There are sensitive documents, algorithms, and records in every company. If you overprotect them, your company's operations will come to a standstill. If you leave them open, you risk having major security difficulties. Role-Based Access Control (RBAC) is a solution to this problem.
Role-Based Access Control (RBAC) systems assign access and actions to users depending on their role in the system. Everyone in that position has the same set of privileges. Those in various roles have varying levels of authority.
Here’s how it is done:
- What is Role-Based Access Control?
- Implementing Role-Based Access Control
- Benefits Of Role-Based Access Control
- Disadvantages of Role-Based Access Control
- Best Practices for Implementing RBAC
What is Role-Based Access Control?
Role-Based Access Control (RBAC), often known as Role-Based Security, is a system access control mechanism. It requires assigning permissions and privileges to approved users to grant them access.
Role-based access control is used by most big companies to give their employees different levels of access depending on their positions and responsibilities. This protects sensitive data and ensures that employees have only the information and activities they need to complete their jobs.
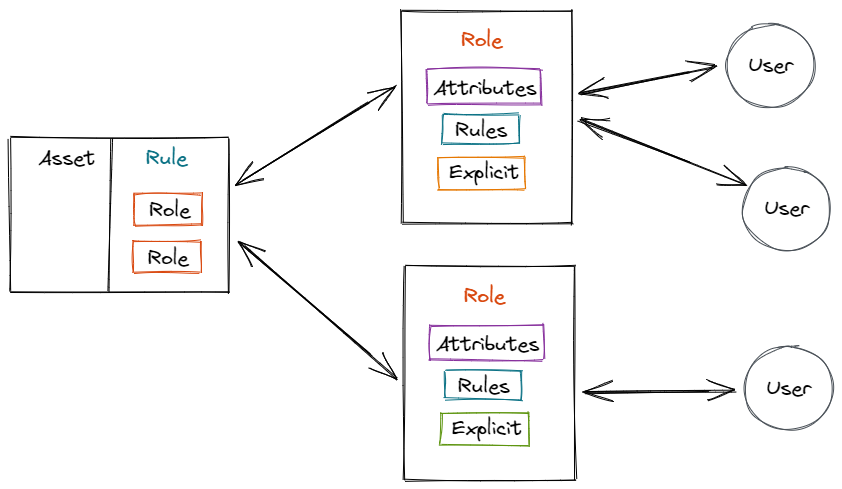
A role-based access control role is allocated to each employee in a company, and this position determines which permissions the system grants the user. You can assign a user the roles of administrator, expert, or end-user, and restrict their access to certain resources or tasks. Some employees may be permitted to create and modify files, while others may only be permitted to view them.
In research, Ferrailo and Kuhn offered an alternative to the classic concepts of Mandatory Access Control (MAC) and Discretionary Access Control (DAC). RBAC established three basic access control requirements:
- Role Assignment
Subjects are allocated roles and are only allowed to transact if the defined user role allows it. - Role Authorization
Subjects can only use roles for which they have been given permission. - Transaction Authorization
Subjects can only perform out transactions that their role memberships have approved.
Roles are the most important feature of RBAC. A role refers to a collection of permits. This enables companies to offer appropriate permissions to employees or visitors while maintaining a role hierarchy of privileges and permissions.
Implementing Role-Based Access Control
Organizations can improve their security posture and comply with security regulations by using role-based access control. However, adopting role-based access control across a whole business can be difficult, and stakeholders may push back. You should approach RBAC implementation as a set of steps if you want to succeed:
- Understanding Your Business Requirements
Before implementing RBAC, conduct a comprehensive requirements analysis to analyze job functions, supporting business processes, and technology. You should also evaluate any regulatory or audit requirements, as well as your organization's present security posture. Other methods of access control may also be beneficial. - Planning the Scope of Implementation
Determine the breadth of your RBAC requirements and plan the implementation to meet the demands of your organization. Concentrate your search on systems or applications that store sensitive information. This will also help your company in navigating the transition. - Defining Roles
Once you've completed the requirements analysis and understand how individuals accomplish their activities, it'll be much easier to identify your responsibilities. Excessive or insufficient granularity, role overlap, and providing too many exceptions for RBAC permissions are all frequent role design mistakes to avoid. - Implementation
Rolling out the RBAC is the final phase. Do this in phases, to avoid an overburdening task and business disruption. Start with a small set of users. Before increasing granularity, start with coarse-grained access control. Collect user feedback and monitor your surroundings to plan the next steps in the implementation process.
Benefits Of Role-Based Access Control
RBAC has the following benefits:
- Security
RBAC improves overall security in terms of privacy, compliance, confidentiality, access management to resources, and other sensitive data and systems. - Selective Access
RBAC systems allow users to have many roles at the same time, each with its own set of permissions. - Separation of Duties (SoD)
The concept of separation of duties(SoD) refers to the idea that no single person has complete control overwork. Organizations gain from SoD since cybersecurity on a single account will not do major damage to systems. - Simple Onboarding
You don't have to worry about people's permissions as they join, move within, or are promoted within your company; all you have to worry about is that they're in the appropriate location. The rest is taken care of by the roles. - Decrease Blunders
Traditional security administration cause errors. Individual permissions provide you with a lot of opportunities to make a mistake. You're less likely to give someone too much (or too little) power if you change a role's access. - Flexibility
Permissions associated with each position can be reviewed and adjusted by IT companies regularly. - Maximizing Operational Efficiency
RBAC is a simple and logical solution to access control. Rather than attempting to administrate lower-level access control, all roles can be aligned with the business's organizational structure, allowing users to work more efficiently and autonomously. - Security as a Function of Organizational Structure
RBAC enables organizations to create hierarchies for granting permissions based on seniority or organizational topology.
Disadvantages of Role-Based Access Control

The typical definition of RBAC as a mechanism of controlling access conjures up thoughts of frustration and friction in the minds of many users, and without careful implementation, those effects may be realized.
- Requires Business Knowledge
When it comes to defining positions, there is no such thing as a one-size-fits-all solution. When deciding how to define roles and manage access for those roles, organizations must work together across departments. This requires a thorough understanding of the organization's ideal structure as well as the technical infrastructure that supports it. - Lacks Adaptability
It's no surprise that RBAC has a reputation for being overly strict. Organizations grow, teams develop, and access requirements change. The roles you defined at the start of your RBAC project may no longer be appropriate for your company's objectives. Admins are also under pressure to promptly onboard new workers, especially those with duties that have yet to be established. - Leads to Role Explosion
One of the most typical RBAC objections is role explosion. It occurs when actual responsibilities and access requirements diverge from those described in your policy documents, even in modest ways. And roles that were created as a quick fix tend to remain around. Even when the people for whom these roles were created leave or change employment within the organization, administrators may forget or even choose to leave them in place. As a result, privilege creep and chaos have emerged.
Best Practices for Implementing RBAC
RBAC implementation in your company should not be handled lightly. Several general actions can be taken to bring the team on board without producing needless confusion or workplace irritations. There are a few things to consider.
- Current Status
Make a list of all the security-related software, hardware, and applications. For the most part, it will be a password. However, you might wish to include a list of password-protected server rooms. Physical security is a crucial component of data protection. List who has access to all of these programs and regions, as well. This will provide you with an overview of your current data situation. - Current Roles
Even if you don't have a formal roster or role list, figuring out what each team member does may only require a little conversation. Organize the team so that it does not suffocate creativity or the current culture. - Make a policy
Any changes made must be documented and made available to all existing and prospective employees. Even if you utilize an RBAC tool, having a document that properly explains your new system will help you prevent issues. - Make Changes
It's time to make the modifications after the current security status and roles are understood (not to mention a policy is developed). - Continually Adapt
RBAC's first iteration will almost certainly need some tuning. Early on, you should regularly assess your roles and security status. First, determine how well your creative/production process is operating, and then determine how secure your process is.
Data protection is a critical business function for any organization. An RBAC system can help ensure that the company's data complies with privacy and confidentiality regulations. It can also secure essential business activities, such as access to IP, that has a competitive impact on the company.
Conclusion
Role-Based Access Control (RBAC) is an advanced access control system that restricts network access based on an individual's organizational role. In RBAC, roles refer to the different levels of network access that employees have.
If lower-level employees do not need sensitive data to fulfill their responsibilities, they are frequently denied access. If you have several employees and rely on third-party vendors and contractors to handle network access, this is extremely important. RBAC will help in the protection of your company's sensitive data and critical applications.
Explore:
Containers-as-a-Service (CaaS)
Enterprise Application Integration (EAI)
Monitor Your Entire Application with Atatus
Atatus is a Full Stack Observability Platform that lets you review problems as if they happened in your application. Instead of guessing why errors happen or asking users for screenshots and log dumps, Atatus lets you replay the session to quickly understand what went wrong.
We offer Application Performance Monitoring, Real User Monitoring, Server Monitoring, Logs Monitoring, Synthetic Monitoring, Uptime Monitoring, and API Analytics. It works perfectly with any application, regardless of framework, and has plugins.

Atatus can be beneficial to your business, which provides a comprehensive view of your application, including how it works, where performance bottlenecks exist, which users are most impacted, and which errors break your code for your frontend, backend, and infrastructure.
If you are not yet an Atatus customer, you can sign up for a 14-day free trial.