What is Transmission Control Protocol (TCP) and How it works?
The Transmission Control Protocol provides reliable, ordered and, sometimes, time-sensitive data flow between applications across a network. As well as economizes network use by attempting to improve error-handling capability and providing reliable data transmission.
The Transmission Control Protocol is the underlying communication protocol for a wide variety of applications, including web servers and websites, email applications, FTP and peer-to-peer apps.
TCP stands for "Transmission Control Protocol" or "Transmission Control Program". It is used to establish an end-to-end connection between two hosts on the Internet.
In simple terms, it is a reliable method of data flowing or transferring over long distances using specialised packets which are themselves bulk data moving between computers.
- What is Transmission Control Protocol(TCP)?
- How TCP connection works?
- TCP header structure
- Vulnerabilities Of TCP-DDOS And Mitigation Methods
What is Transmission Control Protocol(TCP)?
Transmission Control Protocol, abbreviated TCP, is a protocol in the Internet Protocol Suite used to facilitate computer-to-computer connections on the internet.
This communication is achieved by employing logical connections called sockets, sometimes referred to as endpoints, that are managed by Internet software such as telnet, web browser or e-mail client.
Each socket has an associated port number and a hostname/IP address combination which we use to identify it.
The hostname/IP combination acts as a street address and then you “speak” over the postal service with the IP number on top of the envelope.
This is similar in concept to the telephone service where when you dial various numbers, you are speaking into the switchboard over your telephone line via the telephone company switching system.
How TCP connection works?
Establishing a TCP connection requires that both the client and server participate in what is known as a three-way handshake.
Here's how it works:
1. The client sends a packet to the server, which responds with an acknowledgement (ACK). This shows that the client's request was received correctly.
2. The client sends another packet to the server, which responds with a window update (WINDOW UPDATE). This shows that the server has received enough data from the client and is ready to start sending data back to it .
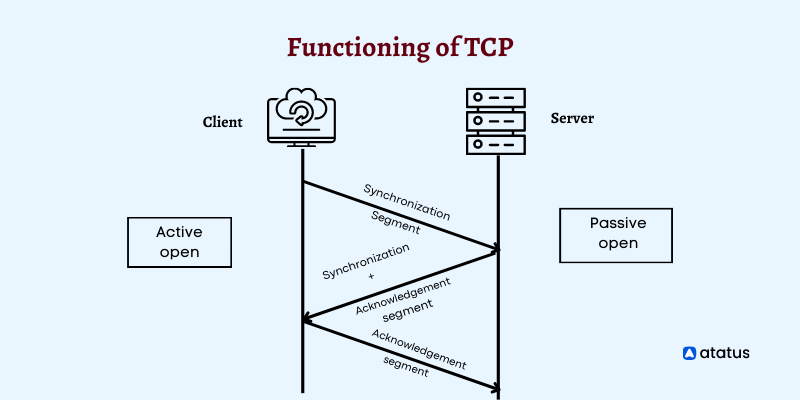
3. The client sends another packet to the server, which responds with an acknowledgement of receipt (RST), indicating that it does not want more data from this connection.
If this packet were not sent by the client, then its partner would close down that connection; however, because there was at least one ACK before this RST packet arrived, there was no reason for terminating the connection.
4. The client sends another packet to the server, which responds with an acknowledgement of receipt (RST), indicating that it does not want more data from this connection.
TCP header structure
The transmission control protocol (TCP) is a communications protocol that allows applications to send data to the Internet.
The 10 TCP header fields are:
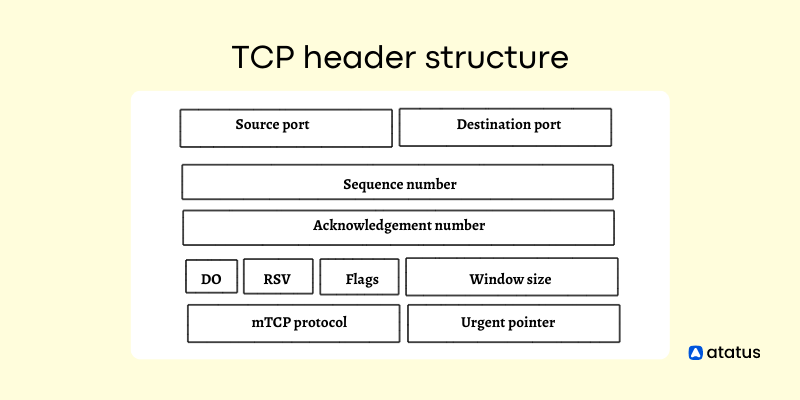
- Source port – The source port number from which this segment of data was received and counted from the beginning of the connection. This field can be used to differentiate between multiple connections to a single destination host.
- Destination port – The destination port number for this segment of data and counted from the beginning of the connection.
- Acknowledgement number - A single-byte value that increments for each successfully delivered data packet and decrements for each unsuccessfully delivered data packet.
- Data Offset - The byte offset in the current segment where the data begins. This field can be used by applications to determine their offset relative to the beginning of the segment.
- Urgent pointer - A 32-bit value that points to the next urgent pointer or window on this connection. Urgent pointers are used by applications to time out connections when no more data can be transferred without losing control of its bits or stream buffer or window size.
- Sequence number – A non-zero value that increments with each new segment sent on that connection and provides ordering information for reassembly and acknowledgement processing.
- Reserved fields - These fields are reserved for system use but can be set by user applications as needed.
- Control flags - Control flags are used to control various aspects of transmission processing including flow control, window scaling, other parameters related to congestion avoidance, or other functions as necessary.
- Window size - This is a numeric value that indicates how much data should be sent before an acknowledgement is returned (the window size).
- mTCP protocol - There are three optional data fields in it they are maximum segment size (MSS), selective acknowledgements (SACK), and window scaling (WS).
Vulnerabilities Of TCP-DDOS And Mitigation Methods
The Transmission Control Protocol (TCP) is connection-oriented. TCP offers reliable delivery of data packets, but it does not guarantee that packets will arrive in the same order as those sent.
TCP is vulnerable to several types of DDoS attacks, including:
i.) SYN flood: This type of attack floods the target with SYN packets. The target responds by sending an SYN/ACK packet back to the attacker, which causes an ACK storm that overwhelms the server's resources and causes it to crash.
The SYN flood is a denial-of-service attack that involves sending SYN packets to a server port in an attempt to complete a connection before the server has had time to process all of its open connections.
The attacker may also send multiple requests for the same port number, which can exhaust resources and prevent legitimate clients from connecting.
Methods for Mitigation are as follows in detail;
a.) Micro-blocks - The server allocates a micro-record in its memory for each SYN request instead of a complete connection object, thus reducing potential resource strain from too many requests.
b.) SYN cookies - The server uses cryptographic hashing to verify a TCP request before allocating memory.
c.) RST cookies - The server intentionally sends an incorrect response after the initial SYN request. If the client is legitimate, the server receives an RST packet, telling the server something is wrong.
d.) TCP stack tweaking - You can decrease the timeout for releasing memory allocated to a connection, or selectively drop incoming connections.
For these types of attacks to be mitigated, network resources should be scaled up on-demand, such as through cloud application / solutions.
ii.) STOMP DDoS attack: During this type of attack, attackers send multiple requests for information from a target. The target responds with acknowledgements, which causes multiple requests from each IP address trying to establish connections with the server.
iii.) Teardrop DDoS attack: During this type of attack, attackers send fragmented packets with a large payload size that are designed to cause congestion on a specific port or set of ports on the target system.
This type of attack involves sending so many packets that they cannot be processed by the target. The target has to discard some packets or wait for other hosts to process them before it can send new ones.
Synopsize
TCP is the protocol that handles HTTP traffic in web browsers. TCP is used to transfer data between two hosts on a network, but it's also used by other applications like email clients, instant messaging and file sharing.
TCP is one of the core protocols of the internet protocol suite. It originated in the initial network implementation in which it complemented the Internet Protocol (IP), and thus the entire suite is commonly referred to as TCP/IP.
TCP provides reliable, ordered, and error-checked delivery of a stream of octets between applications running on hosts communicating via an Internet Protocol (IP) network.
Major Internet applications such as the World Wide Web, email, remote administration, and file transfer rely on TCP.
TCP is a connection-oriented protocol. It has several features that make it suitable for applications that require a reliable data transfer.
TCP uses port numbers to identify a specific application process on a host. TCP is used in many applications and is the standard transmission protocol on the Internet.
Enrich your website with Atatus
Synthetic monitoring of Atatus will ensure the website or application is available.With an intuitive dashboard, you can discover specific and actionable insights into the speed and function of your application right away.
Ensure that your website is performing well and identify the potential bottlenecks in your application. Boost problematic transactions with Atatus metrics.
Regularly check the DNS records of your domains and servers for changes or outages that might indicate malicious attacks. Monitoring your website's connection speed and loading time will allow you to determine when your site is available.
Be sure that your website doesn't go down, so monitor HTTP, DNS, servers, SSL certificates, and TCP to ensure your customers aren't experiencing errors.
Ensure that you monitor your website for errors and fix them so that they can be accessed by your users 24/7. Boost your website by using Atatus and also get a 14days free trial today!
#1 Solution for Logs, Traces & Metrics
APM
Kubernetes
Logs
Synthetics
RUM
Serverless
Security
More