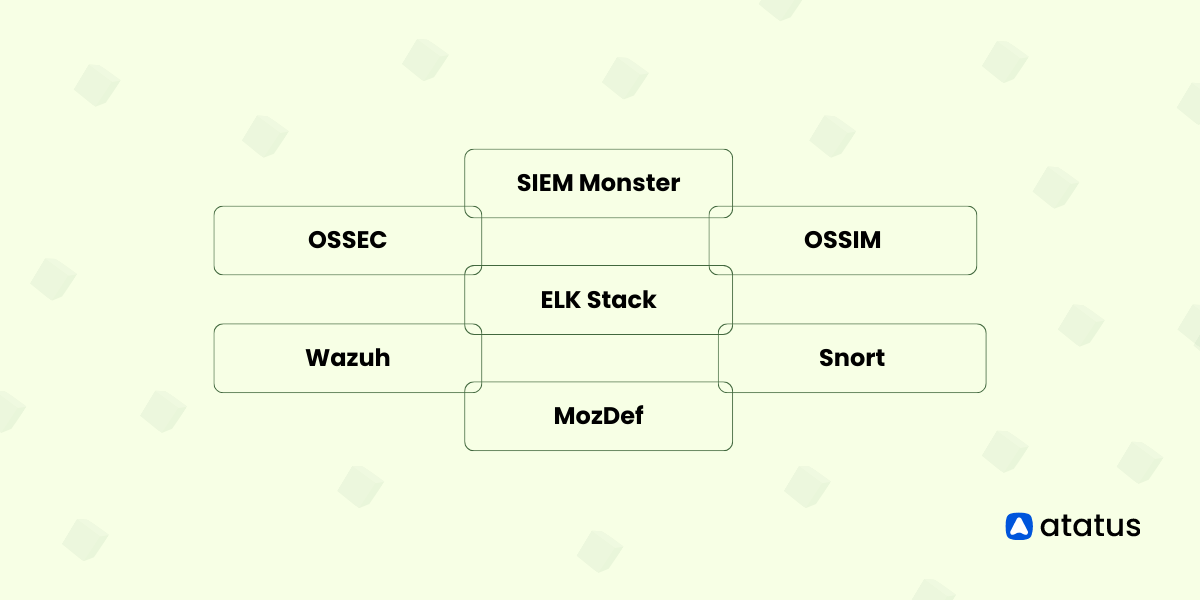
Top Open Source SIEM Tools
In the fast-paced world of cyber security, organizations face a challenging task to safeguard their digital assets from a variety of advanced threats. Security Information and Event Management (SIEM) tools have emerged as a vital solution, empowering businesses to detect, respond to, and mitigate security incidents effectively.
SIEM tools, also known as Security Information and Event Management tools, are powerful software solutions designed to assist organizations in managing and securing their digital environments. The purpose of SIEM tools is to collect, analyse, and correlate security event data from various sources within an organization's network infrastructure, such as logs, network traffic, and system events.
SIEM, at its core, serves as the eyes and ears of an organization's digital infrastructure. It aggregates vast volumes of logs, network traffic, and system events, breaking them down into information that can be used to take action. This allows security teams to identify anomalies, detect threats in real-time, and swiftly respond to incidents.
Additionally, open-source SIEM tools embrace flexibility, enabling customization to meet specific organizational requirements and seamlessly integrate with existing security infrastructure.
In this blog, we will delve into the depths of different open-source SIEM tools, exploring its capabilities, use cases, and the unique advantages offered by open-source solutions.
Before getting into this just check What SIEM is in this blog post.
Lets get started!
1. ELK Stack
The ELK Stack, consisting of Elasticsearch, Logstash, and Kibana, is an open-source software suite utilized for log management, real-time analytics, and data visualization. Let's break down the components of the ELK Stack and understand their individual roles,
Elasticsearch is a distributed search and analytics engine designed to handle large volumes of structured and unstructured data.
Logstash is a data processing pipeline that collects, transforms, and enriches data from various sources before sending it to Elasticsearch.
Kibana is a web-based data visualization tool that allows users to explore and analyse data stored in Elasticsearch through interactive dashboards, charts, and graphs.
With its broad adoption across log analysis, security monitoring, application performance monitoring, and business intelligence, the ELK Stack offers flexibility and extensibility through its open-source nature.
Key Features
- Log Collection: Gathers and consolidates logs from diverse sources like servers, network devices, and security appliances for comprehensive monitoring.
- Log Parsing and Enrichment: Analyzes and enriches log data with contextual information (e.g., geolocation, user details, threat intelligence) to enhance analysis capabilities.
- Real-time Log Analysis: Enables immediate analysis of log data to promptly detect and respond to security events and anomalies.
- Alerting and Notifications: Generates alerts and notifications based on predefined rules and thresholds to notify security teams of potential threats or incidents.
- Correlation and Threat Detection: Performs log correlation and pattern matching to identify complex attack scenarios and detect advanced threats.
- Dashboards and Visualization: Offers interactive dashboards and visualizations to present security metrics, trends, and insights for effective monitoring and analysis.
- Compliance and Reporting: Supports compliance requirements by generating reports and audit trails aligned with predefined standards and regulations.
- User and Entity Behavior Analytics (UEBA): Utilizes machine learning algorithms and behavioral analytics to identify anomalous user behavior and potential insider threats.
- Incident Response: Facilitates incident response workflows by providing access to log data and analysis tools for investigation and mitigation.
2. OSSEC
OSSEC, which stands for Open Source Security, is a powerful open-source SIEM tool designed to monitor and analyse security events in real-time. It provides a comprehensive solution for threat detection, incident response, log analysis, and compliance management. OSSEC is highly customizable and can be tailored to meet the specific needs of different environments.
Positive Outcomes
- OSSEC helps you meet regulatory compliance requirements by monitoring security controls and events, assisting with standards like PCI-DSS, HIPAA, and GDPR.
- It can automatically respond to security incidents by blocking IP addresses or disabling accounts, reducing the need for manual intervention and improving incident response time.
- OSSEC uses advanced techniques to identify unauthorized access attempts, system compromises, or malware infections, protecting your systems from threats.
- It keeps track of critical files and alerts you if any unauthorized modifications or tampering occur, ensuring the integrity of your system.
- It quickly notifies you when it detects suspicious activities or security breaches, allowing you to respond swiftly and minimize the impact.
3. Wazuh
Wazuh SIEM simplifies cybersecurity by offering a robust set of features that help monitor, detect, and respond to potential security threats.
With its log analysis, real-time alerts, threat detection capabilities, compliance monitoring, and incident response features, Wazuh SIEM empowers organizations to proactively protect their systems and networks. let us see some of the key features of Wazuh in short.
Key Features
- Vulnerability Detection: Wazuh includes vulnerability detection capabilities that help organizations identify security weaknesses in their systems. By proactively detecting vulnerabilities, organizations can prioritize and implement necessary patches or configuration changes to mitigate potential risks.
- File Integrity Monitoring: Wazuh offers File Integrity Monitoring (FIM), which involves monitoring critical files and directories for unauthorized changes. FIM alerts organizations to potential security breaches, malware infections, or unauthorized tampering, allowing them to take swift action to investigate and remediate such incidents.
- Regulatory Compliance: By using Wazuh, organizations can streamline their compliance management processes and generate audit-ready reports when required. Wazuh provides built-in rulesets and capabilities to assist with regulatory compliance requirements, such as PCI DSS, HIPAA, GDPR, and more.
- Cloud Security: As organizations increasingly adopt cloud environments, ensuring the security of cloud assets becomes paramount. Wazuh supports cloud security by integrating with popular cloud platforms, such as Amazon Web Services (AWS), Microsoft Azure, and Google Cloud Platform (GCP).
- Log Data Analysis: One of the core functionalities of Wazuh is log data analysis. It collects and analyzes logs from various sources, including operating systems, applications, and network devices. Wazuh's log analysis capabilities enable organizations to gain insights into security events, system behaviour, user activities, and potential threats.
4. Snort
Snort SIEM is a user-friendly and powerful tool that enables beginners in cybersecurity to enhance their defence` system. By incorporating Snort SIEM into your cybersecurity, one can fortify their systems and networks against a wide range of cyber attacks, making it an invaluable tool for safeguarding ones digital assets.
One of the great things about Snort SIEM is that it can be customized to fit your specific needs. You can adjust its settings, create your own detection rules, and configure the alerts to match your organization's security requirements.
Key Features
- Intrusion Detection and Prevention - Snort excels in real-time intrusion detection and prevention by analysing network traffic, identifying and blocking potential security threats.
- Scalability and Flexibility - Snort is highly scalable and can be deployed in various network environments, from small networks to large enterprise setups. It can handle high traffic volumes and adapt to diverse network architectures.
- Integration with Other Tools - Snort can integrate with other security tools and systems, such as SIEM platforms, firewalls, and log management systems. This interoperability allows for centralized monitoring, better correlation of security events, and enhanced incident response capabilities.
5. AlienVault OSSIM
AlienVault OSSIM was developed by a team of engineers who recognized the lack of available open-source security information and event management (SIEM) products that adequately addressed the needs of security professionals. Their aim was to create a feature-rich solution that offers event collection, normalization, and correlation functionalities.
The engineers understood that a SIEM, regardless of being open source or commercial, is only valuable if it provides comprehensive security visibility. Thus, AlienVault OSSIM was designed to address this reality and provide security professionals with a robust open-source SIEM tool that meets their requirements for enhanced security visibility and management.
By now, it is expected that you have gained a clearer understanding of open-source SIEM tools. Whether you are a small business or a large enterprise, open-source SIEM tools are worth considering to enhance your security posture and effectively protect your valuable assets.
They provide the essential capabilities required to collect, analyse, and respond to security events, all while being flexible and customizable to fit specific needs. With their cost-effectiveness, flexibility, and customizability, these tools provide essential security capabilities while empowering organizations to adapt and tailor the solution to their specific needs.
Key Features
- Asset Discovery: OSSIM performs active and passive network scanning to identify and inventory assets on the network, providing visibility into the network infrastructure and devices.
- Vulnerability Assessment: OSSIM integrates with vulnerability scanning tools like OpenVAS to identify and assess vulnerabilities in network devices, servers, and applications, helping prioritize remediation efforts.
- Intrusion Detection: With the inclusion of Suricata, OSSIM offers real-time detection and alerting on network-based attacks and intrusions, enhancing the security posture of the network.
- Behavioral Monitoring: OSSIM incorporates behavioral monitoring capabilities to detect anomalous patterns of activity or deviations from normal behavior, enabling early detection of potential threats.
- SIEM Event Correlation: OSSIM performs event correlation, analyzing logs and events from multiple sources to identify patterns, relationships, and potential security incidents, enabling effective incident response and threat detection.
6. Security Onion
Security Onion is an open-source Security Information and Event Management (SIEM) tool. It integrates various security tools into a unified platform to provide comprehensive network security monitoring and analysis.
Key Features
- Intrusion Detection System (IDS): Security Onion incorporates the powerful IDS engine Suricata, which detects and alerts on malicious activities and network intrusions.
- Network Security Monitoring (NSM): It enables full packet capture and analysis, allowing deep inspection of network traffic for detecting threats and investigating incidents.
- Log Management: Security Onion collects and centrally manages logs from various sources, including network devices, operating systems, and applications. This enables comprehensive log analysis and correlation.
- Threat Intelligence Integration: It supports integration with various threat intelligence feeds, allowing the identification of known malicious IP addresses, domains, and other indicators of compromise.
- Visualization and Analysis: Security Onion provides intuitive dashboards and visualizations to help security analysts analyze network traffic, identify patterns, and investigate security events effectively.
- Incident Response: It assists in incident response by providing a centralized platform for monitoring and investigating security incidents, allowing security teams to take immediate action.
7. SIEM Monster
SIEM Monster is a powerful Security Information and Event Management (SIEM) solution that provides comprehensive cybersecurity monitoring and threat detection capabilities.
Key Features
- Real-time log analysis and event correlation
- Centralized management of security data for easy access and analysis
- Integration with advanced threat intelligence sources to stay ahead of emerging threats
- Customizable dashboards and reports for tailored visibility into security events
- Automated incident response and threat mitigation to streamline security operations
- Compliance management tools to ensure adherence to regulatory requirements
SIEM Monster empowers organizations to proactively identify and respond to potential threats, enhance their security posture, and maintain regulatory compliance.
8. MozDef
MozDef, developed by Mozilla, is an open-source security incident response platform aimed at assisting organizations in efficiently managing and responding to security incidents in a well-coordinated manner.
Key Features
- Incident management: Centralized platform for managing security incidents.
- Security orchestration and automation: Integrates with various security tools for automated workflows.
- Integration with existing tools: Seamless integration with SIEMs, IDS/IPS, and more.
- Event correlation and analysis: Identifies patterns and detects anomalies.
- Playbook-driven response: Predefined actions for efficient incident response.
- Alert management and triage: Prioritize and manage security alerts effectively.
- Reporting and metrics: Generate metrics for performance measurement and improvement.
- Extensibility: Customizable and supports additional tool integration.
- Community support: Active community for knowledge sharing and development.
Points to Remember
- SIEM tools provide centralized monitoring, analysis, and management of security events.
- They collect and aggregate log data from various sources for comprehensive visibility.
- Real-time monitoring enables immediate detection and response to security incidents.
- Advanced correlation algorithms identify patterns and relationships within security event data.
- Integration with threat intelligence enhances detection capabilities.
- SIEM tools streamline incident response and workflow management.
- Compliance requirements can be met with pre-built reports and dashboards.
- User and Entity Behaviour Analytics (UEBA) detects abnormal behaviour and insider threats.
- Scalability and performance are crucial for handling large volumes of data.
- SIEM tools continually evolve to keep up with emerging threats and changing security landscapes.
Conclusion
To conclude, open source SIEM tools are a great alternative for organizations that need to manage security events and logs without breaking the bank.
The open source community provides a lot of excellent options, each with its own set of features and benefits. From Elastic Stack to OSSEC, SIEM tools discussed above are feature-rich and offer a wide range of use cases, from log management and correlation to real-time monitoring and incident response.
It's important to consider the specific needs of your organization and choose the right open source SIEM tool that fits those needs. By leveraging the benefits of open-source technology, organizations can better secure their networks and data while reducing costs and increasing flexibility.
Monitor Your Entire Application with Atatus
Atatus is a Full Stack Observability Platform that lets you review problems as if they happened in your application. Instead of guessing why errors happen or asking users for screenshots and log dumps, Atatus lets you replay the session to quickly understand what went wrong.
We offer Application Performance Monitoring, Real User Monitoring, Serverless Monitoring, Logs Monitoring, Synthetic Monitoring, Uptime Monitoring, and API Analytics. It works perfectly with any application, regardless of framework, and has plugins.

Atatus can be beneficial to your business, which provides a comprehensive view of your application, including how it works, where performance bottlenecks exist, which users are most impacted, and which errors break your code for your frontend, backend, and infrastructure.
If you are not yet an Atatus customer, you can sign up for a 14-day free trial.
#1 Solution for Logs, Traces & Metrics
APM
Kubernetes
Logs
Synthetics
RUM
Serverless
Security
More