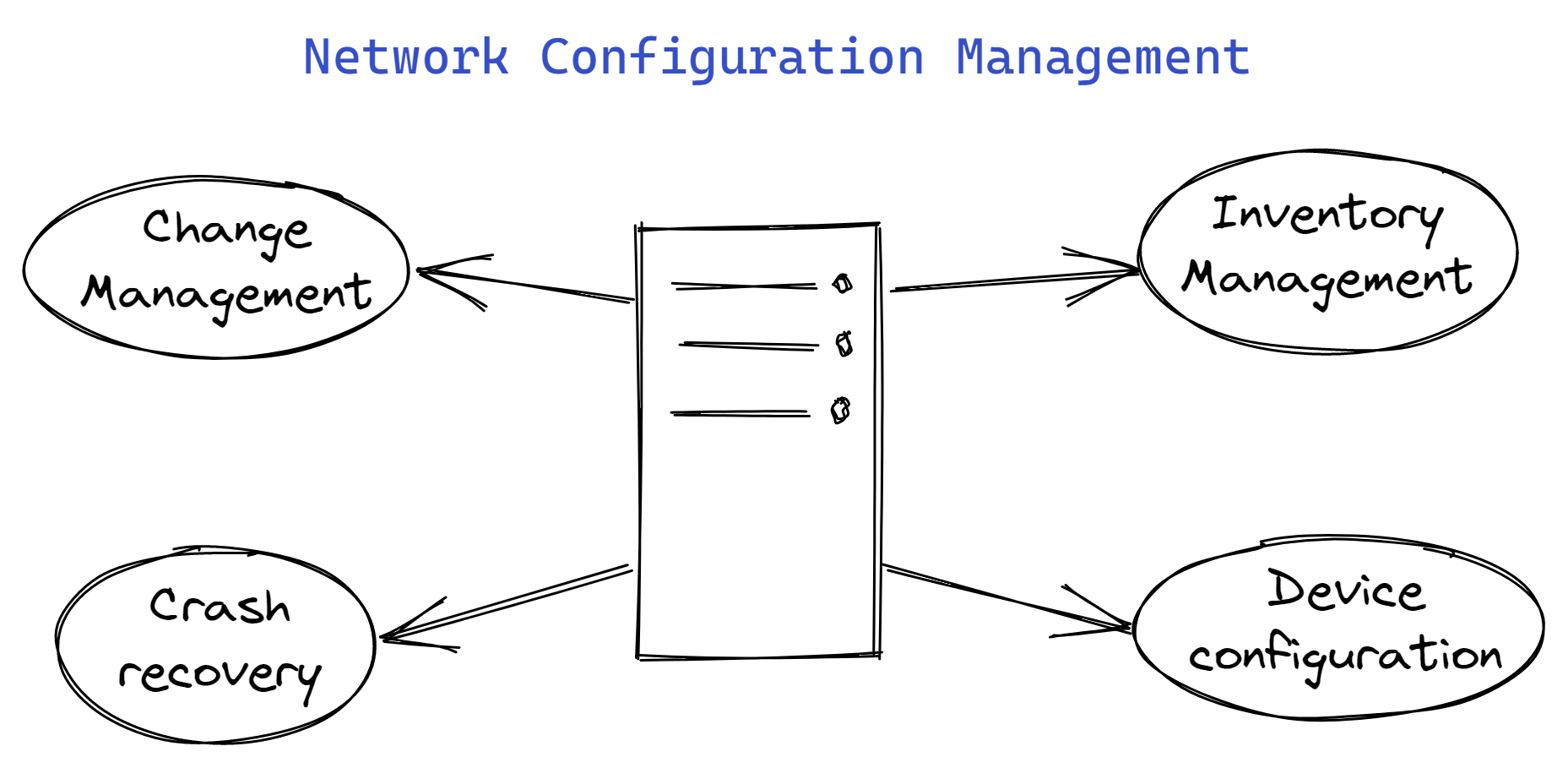
Functions of Network Configuration Manager (NCM) can also include the following, but are not limited to them:
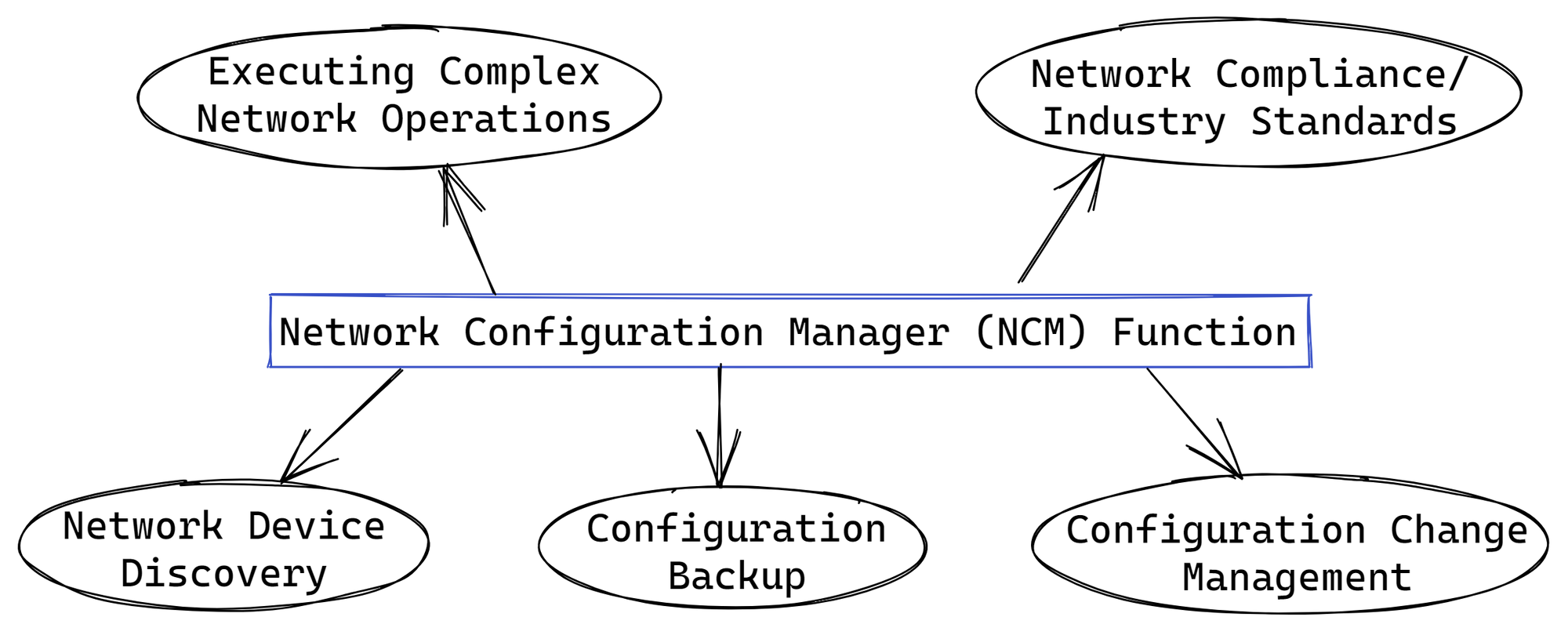
Network Device Discovery
In network configuration management, the first step is to find your device and add it to the inventory. It's crucial to maintain track of the hardware characteristics of your network's devices.
An informative inventory will help the network manager in doing regular audits in addition to increasing visibility into the network equipment.
The inventory provides a detailed view of the device data, including serial numbers, interface details, port configurations, and hardware details of the device, which are helpful when preparing audit reports.
Configuration Backup
A network operator must always be prepared for a network malfunction, and taking network backups is the most essential step in becoming disaster-ready. A flawed modification or update can result in issues like a network outage or security breach.
Any such occurrences can be handled right away using network configuration management (NCM) by replacing the flawed configuration with a reliable copy from the backup.
Configuration Change Management
It is advised that you maintain a list of your users to make it simpler to spot configuration changes. It is essential to prevent any illegal alteration that can have a negative outcome in a network with multiple operators.
These simply lessen the likelihood that something will go wrong on the network, but they do not completely guarantee that it won't.
Configuration backups become useful in this situation. Using Network Configuration Management (NCM), you can easily upload a reliable version of the configuration, restore the device, and guarantee business continuity.
Executing Complex Network Operations
Numerous network procedures that are carried out as part of NCM can occasionally be automated.
Applying the update to each device separately would be a laborious task, for example, if you needed to change the password on all Cisco routers connected to a network. This is where configuration templates, sometimes known as "Configlets," are useful.
Using configlets, you can centrally carry out this action across all of the devices. They also have the benefit of scheduling, which eliminates the need for the user to be present while the operation is being carried out.
Network Compliance/Industry Standards
Your network equipment needs to adhere to a few industry standards. This is done to protect the security of your data and the reputation of your business.
Network configuration management aids in ensuring adherence to organizational, security, and regulatory standards including FISMA, SOX, HIPAA, or NIST 800-53, SAFE, PCI, and DISA STIG.
Devices and systems are correctly configured to adhere to corporate and regulatory requirements due to out-of-the-box templates. Utilize completely adjustable rules to compare your configuration to a "gold-standard" configuration.
Benefits of Network Configuration Manager
The potential of network configuration management to lessen network and application downtime is one of its main advantages.
- Auditing and Reviewing Configurations
You can't find all the information in the configuration files. They won't display any dynamic data, such as ARP tables, interface error numbers, or CPU or memory utilization levels. However, they do provide you with a very helpful initial snapshot. Additionally, the data is helpful for tasks like security audits. They display the precise VPN settings, firewall rules, and IDS/IPS traffic inspection methods. - Automatic Generation
We can make mass modifications using a configuration management tool, among other things. A very helpful feature of configuration management software is this. - Reduce Errors
The number of outages brought on by configuration errors can be greatly decreased using automated network configuration management technologies. This is because human implementation or documentation errors frequently cause these issues. Tools for configuration management track changes, audit configurations, and streamline operations while automatically documenting all tool-related changes. - Reports
Reporting is the initial application. The configuration management tool can instantly display all the devices that changed and precisely what the changes were if it compares today's backup to yesterday's backup. - Roll Back Any Changes with Undesirable Results
Configuration management tools can roll back changes to earlier settings if an administrator makes a change only to discover later that it led to a misconfiguration, saving time and resolving problems. - Streamline Processes
Configuration management tools also make it possible to streamline procedures, which is another advantage. You need tools that make it simple for you to plan backups and receive alerts when backups fail as your network expands. You need a tool with features that lets you easily browse old and restore backups.
What Qualities Should a Network Configuration Manager Have?
By automating the management of your network configuration, you can coordinate changes throughout the whole network, save time on time-consuming but critical operations, and ensure that your network performs at its best.
A competent network configuration manager will reduce configuration errors and enhance network security. It should be capable of performing the following significant duties:
- Establish a setup baseline
- Revert modifications to older settings
- Keep a record of any modifications to the network configuration
- Distribute updates to firmware
- Create configuration snapshot backups
Additionally, you can decide to search for network configuration tools that can:
- Make configuration updates available in bulk
- Conduct compliance audits
- Manage firmware patches
Conclusion
In the past, network configuration management needed manual labor to configure network devices by manually inputting changes in a command-line interface (CLI). This inevitably led to several configuration errors. There were also no provisions for going back to a previous version.
The process of keeping track of, organizing, and maintaining the data relevant to the network devices in your company is known as network configuration management. It is in charge of installing the necessary firmware and software and setting up and maintaining network equipment.
The fundamental goal of configuration management is to make it possible to quickly set up and replace a network device's functionality following a malfunction. If you don't have a recent backup of that device, you'll have to configure the new device from scratch.
Also Read:
IT Operations Management (ITOM)
Atatus API Monitoring and Observability
Atatus provides Powerful API Observability to help you debug and prevent API issues. It monitors the user experience and is notified when abnormalities or issues arise. You can deeply understand who is using your APIs, how they are used, and the payloads they are sending.
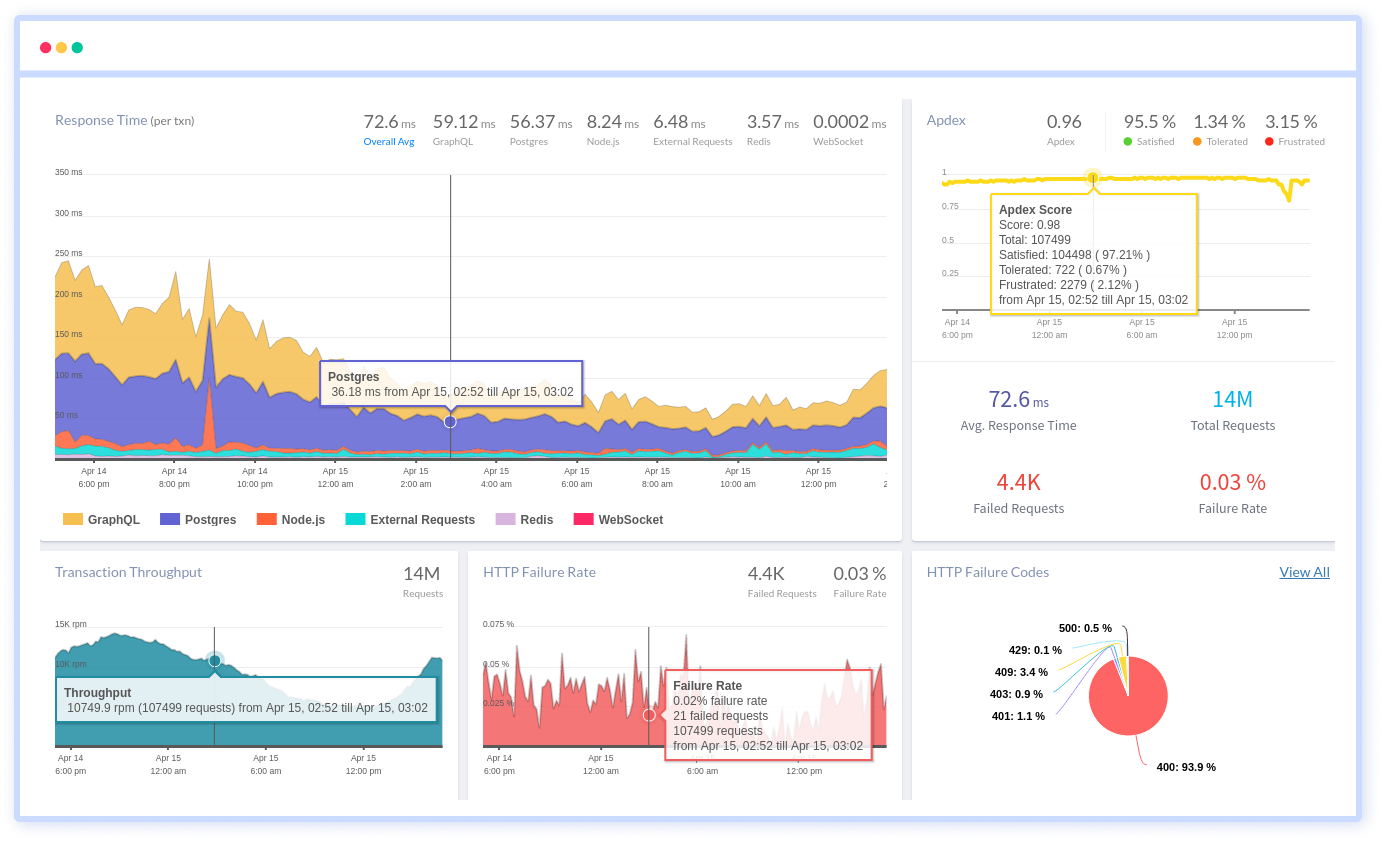
Atatus's user-centric API observability monitors the functionality, availability, and performance of your internal, external, and third-party APIs to see how your actual users interact with the API in your application. It also validates rest APIs and keeps track of metrics like latency, response time, and other performance indicators to ensure your application runs smoothly. Customers can easily get metrics on their quota usage, SLAs, and more.