IP Blacklisting: Your Beginner's Guide
IP Blacklists contain ranges of or individual IP addresses you want to block. A blacklist can be used in combination with firewalls, intrusion prevention systems (IPS), and other traffic filtering tools.
With the recent developments in cyber security, organizations are increasingly relying on IP blacklisting to protect their networks.
Blacklists enable administrators and infrastructure professionals to block unwanted attempts to intrude into internal systems and networks
These lists can also be used for creating whitelists of approved addresses. Also commonly used to block spam, viruses and other malicious traffic.
Table of Contents
- IP Blacklisting - Introduction
- Various kinds of Blacklists
- IP Blacklisting in action
- Why do IP addresses exist?
- Obstacles of IP Blacklisting
- Requisite for an IP Blacklist
IP Blacklisting - Introduction
IP blacklisting is the act of blocking any device that connects to a network using an IP address.
It can be done by an individual user or by a security system that monitors and blocks unwanted connections.
IP addresses are used to identify computers on the internet, and they are assigned automatically when you connect to a network. They are also referred to as MAC addresses (Media Access Control).
Various kinds of Blacklists
Blacklists work by comparing an incoming IP address against a database of IP addresses that have been identified as being malicious.
If the IP address matches one in the database, access is denied. The most common types of blacklists are:
i.) DNS blacklists – These lists are maintained by DNS resolvers and contain public domain names that have been flagged as malicious or illegal. They’re usually used on shared web hosting services to prevent abuse by customers.
ii.) IPv4 blacklists – These lists are maintained by ISPs and contain IPv4 addresses that have been flagged as malicious or illegal. They’re usually used on shared web hosting services to prevent abuse by customers.
IP Blacklisting in action
IP blacklisting is a method of blocking access to an IP address by adding it to a list of banned addresses.
The list is then distributed to routers worldwide, which prevents users with the banned IP address from accessing the Internet.
The process of adding an IP address to a blacklist can be done manually or automatically.
Manual methods allow the user to see who uses the blocked IP address and when they accessed it.
Automatic methods can block any activity from that IP address without requiring user intervention.
The most common way for blacklists to work is by having all web traffic pass through a centralized server that manages all incoming requests and directs them accordingly.
This makes it easy for website owners or ISPs to block unwanted traffic without having to worry about individual computers being infected with viruses or malware.Here, if you blacklist an IP address that belongs to China, you might not want your users accessing anything in China. Including Facebook and Google, even if they are legal in China.
Why do IP addresses exist?
An internet protocol (IP) address is a unique identifier for devices connected to the Internet.
Your home router uses an external IP address provided by your ISP so that it can connect to other devices on the Internet through its connection to your broadband modem.
When you browse the web, your computer will send packets of data over a connection between two hosts; one host being your device and another being the server hosting the website you're visiting.
Each packet contains information such as where it came from and where it's going, along with other details like which port it's using for communication (port 80 is used for HTTP connections).
All of this information is contained in a header within each packet of data sent over the network.
There are two fundamental ways that you can use IP addresses:
- Whitelists — These are lists of approved IP addresses that are allowed through your firewall or router.
- Blacklists — These are lists of denied IP addresses that aren't allowed through your firewall or router.
Obstacles of IP Blacklisting
It's a common misconception that IP blacklisting is a perfect security mechanism.
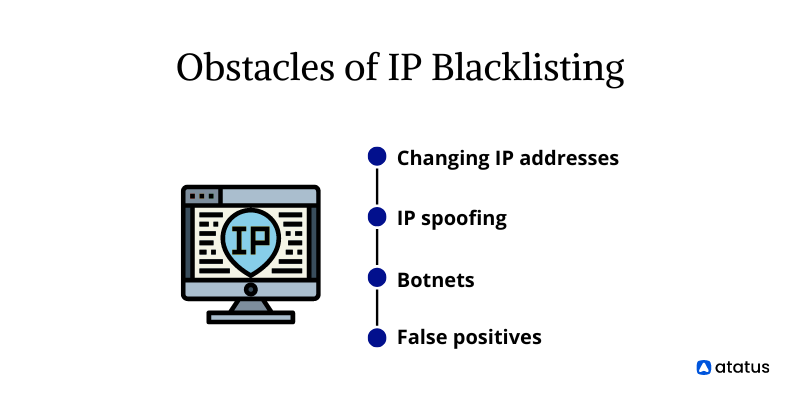
In fact, the challenges of IP blacklisting include:
Changing IP Addresses
One of the biggest challenges of IP blacklisting is dealing with new IP addresses. Companies can be hit with an IP address ban for a variety of reasons, and it's important to understand how these bans work.
A common example is if you're using a VPN, or if you're using an open proxy or TOR network.
When this happens, your current IP address will be banned from accessing certain websites.
However, if you use another VPN or proxy, it will allow you access again.
This means that if your business has been hit by an IP address ban, all it takes is changing your current IP address in order to get around it.
IP Spoofing
IP spoofing is a technique used by hackers to hide their real origin and make it appear like they're coming from a different location.
Hackers often use this technique to avoid detection or hide their malicious activities from law enforcement agencies.
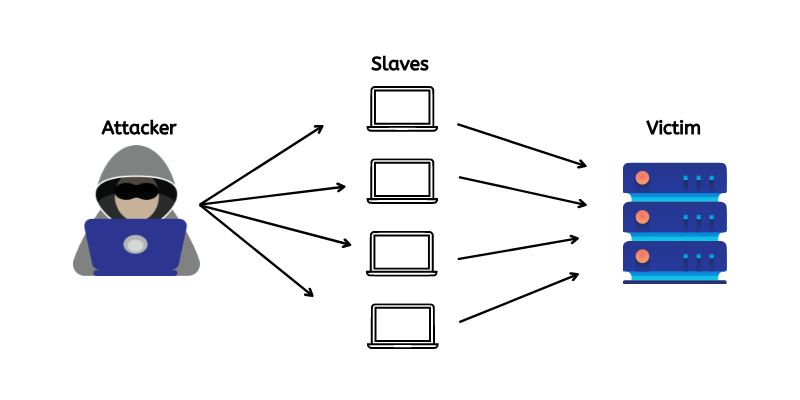
Botnets
Botnets are networks of infected computers used as proxies for cyberattacks. Hackers typically install malware on systems and then try to hide the malware's activity by using botnets.
In some cases, this can be achieved by changing the source IP address of infected systems in such a way that they appear to be coming from different locations or even countries.
False Positives
False positives refer to false alarms triggered by legitimate activity on the part of users or systems within your network as opposed to malicious behaviour.
This can result in wasted resources when you needlessly blacklist IP addresses that aren't actually involved in attacks or other malicious activity against your organization's assets.
Requisite for an IP Blacklist
The purpose of an IP blacklist is to prevent your website from being visited by malicious bots, such as spammers, hackers, scrapers and other unwanted visitors.
There are many reasons why you may want to use an IP blacklist:
- Preventing DDoS attacks – DDoS attacks are becoming more common as hackers gain access to more powerful tools. An IP blacklist can help protect your site from these attacks by blocking malicious IP addresses before they even reach your servers.
- Protecting your servers – An IP blacklist can also prevent other types of attacks from reaching your servers, such as SQL injection and XSS attacks. These types of attacks allow hackers to take control over parts of your site or database and steal user data or other sensitive information.
Wind-Up
A blacklist is a list that includes IP addresses of external clients that you want to ban from your network. Simply, blacklists take effect faster, and more effectively than proxy servers.
They can also be free if you are willing to set up the server-side software yourself and maintain it. Their only drawback is that they don't (generally) apply to HTTPS traffic.
At the end of the day, using good blacklisting practices can prepare you for the worst and ensure that malicious threats don't sneak into your network undetected.
Their effectiveness depends on how well you configure them. Configuring the right IP blacklisting solution is a matter of priority.
Monitor Web Performance With Real User Monitoring
The real-user monitoring solution allows you to gain full-stack visibility into the poorly performing front-end code of your website.
In order to ensure that you are getting some actionable insights from the real data that affects your customers, you can filter Bots, Domains, IPs, User Agents, and many other configurations.
It monitors the end-user experience and imparts real-time feedback on what the user is perceiving. Implement Real User Monitoring to resolve performance issues on the front-end.
The best way to fix poor end-user performance is to identify and fix the complex frontend issues that arise due to slow page loads, route changes, static assets not being retrieved, poor XMLHttpRequest, JS errors, and more.
When you are employing Atatus, you can find out which pages are not loading correctly or how long it takes for a page to load. You can also check errors that have been generated.
Atatus is a full-stack observability platform that provides a one-stop solution for all of your application monitoring needs.
It provides an inclusive set of monitoring tools that covers all necessary indicators, including server performance, backend bottlenecks, and log analytics.
#1 Solution for Logs, Traces & Metrics
APM
Kubernetes
Logs
Synthetics
RUM
Serverless
Security
More