Filebeat vs. Logstash: A Quick Comparison
When it comes to managing logs in a distributed environment, two popular open-source tools come to mind: Filebeat and Logstash. While both tools have similar goals, there are significant differences in their functionality and usage.
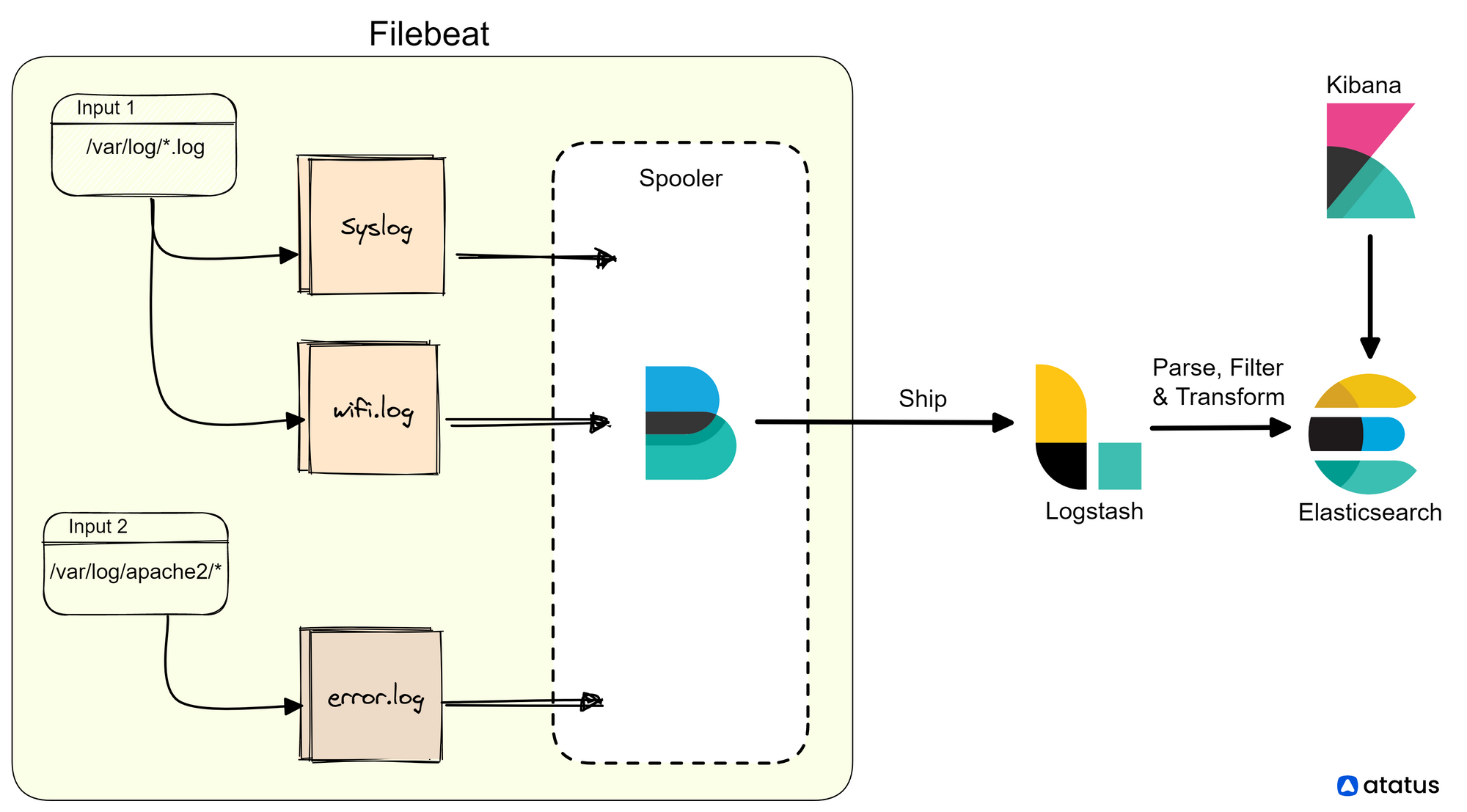
Filebeat is a lightweight log shipper that collects, parses, and forwards logs to various outputs, including Elasticsearch, Logstash, and Kafka. Filebeat has a small memory footprint and is designed to be fast and efficient, making it ideal for collecting and forwarding logs from multiple sources across a distributed environment.
It supports various input sources, including files, syslog, and Beats protocols. Filebeat can also be configured to apply filters to the log data before forwarding it to an output destination.
Logstash, on the other hand, is a more comprehensive data processing pipeline that can handle a wide range of data types, including logs, metrics, and events. Logstash provides a flexible architecture that enables you to parse, transform, and enrich data from a wide range of sources, including databases, message queues, and APIs.
It also supports a large number of input sources, including files, syslog, and various network protocols. Logstash also provides a broad range of output destinations, including Elasticsearch, Redis, and Kafka. It also includes powerful filters and plugins for data processing, such as grok patterns and date filters.
Table of Content
Beginning of Logstash
Logstash was developed by Elastic, the same company which developed Elasticsearch and Kibana. It was first released in 2012 and has since become one of the market's most popular open-source data processing pipelines.
The idea behind Logstash was to provide a flexible, scalable, and easy-to-use tool for processing and transforming data from various sources - logs, metrics, and events. Logstash was designed to be a key component of the ELK stack, along with Elasticsearch and Kibana, which together provide a comprehensive solution for log management and analytics.
Logstash provides a wide range of input sources, including files, syslog, TCP/UDP, and various network protocols. It also includes a broad range of output destinations, including Elasticsearch, Kafka, and Redis, among others. Data processing can be automated with the help of Logstash filters, plugins, and grok patterns, which provide a rich set of filters, date filters, and geolocations for processing data.
Logstash's flexibility and scalability have made it a popular choice for teams of all sizes and industries. Its open-source nature also means that it has a vibrant community of users and contributors, who have contributed to its development and growth over the years.
Since its initial release, Logstash has undergone numerous updates and improvements, adding new features and capabilities, such as support for new input sources, output destinations, and filters. Elastic has continued to optimize Logstash's performance and efficiency, making it even more powerful and versatile.
However, like any other software, you may encounter some problems while using Logstash. Logstash can be resource-intensive and may consume a lot of memory and CPU. If your Logstash instance is slow, you can try increasing the heap size or reducing the number of plugins.
Configuration can be complex and challenging to troubleshoot. You may encounter issues with the input, filter, or output plugins. It is recommended to validate your configuration using the --config.test_and_exit option before starting Logstash.
Today, Logstash is widely used by companies and organizations around the world to process and transform their data, enabling them to gain valuable insights and make better-informed decisions.
How Filebeats developed?
Filebeat was also developed by Elastic. Elastic was founded in 2012 and is based in Mountain View, California.
The idea behind Filebeat was to provide a lightweight, efficient, and easy-to-use log shipper that could collect, parse, and forward logs to various outputs, including Elasticsearch, Logstash, and Kafka. The goal was to create a tool that could be deployed across a distributed environment, allowing teams to collect logs from various sources, including servers, containers, and cloud-based services.
Filebeat was first released in 2015, and since then, it has become one of the most popular log shippers in the market. It has a simple and intuitive configuration system that allows users to set up log collection and forwarding quickly and easily.
Filebeat supports various input sources, including files, syslog, and Beats protocols, and can apply filters to the log data before forwarding it to an output destination. It is also highly scalable and can be deployed across a large number of servers and containers.
Over time, Elastic has continued to develop and improve Filebeat, adding new features and capabilities, such as support for modules, which are pre-built configurations for collecting and processing logs from popular services and applications, including Apache, Nginx, and MySQL. Elastic has also added support for new output destinations, such as Kafka and AWS S3, and has continued to optimize Filebeat's performance and efficiency.
Today, Filebeat is widely used by companies and organizations around the world to manage their logs and gain valuable insights into their applications and infrastructure. Its popularity is due in part to its ease of use, efficiency, and flexibility, making it an excellent choice for teams of all sizes and industries.
Filebeat vs. Logstash
1. Filebeat vs. Logstash: Methods of Collecting Log Data
Filebeat uses various input plugins to collect log data from different sources, including log files, system metrics, and network data. It then sends the data directly to Elasticsearch or Logstash for further processing. Filebeat is designed to be lightweight and efficient, so it can collect and forward log data with minimal resource usage.
Logstash, on the other hand, uses input plugins to collect data from various sources, including log files, message queues, and APIs. It then processes the data through various filters and sends it to an output destination, such as Elasticsearch or a file. Logstash is a more versatile tool that can handle complex data processing and transformation tasks.
2. Filebeat vs. Logstash: How They Handle Data Processing
Filebeat is primarily designed to collect and forward log data, so it has limited data processing capabilities. It can enrich data by adding metadata or fields, but it does not have advanced filtering or transformation features.
Logstash, on the other hand, is designed for complex data processing and transformation tasks. It has a wide range of filters that can manipulate and transform data, including grok, mutate, and geoip. Logstash also supports conditional processing, which allows you to route data based on specific conditions.
3. Filebeat vs. Logstash: Plugins and Integrations
Both Filebeat and Logstash have a wide range of plugins and integrations that can extend their functionality. Filebeat supports input plugins for different data sources, as well as output plugins for different destinations. It also has several other types of plugins, such as processors and modules.
Logstash has a similar plugin architecture, with input, filter, and output plugins that can be combined to perform complex data processing tasks. Logstash also has several pre-built integrations with popular data sources and destinations, such as AWS S3 and Kafka.
4. Filebeat vs. Logstash: Performance and Scalability
Filebeat is designed to be lightweight and efficient, so it has a lower resource usage than Logstash. It can handle a high volume of log data without impacting system performance. Filebeat also supports load balancing and failover to ensure that data is collected and forwarded even in high-traffic environments.
Logstash has more advanced data processing capabilities, but it requires more resources to run. It can be configured to scale horizontally to handle high volumes of data, but this can impact performance and require more hardware resources. Logstash also supports load balancing and failover to ensure high availability in large-scale deployments.
5. Filebeat vs. Logstash: Monitoring Metrics
Monitoring Capabilities and Metrics Offered by Filebeat:
a.) Internal Monitoring Metrics: Filebeat provides built-in monitoring metrics to track its performance. These metrics include:
- Events Rate: Shows the rate at which events are read from input sources and sent to the outputs.
- Harvester Metrics: Tracks the status of log harvester instances, including open and closed files, states, and errors.
- Pipeline Metrics: Monitors the events' journey through different processing stages of Filebeat's pipeline.
b.) Elasticsearch Output Metrics: When Filebeat sends log data directly to Elasticsearch, it can capture metrics related to the output connection, such as bulk indexing duration and request/response status.
c.) Monitoring API: Filebeat exposes an API to retrieve various metrics and statistics, which can be integrated with monitoring and alerting systems.
Monitoring Capabilities and Metrics Offered by Logstash:
a.) Node Metrics: Logstash provides detailed node-level metrics, including JVM statistics, pipeline events, memory usage, and load average.
b.) Pipeline Metrics: Logstash offers metrics related to each pipeline configured, showing event rates, processing times, and number of inputs, filters, and outputs.
c.) Plugin Metrics: Logstash captures metrics specific to various input, filter, and output plugins, enabling users to monitor the performance of individual components.
d.) Monitoring API: Logstash exposes a monitoring API that provides access to internal metrics, pipeline statistics, and node information, making it easy to integrate with monitoring systems.
Typical use cases
Let's explore some specific use cases where Filebeat or Logstash would be the better choice:
Use Filebeat when:
- Log Shipping: If you need to collect and ship log files from multiple sources to a centralized location, Filebeat is a lightweight and efficient option. For example, if you have an application running on multiple servers, and you want to gather the application logs from each server and send them to Elasticsearch for analysis, Filebeat can handle this task effectively.
- Parsing Log Lines: When you have straightforward log parsing requirements and need to extract data based on predefined patterns, Filebeat is a good fit. For instance, if you have Apache web server logs and want to extract specific fields like the client IP, request URL, or response status, Filebeat can tail the log files, extract the relevant information, and send it to a target destination like Elasticsearch or Logstash.
- Log Collection from Standard Inputs: Filebeat supports various standard inputs like syslog, which allows you to collect logs from different sources without much configuration. If you want to gather logs from syslog or other standard sources and forward them to your desired location, Filebeat simplifies this process.
Use Logstash when:
- Complex Log Transformations: If you have logs with unstructured or semi-structured data and need to perform complex transformations, enrichment, or filtering, Logstash's extensive filter plugins make it a suitable choice. For example, if you have JSON logs that need to be parsed, fields extracted, and enriched with additional information before sending to Elasticsearch, Logstash can handle this parsing and transformation efficiently.
- Multiple Data Sources: Logstash is versatile and can handle more than just log files. If you need to ingest data from diverse sources like databases, message queues, APIs, or other external systems, and perform data processing and transformation on this data, Logstash provides the flexibility to handle these sources and apply transformations.
- Advanced Data Processing: When you require advanced data processing capabilities, such as aggregating logs from multiple sources, joining data based on certain criteria, applying conditional logic, or performing data enrichments with lookup tables or external APIs, Logstash's filter plugins and processing pipeline allow you to accomplish these tasks effectively.
Summary
In summary, Filebeat and Logstash are both excellent tools for managing logs in a distributed environment.
Filebeat has a number of excellent features including lightweight, SSL and TLS encryption, a good built-in recovery mechanism, and is one of the most reliable log file shippers today. In most cases, however, it cannot convert your logs into structured log messages that are easy to analyze. It's in this role that Logstash plays a key role.
Filebeat is a lightweight log shipper that collects and forwards logs, while Logstash provides a more comprehensive data processing pipeline for handling a wide range of data types.
The choice between the two depends on your team's specific needs, with Filebeat being a great choice for teams who want a simple and efficient solution for log collection, and Logstash being a better choice for teams who need more advanced data processing capabilities.
Atatus Logs Monitoring and Management
Atatus offers a Logs Monitoring solution which is delivered as a fully managed cloud service with minimal setup at any scale that requires no maintenance. It monitors logs from all of your systems and applications into a centralized and easy-to-navigate user interface, allowing you to troubleshoot faster.
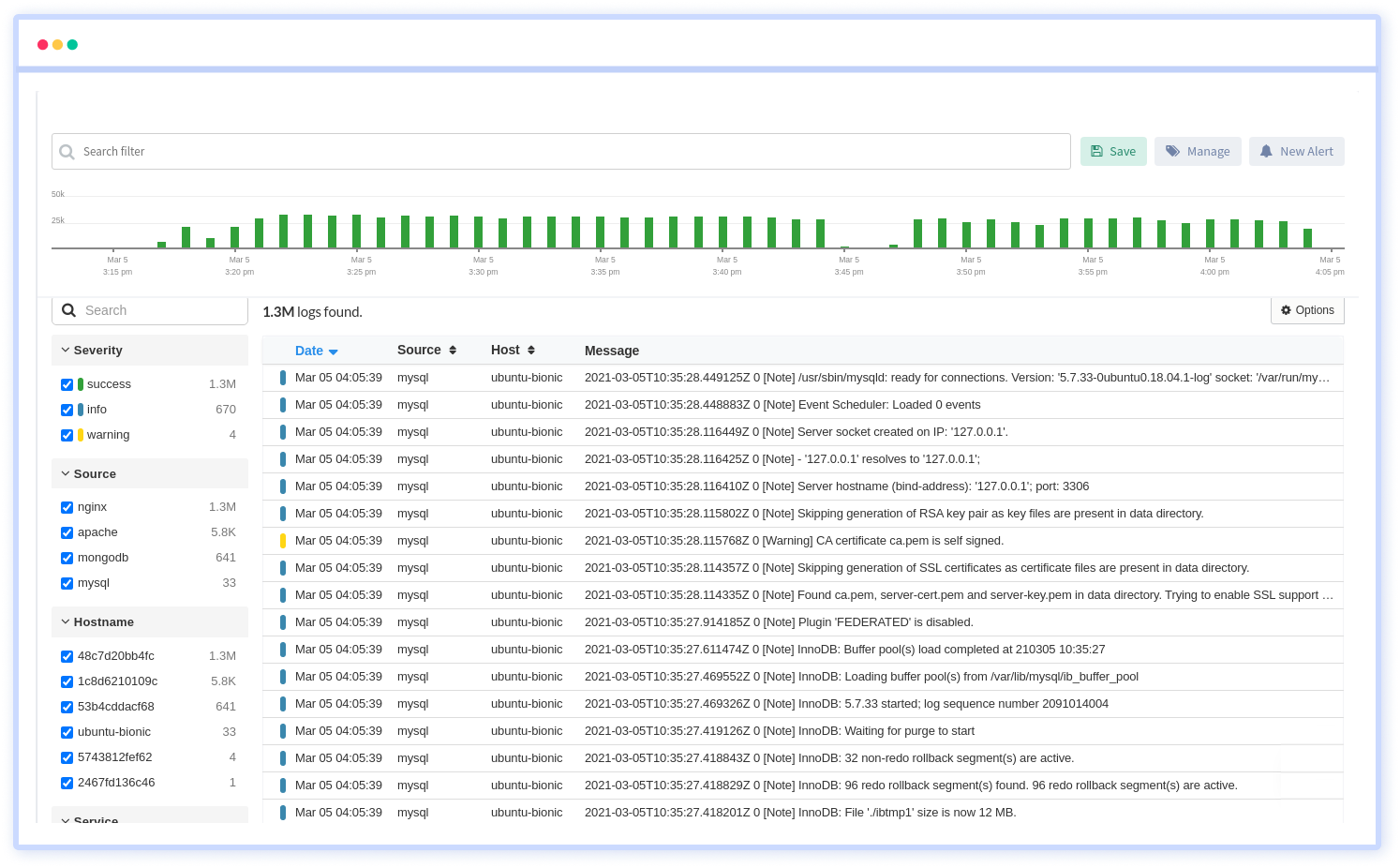
We give a cost-effective, scalable method to centralized logging, so you can obtain total insight across your complex architecture. To cut through the noise and focus on the key events that matter, you can search the logs by hostname, service, source, messages, and more. When you can correlate log events with APM slow traces and errors, troubleshooting becomes easy.
#1 Solution for Logs, Traces & Metrics
APM
Kubernetes
Logs
Synthetics
RUM
Serverless
Security
More