CNAPP: A Comprehensive Solution for Cloud-Native Application Security
A unique approach to security is needed when developing cloud-native apps that use microservices, containers, and serverless computing. The specific security issues that these cloud-native architectures provide are the focus of CNAPPs.
Traditional security solutions are frequently created to protect on-premises infrastructure and applications. However, new security strategies are required due to the adoption of cloud-native architectures and the migration to cloud computing. CNAPP's close this gap by offering security controls created especially for cloud-native apps.
Businesses must adopt strong security measures as they use cloud computing and move their applications and data there. Platforms for protecting cloud-native applications (CNAPPs) have arisen as specialised approaches to deal with the particular security issues that occur with cloud-native architectures.
One of the main benefits of a Cloud-Native Application Protection Platform (CNAPP) is its capacity to integrate several security capabilities into a centralised control set. By doing this, it makes it easier to manage cloud network security, which includes diverse duties including threat detection, risk remediation, and continual monitoring of security and compliance posture.
The capacity of Cloud-Native Application Protection Platforms (CNAPPs) to give visibility across various network components, such as virtual machines (VMs), orchestrators, private clouds, and public clouds, is one of their primary advantages. By combining previously separate cloud stacks into a single layer of abstraction, CNAPPs allow organisations to manage their security posture and policies on a comprehensive scale.
This article will give a general overview of the following topics:
- What is CNAPP?
- Why do we need CNAPP?
- What problems does CNAPP solve?
- How does CNAPP work?
- CNAPP Features and Capabilities
- Benefits of CNAPP
What is CNAPP?
A CNAPP is a complete Cloud-Native Security Solution. It offers a common control plane that integrates all security features to safeguard cloud environments, making your security cloud native.
A cloud-native application protection platform (CNAPP) is an all-in-one cloud-native software platform that makes it easier to monitor, identify, and respond to possible threats to and vulnerabilities in cloud security.
By doing so, the potential for greater human error and labour when utilising different solutions with disparate perspectives on application risk is eliminated, and the time required for threat detection and reporting is decreased.
Why do we need CNAPP?
We require Cloud-Native Application Protection Platforms (CNAPPs) for many reasons. The following are the main justifications for why CNAPPs are essential in the current cloud-native environment:
- Businesses are moving their applications and data to the cloud as cloud computing becomes more widely used. CNAPPs assist in making sure that the security of these cloud-hosted apps is strong throughout their lifecycle, guarding against potential attacks and vulnerabilities.
- CNAPPs are designed to meet the scalability and flexibility needs of cloud-native applications, and they provide security mechanisms that can change to accommodate these environments' dynamic nature.
- CNAPPs support businesses in adhering to legislative requirements as well as industry standards. They frequently offer tools for policy enforcement, auditing, and reporting, assisting organisations in proving compliance with security standards in cloud-native systems.
- To fully safeguard infrastructure and cloud-native applications, traditional security methods like firewalls and intrusion detection systems are no longer sufficient. By considering the cloud platform holistically and taking into account the special problems associated with cloud-native apps and bigger cloud footprints, CNAPP solutions offer a thorough security and targeted approach to securing cloud-native applications.
- Cloud-native application and infrastructure monitoring, a more focused approach to cloud threat detection and response, compliance management, including special cloud compliance challenges, and the overall security benefit of lowering the risk of cyber attacks and data breaches are all advantages of CNAPP solutions.
What problems does CNAPP solve?
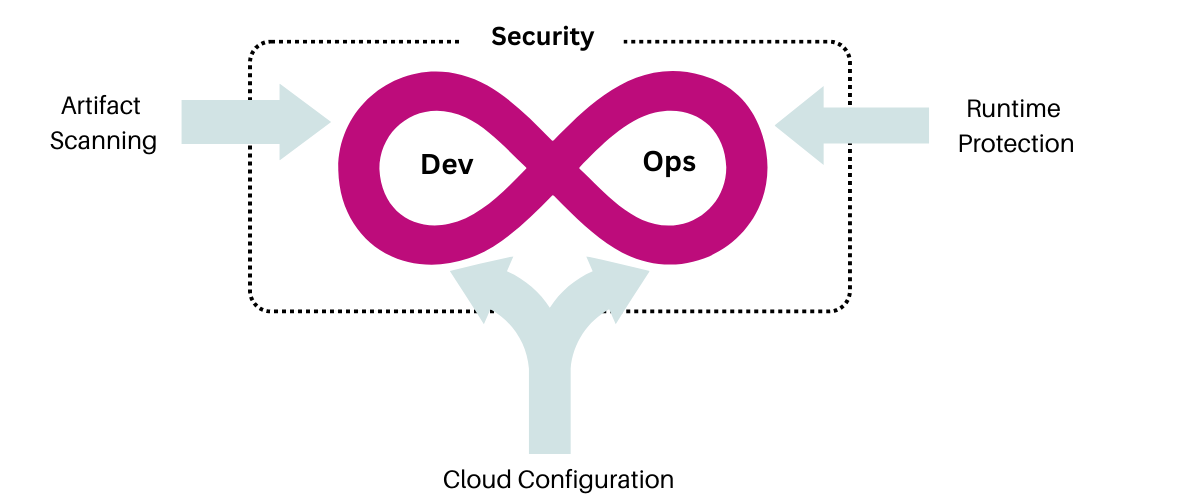
Enterprises should view security and compliance as a continuum spanning development and operations and work to combine technologies whenever possible, as opposed to treating development and runtime as separate tasks that must be safeguarded and scanned using a variety of different tools. The CNAPP programme can help with this.
The goal of CNAPP is to provide full end-to-end security for cloud-native environments. Organisations should adopt an integrated platform strategy rather than using numerous point solutions that each address a specific security issue and need human assembly. To secure and protect cloud-native apps during development and production, CNAPP is a collection of security and compliance capabilities.
CNAPP may gain a comprehensive view of application risk by transferring context between development and production, allowing it to reliably protect applications throughout their life cycle.
CNAPP is a unified platform that combines the capabilities of various existing cloud security categories, such as "shift left" artefact scanning, Cloud Security Posture Management (CSPM) and Kubernetes Security Posture Management (KSPM), IaC scanning, Cloud Infrastructure Entitlements Management (CIEM), and Runtime Cloud Workload Protection Platform (CWPP).
How does CNAPP work?
Security is incorporated throughout the whole lifecycle of cloud-native applications by CNAPP. Development, testing, deployment, and production are all included. The platform offers a selection of security tools built to function with cloud-native apps, including:
Container security –By checking images for vulnerabilities, observing runtime activity, and enforcing runtime restrictions, CNAPP defends against container-based attacks.
Network security –Through traffic monitoring, security policy enforcement, attack detection and prevention, and traffic enforcement, CNAPP offers network security.
Application security –Through vulnerability detection, runtime behaviour monitoring, and runtime policy enforcement, CNAPP offers application security.
Data security – It is provided by CNAPP through the monitoring of data access, the enforcement of data protection laws, and the detection and prevention of data breaches.
Additionally, CNAPP offers sophisticated threat detection and response tools, such as automated incident handling, threat hunting, and security analytics.
CNAPP Features and Capabilities
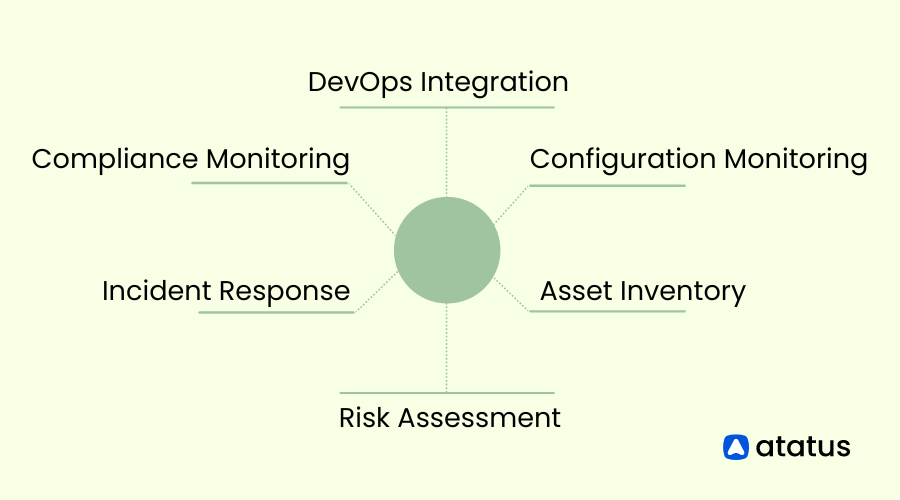
The CNAPP consists of many parts that function as separate security frameworks. The main organisational frameworks used by CNAPP are listed below:
1. Cloud Security Posture Management (CSPM)
Cloud Security Posture Management (CSPM) automates security procedures for cloud environments, including finding misconfigurations, correcting them, examining compliance, and using Artificial Intelligence (AI) to direct developers and other security personnel as they address problems.
Additionally, CSPM continuously monitors the cloud-native applications and issues notifications whenever an error or configuration issue is discovered. By regularly carrying out these tasks, CSPM assists businesses in enhancing the security of their cloud infrastructure.
2. Vulnerability Management
Vulnerability Management is a critical capability of a CNAPP that focuses on identifying and managing vulnerabilities within cloud-native applications and their underlying infrastructure.
It includes features for vulnerability scanning, assessment, prioritization, and remediation. The CNAPP scans for known vulnerabilities in applications, libraries, and system components, assesses their severity, and provides guidance on mitigating actions.
Vulnerability Management ensures that applications are protected from known security flaws and assists in maintaining a secure application environment.
3. Kubernetes Security Posture Management (KSPM)
Kubernetes Security Posture Management (KSPM) is not generally included in the CNAPP because it focuses primarily on Kubernetes deployments.
Thus, on a broader level, KSPM tools execute similar activities to the rest of the components but are better suited to Kubernetes deployments. KSPM entails misconfiguration of resources like pods and clusters, compliance with Kubernetes standards, checking RBAC policies, and more.
4. Cloud Detection and Response (CDR)
CDR capability is centered around detecting and responding to security threats and incidents within cloud environments. The CNAPP's CDR features utilize advanced threat detection mechanisms to monitor cloud-native applications and infrastructure components.
It analyzes real-time data, such as logs, network traffic, and system events, to identify indicators of compromise (IOCs), suspicious activities, or potential security breaches. CDR initiates incident response workflows, triggers alerts, and supports forensic analysis to mitigate the impact of security incidents.
5. Infrastructure as Scanning (IaS)
The CNAPP's IaC Scanning capability focuses on analyzing and evaluating the configuration and deployment code used in cloud environments. It scans Infrastructure-as
Code templates, such as Terraform or AWS CloudFormation scripts, to identify potential security vulnerabilities, misconfigurations, or compliance issues.
By conducting thorough assessments of infrastructure code, IaC Scanning ensures that cloud resources are provisioned securely and in line with best practices, reducing the risk of misconfigurations and potential security gaps.
6. Cloud Infrastructure Entitlements Management (CIEM)
CIEM capability provides comprehensive management of entitlements and access controls within cloud environments. The CNAPP's CIEM features enable organizations to monitor and manage permissions, roles, and privileges associated with cloud resources.
CIEM helps enforce the principle of least privilege, identify excessive or inappropriate access, and prevent unauthorized actions. It assists in maintaining a secure and compliant cloud infrastructure by monitoring and managing entitlements across the organization.
7. Data Security Posture Management (DSPM)
DSPM capability focuses on assessing and managing the security posture of data within cloud-native applications. It includes features for data classification, encryption, access control, and monitoring.
The CNAPP with DSPM helps organizations identify sensitive data, apply appropriate security controls, enforce data privacy regulations, and detect data breaches. DSPM ensures that data assets are protected throughout their lifecycle and that compliance requirements are met.
8. Cloud Workload Protection Platform (CWPP)
Cloud Workload Protection Platform (CWPP) is a platform that secures the workload of apps. CWPP operates across many cloud-native applications and environments and provides solutions dependent on whether the infrastructure is deployed in public, private, or hybrid cloud settings.
Cloud-native protection, workload protection, threat detection and response, compliance management, automation, and centralised management are the primary characteristics.
Benefits of CNAPP
- Enhanced Security: A thorough and specialised approach to cloud-native application security is offered by CNAPPs. They deal with the particular security issues that arise from cloud-native designs, such as container vulnerabilities, API assaults, and insecure setups. Using a variety of security tools, like vulnerability scanning, runtime protection, access control, and threat detection, CNAPPs assist organisations in improving their entire security posture.
- Scalability and Flexibility: CNAPPs are made to scale and adjust to the changing conditions of cloud environments. They can manage the elastic and distributed nature of cloud-native applications, ensuring that security measures can scale with the application workload and fit the changing requirements of the cloud environment. For cloud-native applications to be properly secured in dynamic cloud infrastructures, scalability and adaptability are essential.
- Simplified Management: CNAPPs offer centralised administration and orchestration capabilities, enabling security teams to set up and maintain security policies, keep an eye on security events, and produce reports from a single interface. This centralised method simplifies security operations, lowers complexity, and enhances overall visibility and control over the security of cloud-native apps.
- DevOps Integration: CNAPPs interface easily with DevOps practises and workflows. They make it possible to incorporate security into the development and deployment processes from the start, encouraging a DevSecOps culture. CNAPPs automate security controls, link with CI/CD pipelines, and enable security-as-code, ensuring that security is embedded into the whole application lifecycle. This connection enables the delivery of cloud-native applications to be more rapid and safe.
- Multi-Cloud Support: Numerous businesses use various cloud service providers to function in multi-cloud or hybrid cloud settings. CNAPPs provide multi-cloud architectures, enabling organisations to uphold uniform security policies, controls, and visibility across various cloud platforms. This guarantees that security measures can be employed consistently independent of the particular cloud provider being used.
- Compliance and Governance: CNAPPs support businesses in adhering to legislative requirements as well as industry standards. They give organisations tools for policy enforcement, auditing, and reporting, assisting them in proving compliance with security standards in cloud-native systems. CNAPPs support the management of security measures, data security, and privacy demands across cloud-native applications.
- Improved Incident Response: CNAPPs feature advanced threat detection algorithms and give real-time warnings and incident response capabilities. They assist organisations in detecting and responding to security issues more efficiently, lowering the time required to identify and mitigate possible threats. By providing actionable insights and automatic reaction capabilities, CNAPPs improve an organization's ability to identify, respond to, and recover from security breaches.
Conclusion
Businesses can strengthen the security posture of their cloud-native apps and defend against changing threats in dynamic cloud environments by adopting a CNAPP. Organisations should compare various CNAPP solutions based on their unique requirements, taking into account elements like scalability, performance, usability, and compliance with their cloud infrastructure.
By offering a centralised platform that streamlines security operations, improves threat detection and response capabilities, and assures ongoing monitoring and compliance with security regulations, CNAPPs assist organisations in efficiently managing and securing their cloud-native applications.
A CNAPP is a thorough tool that provides DevOps and DevSecOps teams with a unified and automated security solution that handles every stage of the application lifecycle, including workloads, containers, and security posture and compliance.
It offers general security and visibility for environments that use private, public, hybrid, and multiple clouds. Additionally, CNAPP automates tasks and checks your infrastructure and settings to thwart threats, increase productivity, and speed up response times when vulnerabilities are found.
Monitor Your Entire Application with Atatus
Atatus is a Full Stack Observability Platform that lets you review problems as if they happened in your application. Instead of guessing why errors happen or asking users for screenshots and log dumps, Atatus lets you replay the session to quickly understand what went wrong.
We offer Application Performance Monitoring, Real User Monitoring, Server Monitoring, Logs Monitoring, Synthetic Monitoring, Uptime Monitoring, and API Analytics. It works perfectly with any application, regardless of framework, and has plugins.

Atatus can be beneficial to your business, which provides a comprehensive view of your application, including how it works, where performance bottlenecks exist, which users are most impacted, and which errors break your code for your frontend, backend, and infrastructure.
If you are not yet an Atatus customer, you can sign up for a 14-day free trial.
#1 Solution for Logs, Traces & Metrics
APM
Kubernetes
Logs
Synthetics
RUM
Serverless
Security
More


