When it comes to IT system management and monitoring, logs are one of the most useful assets. Logs provide the intelligence you need to discover issues that could influence performance, compliance, and security since they record every action that occurs on your network. As a result, any monitoring system should include log management.
The first hurdle is to aggregate all of your logs into a single, easily accessible area, which you may do as part of your logging system setup.
We will cover the following:
- What is Log Analysis?
- How does Log Analysis Work?
- Log Analysis Methods
- Benefits of Log Analysis
- Why Log Analysis is Important?
What is Log Analysis?
The process of deciphering computer-generated log messages, also known as log events, audit trail data, or simply logs, is known as log analysis. Log analysis provides useful indicators that show what's been happening across the infrastructure. This information can be used to improve or resolve performance issues in an application or IT infrastructure. Companies examine logs to proactively and reactively manage risks, comply with security policies, audits, and regulations, and understand online user behaviour.
A log is a large file that records all activity in the operating system, software applications, and devices. Messages, error reports, file requests, file transfers, and sign-in/out requests are all documented automatically in logs by the system administrators. The activity is also time-stamped, which assists IT professionals and developers in creating an audit trail in the event of a system failure, breach, or other unusual occurrences.
Log analysis can indicate potential vulnerabilities such as security breaches or impending hardware failure by providing information about system performance.
How does Log Analysis Work?
Applications, networks, devices (including programmable and IoT devices), and operating systems generate logs, which are time-series records of actions and activities. For real-time log analysis, they're usually saved in a file or database, or in a specialized application called a log collector.
A log analyst's job is to help analyse a wide range of log data and messages in context, which needs log data normalization to maintain consistency in language. This avoids any confusion that would happen if one function indicates 'normal' and another indicates 'green,' both indicating that no action is necessary.
In most cases, log data is collected for the log analysis program, cleansed, formatted, or normalized, and then presented for expert analysis to find trends or uncover abnormalities like a cyber-attack or data exfiltration. The steps for performing log file analysis are as follows:
- Data Collection
A central database collects data from hardware and software probes. - Data Indexing
Data from all sources are centralized and indexed to improve searchability, allowing IT professionals to find problems or patterns more quickly. - Analysis
Normalization, pattern recognition, correlation, and tagging are all log analysis techniques that can be conducted either automatically or manually, depending on the situation. - Monitoring
When anomalies are found, a real-time, self-contained log analysis platform can send out notifications. Most continuous monitoring of the entire IT stack relies on this form of automated log analysis. - Reports
A log analysis platform includes both traditional reports and dashboards, which provide at-a-glance or historical views of metrics for operations, development, and management stakeholders.
Log Analysis Methods
Due to the vast volume of data generated in today's digital world, it's become unfeasible for IT professionals to manually monitor and analyse logs across a large IT infrastructure. As a result, they required a sophisticated log management system as well as strategies that automate essential data gathering, formatting, and analysis operations.
Among the methods used are:
- Artificial Intelligence
Modern log analysis systems can automatically recognize and delete or ignore log data that do not help uncover anomalies or security breaches using artificial intelligence and machine learning (AI/ML) capabilities. This function sometimes referred to as "artificial ignorance," allows log analysis to issue alarms when scheduled routine occurrences do not occur when they should. - Correlation
Analysts can aggregate logs from different sources to help decode an event that isn't observable in a single log. This is especially valuable during and after cyber-attacks when a correlation of logs from network devices, servers, firewalls, and storage systems can reveal data relevant to the attack and patterns that aren't visible in a single record. - Normalization
Converting diverse log element data into a standard format can assist ensure that comparisons can be made and that data can be stored and indexed centrally regardless of log source. - Pattern Recognition
Modern machine learning (ML) technologies may be used to find patterns in log data that may indicate abnormalities, such as comparing messages concealed in an external list to see if there is a threat hidden in the pattern. This can help to filter out ordinary log entries, allowing analysis to focus on those that may reveal problems. - Structured
To provide the most value, all log data should be stored in a central location and formatted in a way that both humans and machines can interpret it. Much of the heavy lifting can now be done automatically due to advancements in log analysis technologies. To acquire the most complete perspective of events and anomalies, businesses should employ full-stack logging across all system components. - Tagging and Classification
Filters can be used to data that has been tagged with keywords and classified by type, which can speed up the discovery of important information. When tracking a virus that infects Windows servers, for example, all records of the class "LINUX" could be deleted.
Benefits of Log Analysis
These are the benefits that are provided by log analysis:
- Compliance
Many governmental or regulatory entities want proof of conformity with the plethora of regulations that affect practically every business. Logfile analysis can verify that the organization is complying with HIPAA, PCI, GDPR, and other regulations. - Efficiency
A log analysis framework can help your company become more efficient. Every department's IT resources can share a single log repository, and an organization's log data can be analysed to discover errors or trends in every business unit and department, allowing for quick correction. - High Availability
Timely action based on log analysis information can assist prevent a problem from escalating into a downtime issue. This, in turn, can assist ensure that the company fulfils its business objectives and that the IT department keeps its promises to offer services with a certain level of uptime. - Effectiveness of Sales and Marketing
Log analysis can help sales and marketing professionals identify which programs are effective and which should be adjusted by examining indicators such as traffic volume and the websites that customers visit. Traffic patterns can also aid in the redesign of a company's website to make it easier for consumers to find the most often requested information. - Security Enhancements
As cybercrime becomes more structured, the demand for more effective defences develops as well. If a breach or data loss does occur, event log analysis gives significant tools for adopting pre-emptive actions as well as forensic analyses after the fact. Log analysis can be used to uncover illegal access attempts and check that security operations and firewalls are configured properly. - Avoid over-or under-provisioning
While organizations must plan for peak demand, log analysis can assist determine whether there is enough CPU, memory, disk, and network bandwidth to fulfil current and future demands. Overprovisioning wastes IT funds, while under provisioning can result in service disruptions as organizations try to buy more resources or use cloud resources to meet demand fluctuations.
Why Log Analysis is Important?
As part of their compliance rules, most companies are obliged to archive and analyse logs. They must monitor and analyse system logs on a regular basis to look for errors, anomalies, or suspicious or unauthorized activity that is out of the ordinary. They can employ log analysis to re-create the sequence of events that led up to a problem and efficiently troubleshoot it.
Furthermore, while data log analysis may appear to touch solely the IT component of your organisation at first look, it actually affects all aspects of your business, including legal, financial, sales and marketing, human resources, security, and operations. You may spot issues before or as they arise with log analysis, saving time, avoiding unnecessary delays, and avoiding additional costs.
Conclusion
Log monitoring and log analysis are two different concepts that work together to speed up the process of resolving system or application issues.
For monitoring and alerting, security policy compliance, auditing, and regulatory compliance, security incident response, and even forensic investigations log analysis is a critical role. Enterprises may more easily discover possible threats and other issues, determine the fundamental cause and launch a timely response to manage risks by examining log data.
Atatus Log Monitoring and Management
Atatus is delivered as a fully managed cloud service with minimal setup at any scale that requires no maintenance. It monitors logs from all of your systems and applications into a centralized and easy-to-navigate user interface, allowing you to troubleshoot faster.
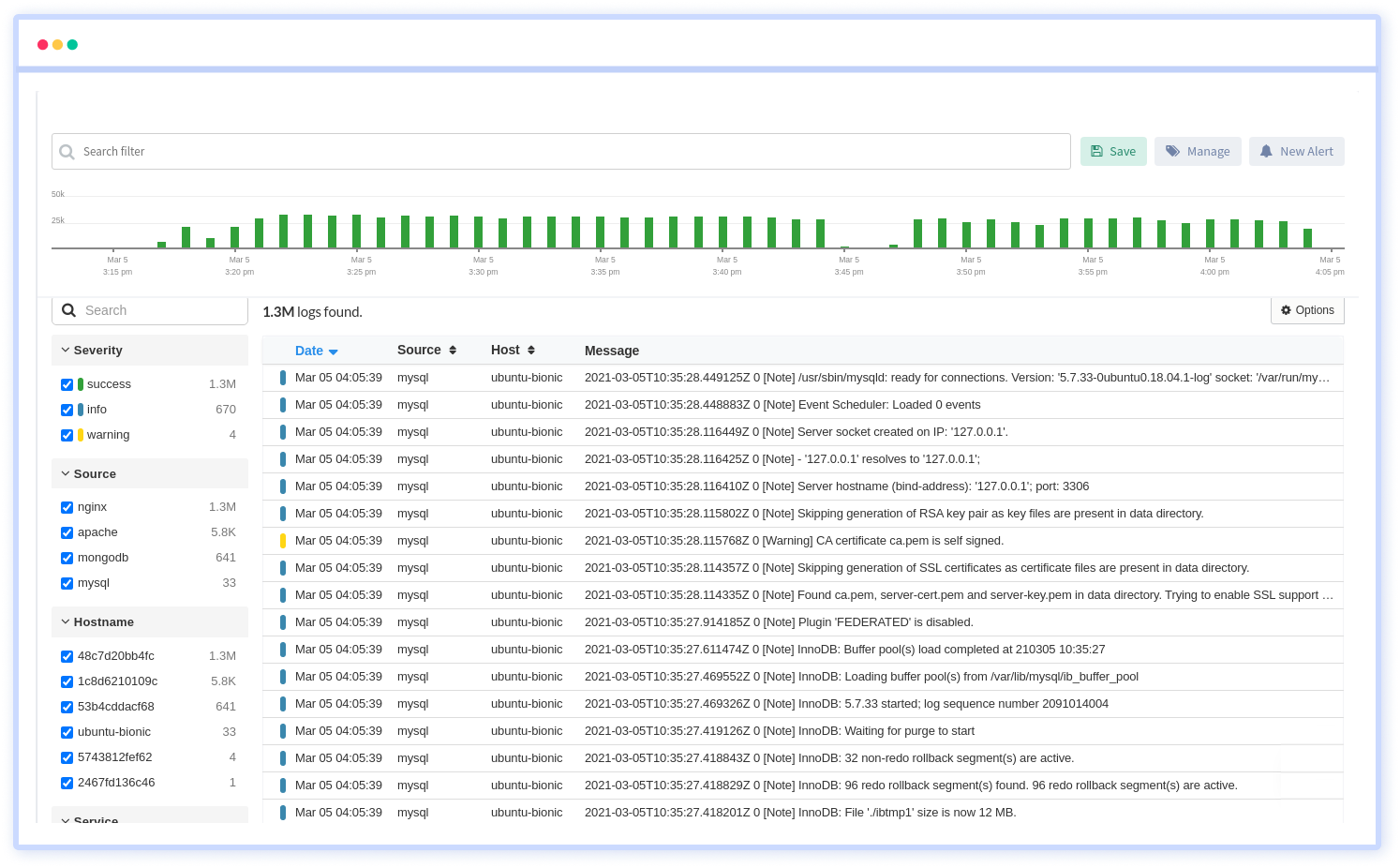
We give a cost-effective, scalable method to centralized logging, so you can obtain total insight across your complex architecture. To cut through the noise and focus on the key events that matter, you can search the logs by hostname, service, source, messages, and more. When you can correlate log events with APM slow traces and errors, troubleshooting becomes easy.