Personally Identifiable Information (PII) - A Beginner's Guide
PII stand for Personally Identifiable Information, so protecting Personally Identifiable Information (PII) is a top priority for companies small and large, as well as government agencies.
Companies are amassing increasing amounts of data on their employees, customers, and partners, making PII security more important than ever. It's critical to understand what PII is and how to protect it.
Personal information can be divided into two categories:
- Personally Identifiable Information is any information that can be used to identify an individual. Instances of PII include social security numbers, credit card numbers, passport numbers and driver's license numbers; passwords (for websites or services); phone numbers; biometric data such as fingerprints and handwriting samples.
If a person’s name is not included with this information but allows for the identification of an individual (i.e., age/birth date), then it may still be considered personal information. - Personally Identifying User Information (PIUI), allows someone to access online services without needing to login each time they visit that service because their login details are stored locally on their computer or mobile device when they first sign up for an account with a company like Amazon so that when they return later on there is no need for them inputting all those details again.
Table Of Contents
- What is Personally Identifiable Information (PII)?
- Who is responsible for safeguarding PII?
- Creating a Data Privacy Framework
- Protection of PII
What is Personally Identifiable Information (PII)?
In the context of data security, PII refers to any information that can be used to distinguish one person from another and can be used for de-anonymizing anonymous data. Any information that could potentially be used to identify a particular person is considered PII.
Personally Identifiable Information (PII) is any data that could potentially be used to identify a particular person.
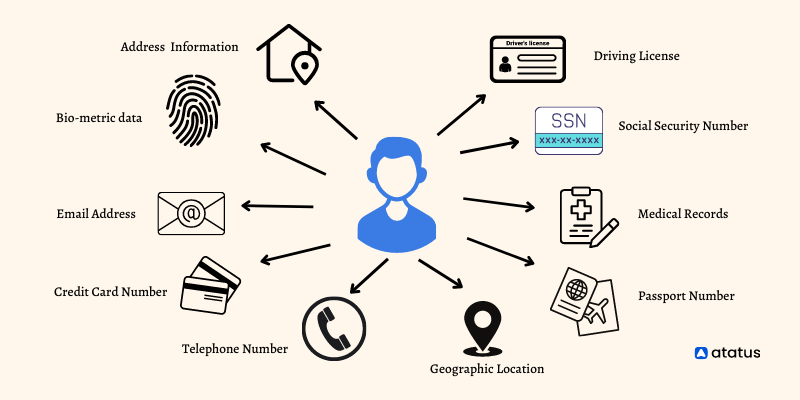
An individual's PII may be utilised solely or in combination with other proper data to identify them and may include direct identifiers, such as Driving licence information.
This can be used to identify them individually, as well as quasi-identifiers, such as ethnicity, that can be combined with other quasi-identifiers, such as their birth date, to determine whether a person is actually the owner of the card.
PII data is not limited to just a name and social security number; it also includes things like your email address, IP address, phone number, username and password information, biometric data (e.g., fingerprints recognition characteristics) as well as other types of unique identifiers like:
- Device IDs (e.g., MAC addresses)
- Location tracking information (e.g., GPS coordinates)
Who is responsible for safeguarding PII?
The answer to this question depends on who owns the PII. If you own the PII, then you are responsible for protecting it. If you are collecting PII from others, then you have a responsibility to protect it as well.
Ultimately, it is up to the individual to decide who they want to share their PII with and how they want it to be protected.
Organizations that collect and store PII are responsible for ensuring PII security and must take steps to protect it from unauthorized access.

This includes implementing security measures like encryption, access control, and data destruction. PII should also be classified according to its sensitivity, and only authorized individuals should have access to it.
The responsibility of safeguarding PII is shared between the data owner and the data processor. The data owner is responsible for protecting PII and must determine how to do so.
The data processor also has a responsibility to protect PII in its possession, but only if it has been provided with this information by a client (or other entity) who owns or controls that information.
As such, when you're working with someone else's personal information, you should make sure they understand their responsibilities towards it as well and vice versa. This will help ensure your company's PII compliance with GDPR while keeping everyone safe!
Creating a Data Privacy Framework
Several concepts exist in the Data Privacy Framework, which can help businesses protect sensitive data like payment details, personal information, and intellectual property.
Specifically, it describes in detail how sensitive data should be defined, how risks affecting the data should be analyzed, and what controls should be in place to protect such data.
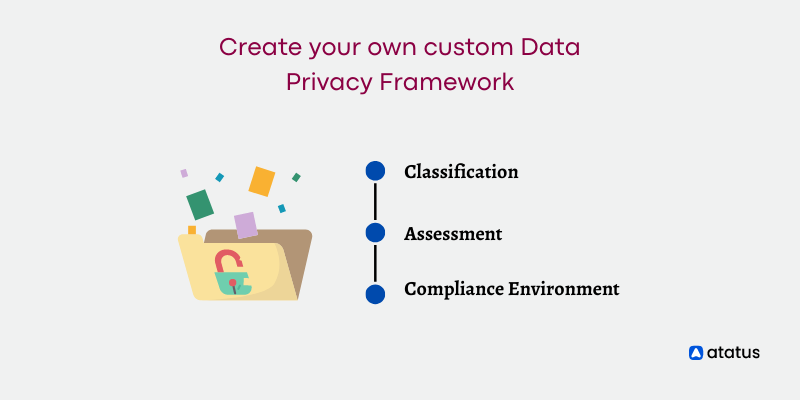
To create your own custom Data Privacy Framework, follow these steps:
- Classification - Classification is the process of identifying what data should be classified as PII and how it should be protected and secure PII.
This can include things like names, social security numbers (SSNs), physical or email addresses, or even credit card numbers. - Assessment -An assessment is a test that determines whether a specific environment has any PII vulnerabilities in it or not.
If there are any vulnerabilities, then you'll need to take action to resolve them before moving forward with your Data Privacy Framework implementation plan. - Compliance Environment - To determine if you're compliant with current regulations regarding data privacy, such as the GDPR or CCPA (California Consumer Privacy Act).
You'll need an audit trail for each piece of information that's processed by your company to prove compliance records were kept correctly throughout its lifecycle at all times during normal operations as well as during crisis events involving breaches/losses etc...
This also helps ensure accountability among employees who access sensitive information because they know they're being monitored closely while doing so which keeps everyone honest about their actions within their workplace environment at all times without fail.
Protection of PII
To protect PII, we need centralized control, access controls, threat detection, encryption, and data masking.
The first step to protecting PII is centralized control. Centralized control ensures that the data is accessed only by authorized people and not shared with unauthorized parties.
Additionally, it helps you track who has access to the data and where it's being stored. Once you've ensured that only authorized users have access to your data, you need to monitor for any threats against your PII.
Threats can be internal (such as an employee accessing information they shouldn't) or external (such as hackers breaking into your systems). The best way to detect threats is through threat detection software that scans networks constantly looking for malicious activity.
Encryption protects data from hackers by encrypting it so they cannot read its contents without the right key or password.
Encryption works on an entire disk, drive partition, folder or file in one of two ways: symmetric encryption uses a single key that both encrypts and decrypts information; asymmetric encryption uses two different keys; one used for encryption and another used for decryption.
Wrap-Up
As you can see, PII data is a serious issue that needs to be addressed as quickly as possible. Fortunately, there are many technologies available today that can help mitigate the risks associated with PII data by reducing exposure to such information and ensuring that only authorized personnel to have access to it.
It’s important to protect PII data because the severity of a security breach involving PII data can lead to serious damages for a company or individual.
Protecting PII is an important part of running your business. If your business is found to have stored or shared PII without following the laws that require you to do so, you could be found guilty of a crime.
PII is everywhere. It’s on your social media profiles, it’s buried in your search history, and it’s floating around in your email inbox. And as we’ve learned recently, it’s also on your credit card.
Monitor Your Website Availability 24/7 with Atatus
Test the availability of the website or application through synthetic (uptime) monitoring of Atatus. Get definite and actionable insights into the speed and function of your application instantly with an intuitive dashboard.
Test how well your site works and identify the potential performance bottlenecks in your application to achieve high performance. Discover Atatus' metrics and optimize problematic transactions.
Monitor and measure the connection speed and browser load time of your website to make sure it is accessible.
Monitoring the availability of specific ports, such as HTTP, SSL, TCP and ICMP, from different locations at set intervals.
Get started with free 14-day trial!
#1 Solution for Logs, Traces & Metrics
APM
Kubernetes
Logs
Synthetics
RUM
Serverless
Security
More