What is User Datagram Protocol (UDP)?
One of the easiest transport layer protocols available in the TCP/IP protocol suite is the User Datagram Protocol (UDP). The communication mechanism involved is minimal.
With UDP, neither the receiver nor the sender receives any acknowledgements of packets received. This protocol's shortcoming makes it unreliable and easier to process than many other protocols.
Although UDP is considered an unreliable transport protocol, it uses IP services to ensure the best attempts are made to deliver data.
Table of contents
- What is UDP?
- How UDP works?
- Structure of UDP header packets
- The UDP protocol attributes
- Violations and threats to DDoS - UDP
What is UDP?
User Datagram Protocol (UDP) is a communications protocol designed for the establishment of low-latency and loss-tolerant connections between websites. A time-sensitive transmission such as video playback or DNS look-ups is normally handled by UDP, or User Datagram Protocol.
Because no formal connection is established before data is transferred, it speeds up the transmission of data. As a result, data can be transferred rapidly, but packets can be lost in transit, which means that DDoS attacks are easily possible.
The UDP protocol is a method of transmitting data besides TCP. The two protocols are often called UDP/IP or TCP/IP since they run on top of IP.
However, they differ significantly. Communication between processes is enabled by UDP, while communication between hosts is enabled by TCP.
How UDP works?
Datagrams are sent between computers using the UDP via IP. In the UDP, data is gathered into UDP packets and header information is added to the packets.
A packet length and a checksum are included in this data, as well as the source and destination ports. UDP packets are sent to their destinations after being encapsulated in IP packets.
The UDP protocol does this much simpler than other protocols; it sends packets to a target computer directly, without first establishing a connection, without checking whether the packets arrived properly or showing their order. It is called a 'datagram' when referring to UDP packets.
TCP is another common transport protocol, but UDP is faster. A 'handshake' automated process establishes a connection between two computers in a TCP communication.
The data packets will only be transferred once the handshake has been completed. This process does not apply to UDP communications instead data can be sent from one computer to another.
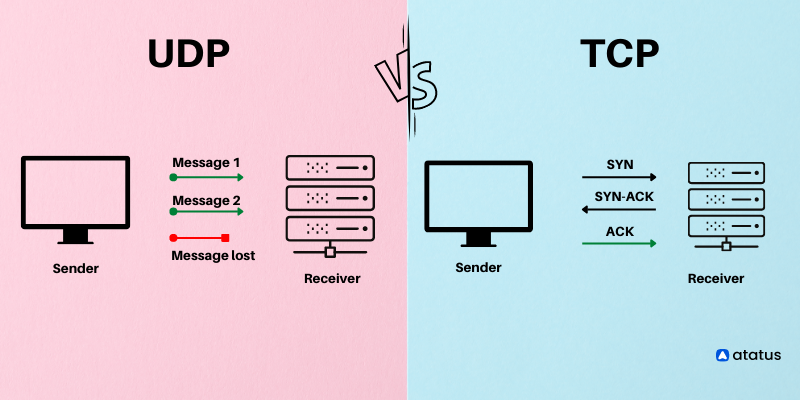
In addition, TCP communications indicate the order in which data packets should be received and confirm that packets arrive as intended.
If a packet does not arrive, for say, due to congestion in intermediary networks; TCP requires that it be re-sent. UDP communications do not include any of this functionality.
Some advantages arise from these differences. Because it does not require a handshake or verification of data delivery, UDP is much faster than TCP.
Despite this, there are tradeoffs associated with this speed. It is not possible to resend a lost UDP datagram. Because of this, UDP-based applications must be able to handle error messages, data loss, and duplicate data.
In technical terms, such packet losses are less caused by UDP than by how the Internet operates.
Most internet routers do not order packets or guarantee their arrival since it would require far too much memory. TCP works around this problem when applications require it.
Structure of UDP header packets
There are four fields totaling eight bytes in a UDP header, which is wrapped around datagrams. There are four fields in the UDP header:
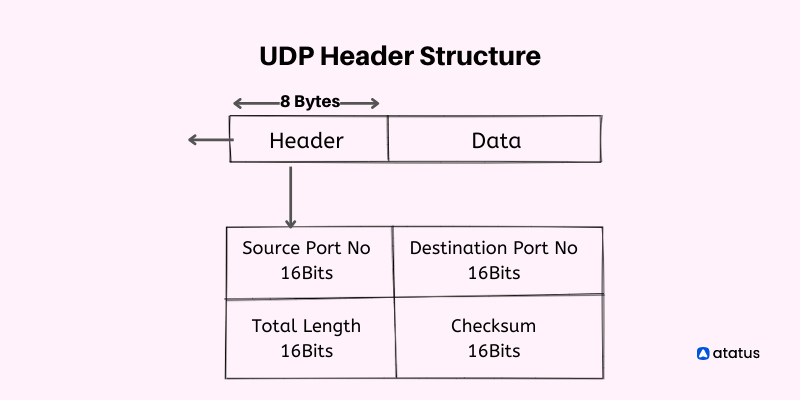
Source port number: Packets are sent to a port identified by 16 bits of information. It is possible to set this field to zero if the recipient computer does not need to respond.
Destination port number: The port on the device that receives the data. Between 0 and 65,535 are the possible UDP port numbers. An application-level service on the destination machine can be identified by this 16-bit information.
You can view the list of UDP ports in linux using the following command:
sudo lsof -i -n -P | grep UDP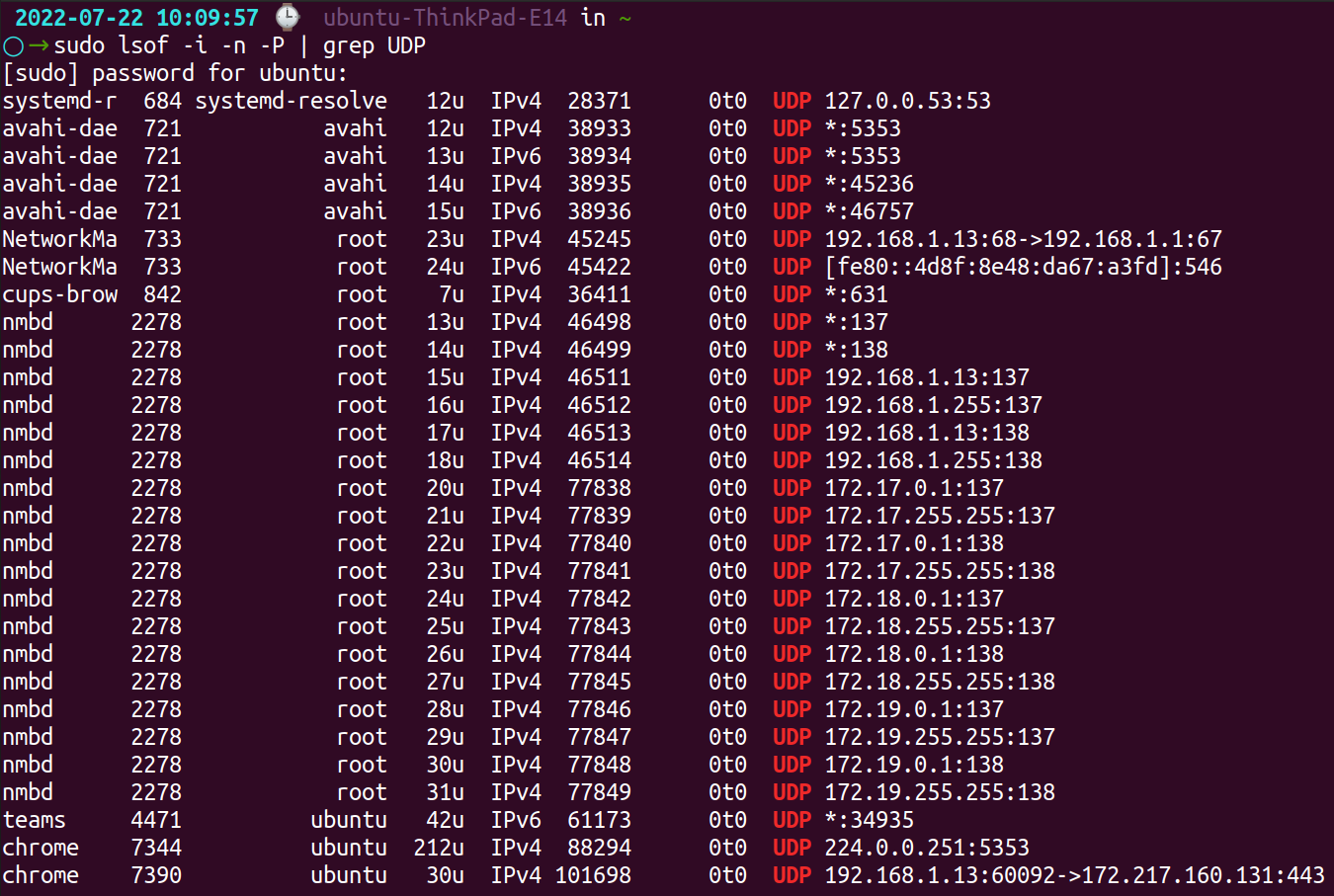
Length: A UDP packet's header and its full 16-bit length are specified in this field. Because the header size is 8 bytes, the minimum value would be 8 bytes. As a result of the IP protocol being used to transmit data, the UDP length field has some limitations.
Checksum: In addition to being 16 bits long, it is also not mandatory. Checksums are used by the receiver’s device to validate the integrity of the headers and payloads of the packet. IPv6 is obligatory, while IPv4 is just an option. As opposed to IP, UDP does not apply checksums to the header and data portions of the packet.
The UDP protocol attributes
Data loss tolerance is an asset of the User Datagram Protocol, which makes it a good choice for applications that require data resilience. The UDP protocol has the following attributes:
- Transport layer communication protocols are feasible for UDP. Communication mechanisms are limited to a minimum. As a best-effort delivery protocol, it is unreliable. There is no acknowledgement mechanism in UDP. This method is suitable for real-time applications where latency could be a concern since packets can be dropped and received in a distinct order than when they were transmitted.
- There is no guarantee that data will be delivered when ordered. As UDP files are not numbered, the receipt of the datagrams is not guaranteed in the same order as their sending.
- Transaction-based protocols can be implemented with it, such as Network Time Protocol (NTP) or DNS.
- An acknowledgement is not received by the sender of the packet when it is sent using stateless protocols.
- Due to its connection-less nature, UDP can transmit data faster than other protocols, since no virtual path is needed for the data to be transferred. The sender and receiver communicate in different paths, so packets are lost or received out of order as it doesn't use the virtual path.
- Gaming, voice or video conferencing, and streaming media are some of the scenarios where it can be used since it doesn't require real-time error correction.
- There is independent handling of segments. Because each UDP segment takes a different path to its destination, each is handled individually by others. As there is no connection between the sender and the receiver, UDP segments may be lost or delivered in an improper order.
Violations and threats to DDoS - UDP
DDoS attacks are very likely to occur using UDP. Due to UDP's lack of security mechanisms and closed-end connections. Spoofing packets with arbitrary IP addresses allows hackers to access the application directly.
Unlike TCP, UDP does not require a sender to receive packets from a receiver in order to start communication. DDoS attacks targeting UDP comprise:
DNS Amplification Threat
Malicious parties can take advantage of DNS amplification threats by sending UDP packets with a mocked IP address, which corresponds to the victim's IP address.
After sending their response, DNS resolvers notify the victim. DNS responses are drafted in such a way that they are much bigger than the initial request, causing attacks to be intensified.
Especially in large-scale implementations with numerous DNS resolvers and many clients, it can be devastating for the target system.
UDP Flood attack
With UDP flooding, large quantities of spoofed UDP packets are sent to numerous ports on a single server, knowing that the packet's real source cannot be verified. In retort to all requests, the server receives an ICMP 'Destination Unreachable' message, overburdening the server's system.
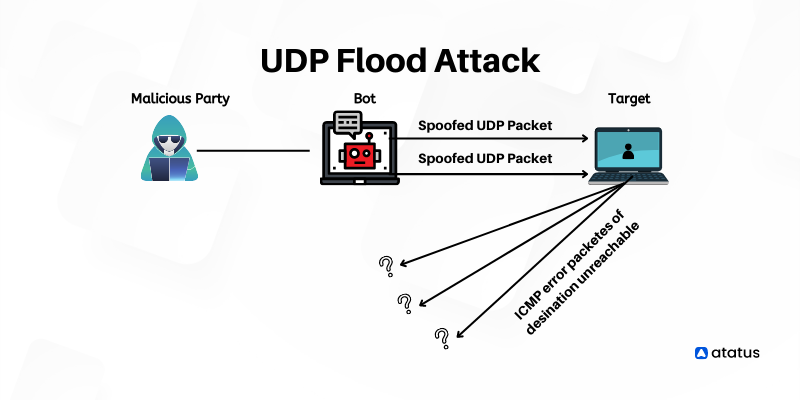
Aside from UDP flooding, DDoS attacks generally create network congestion by transmitting immense amounts of fake UDP packets to create generic network layer attacks. Using a cloud DDoS mitigation solution, a network's resources can only be scaled up on demand to prevent these attacks.
UDP Port Scan attack
A server's UDP ports can be found by sending UDP packets to their ports in order to determine which ports are open by an attacker. Servers responding with ICMP 'Destination Unreachable' messages are closed. As long as there is no response, the perpetrator is left to speculate that the port is open, which he uses to plot system exploitation.
Wrap-up
Most application developers are aware UDP does not deliver any kind of reliability, e.g., it does not allow packets to be retransmitted that are lost. Typically, this is the primary reason to use UDP.
As a result, applications mandating reliable message delivery should enforce the necessary protocol mechanisms.
An application can receive multiple copies of the same UDP datagram due to the best effort service's lack of protection from datagram duplication.
In this regard, application designers should ensure that their applications skillfully regulate datagram duplication and may need to enforce mechanisms to detect duplicate datagrams.
As a result of routing transients, intermittent connectivity, or mobility, some packets may also be delayed considerably compared to others on the Internet.
UDP datagrams can be reordered, resulting in them arriving at the receiver in a different order from when they were transmitted. Datagram ordering must be restored by the applications that require it.
A lot of computer games and video conferencing use UDP. In addition to allowing packets to be dropped, the protocol also enables packets to be received in a different order than they were sent, making the protocol more efficient.
Monitoring application performance with Atatus
Atatus assists to Identify and fix problems with your web and back-end apps using our full-stack monitoring. Utilize unified monitoring to identify performance bottlenecks and optimize your app for the best user experience.
With application monitoring, you can optimize your application. With full-stack monitoring tools, eliminate errors by instrumenting, analyzing, troubleshooting, and rectifying them.
Ensure that users have a seamless experience. Observe the performance of your applications and relate them to business outcomes using full-stack observability.
With synthetic monitoring, you can track the availability of TCP connections that is established on the given hosts and also ensure the availability of any services living on TCP ports.
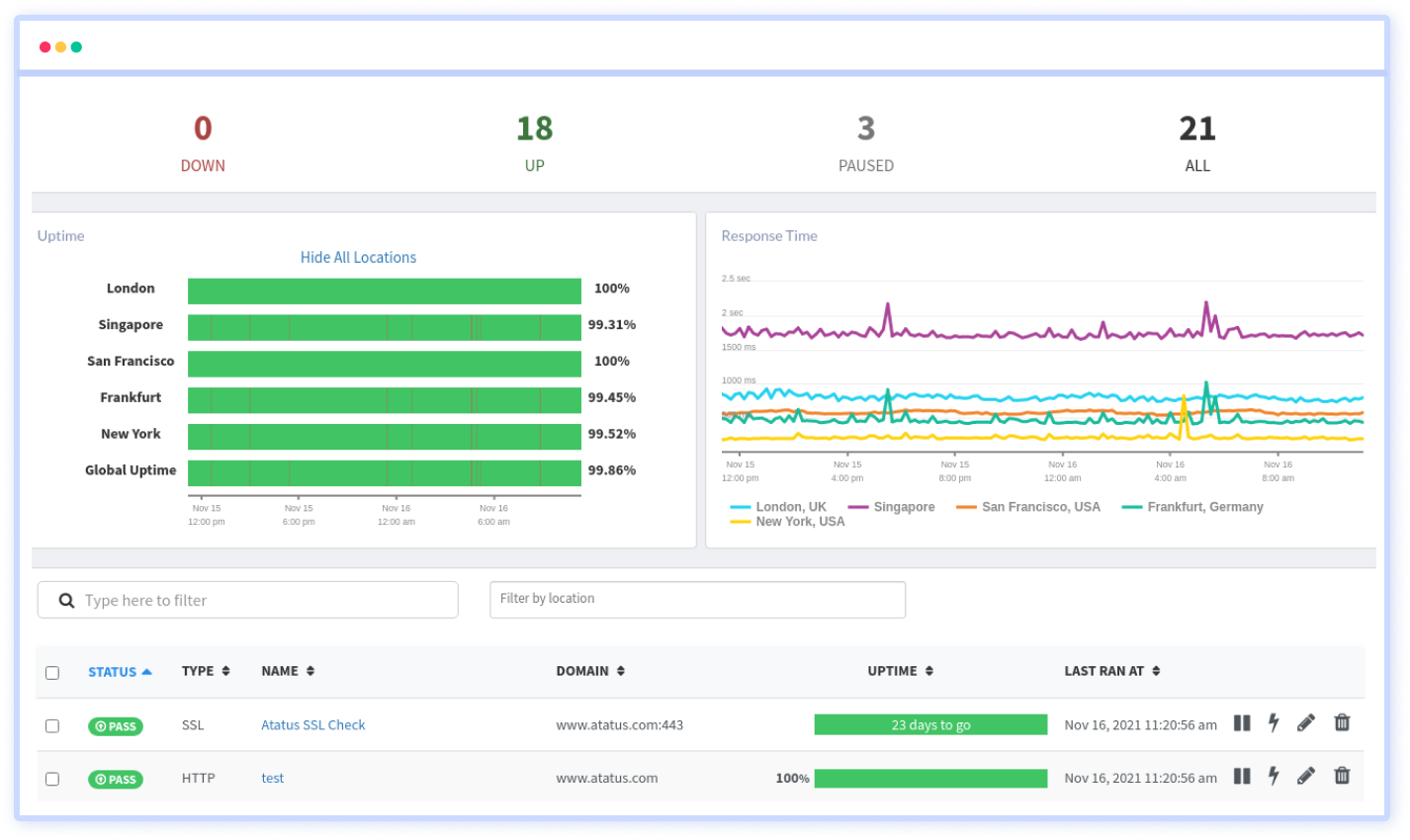
Interested in actionable data? Take advantage of the 14-day free trial of Atatus!
#1 Solution for Logs, Traces & Metrics
APM
Kubernetes
Logs
Synthetics
RUM
Serverless
Security
More