The threat landscape in cybersecurity is changing, and businesses need modern security solutions to keep up. This occurs at a time when corporate operations have shifted dramatically in order to boost access, availability, productivity, and revenues by utilising more cloud resources.
The difficulty for IT has been how to keep track of the security of this complex mix of systems, platforms, applications, and environments while also being able to respond quickly and effectively to threats that have been detected.
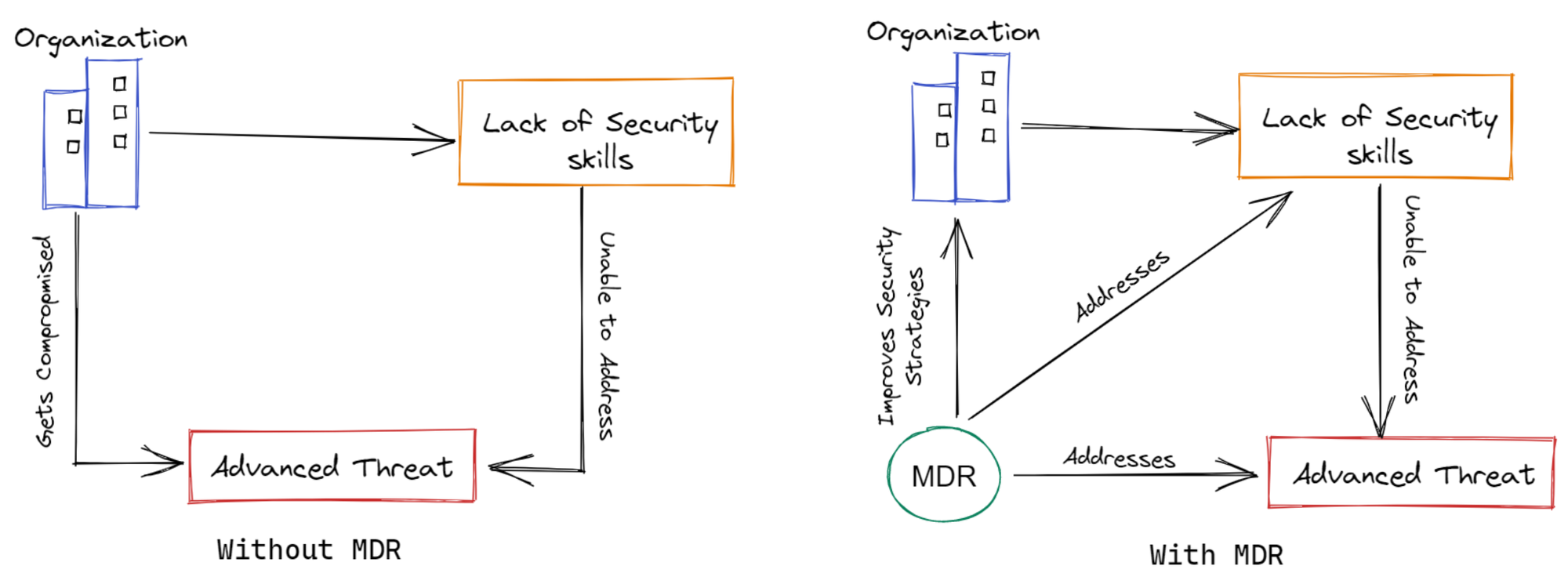
Security service providers have filled the hole with managed detection and response services because organisations have long recognised their limits in terms of staffing and experience to effectively address this rising demand within a security strategy.
We will go over the following:
- What is Managed Detection and Response?
- What is the Origin of the Term MDR?
- How Does MDR Work?
- Benefits of Managed Detection and Response
- Challenges Managed Detection and Response can Solve
What is Managed Detection and Response?
MDR (Managed Detection and Response) is a managed cybersecurity solution that provides enterprises with continuous active monitoring and intelligence-based threat detection, allowing them to respond and remediate attacks fast.
It could comprise a variety of automated technologies that work at both the network and host layers. Threat intelligence and sophisticated analytics are frequently used in conjunction with human incident investigation and response expertise in MDR.
Threat intelligence is meant to detect sophisticated threats on endpoints and the network, and it can be provided by outsourced teams of skilled security analysts to supplement your internal staff and enhance your security solutions. The analyst also collaborates with your team to establish processes and routines that will help with investigation and remediation.
It does more than just strive to stop an ongoing attack; it also works to assure that an organisation will never be harmed by the same cyberattack repeatedly. MDR companies provide a variety of remote response services, such as threat containment and assistance in restoring systems and networks to regular operations.
What is the Origin of the Term MDR?
MDR emerged from Managed Security Service Providers (MSSPs), which previously provided network security management and monitoring but left investigation and remediation to internal IT teams. This shifted the task of detecting serious threats and responding to incidents back to the already overburdened IT team.
One of the most prevalent challenges for internal IT teams is that no one is a cybersecurity expert; your team is mostly made up of generalists with some specialisation. When it comes to detecting and responding to a potential cyberattack, your company requires a professional.

MDR was born as a result.
MSSPs are more concerned with security monitoring and alerting, whereas MDR goes even farther by incorporating detection, response, and threat hunting.
MDR services often employ additional solutions that provide visibility all the way down to the endpoint to ensure a complete picture of any potentially malicious activity. As well as response orchestration to automate remediation, while both include vulnerability scanning and SIEM features.
How Does MDR Work?
MDR monitor, detect and respond to risks in your organisation remotely. The visibility into security events on the endpoint is often provided by an endpoint detection and response (EDR) solution.
Human analysts triage warnings and evaluate the best response to mitigate the effect and risk of positive incidents using relevant threat information, sophisticated analytics, and forensic data. Finally, the threat is eradicated and the impacted endpoint is restored to its pre-infected state using a combination of human and machine skills.
An MDR's key capabilities are as follows:
- Prioritization
Managed prioritisation aids businesses who struggle to sort through their huge volume of notifications on a daily basis to select which to respond to first. Managed prioritising, often known as "managed EDR," uses automated criteria and human inspection to separate benign events and false positives from actual risks. Additional context is added to the results, which are then distilled into a stream of high-quality alerts. - Threat Hunting
Every threat is accompanied by a human who is considering how to avoid being detected by their targets' countermeasures. While machines are intelligent, they are not cunning; a human brain is required to add the element that no automated detection system can. Human threat hunters with vast skills and expertise identify and notify on the most evasive and stealthy dangers, catching what the layers of automated protection missed. - Investigation
Managed investigation services provide additional context to security alerts, allowing enterprises to better identify risks faster. Organizations can gain a better understanding of what happened, when it happened, who was impacted, and how far the attacker proceeded. They can design an effective response based on that data. - Guided Response
Guided response provides concrete recommendations for containing and resolving a given threat. Organizations are counselled on matters ranging from the most basic, such as whether to isolate a system from the network to the most complex, such as how to eliminate a threat or recover from an incident step by step. - Remediation
Recovery is the final step in any incident. The organization's entire endpoint security effort would be wasted if this step is not done properly. By uninstalling malware, clearing the registry, ejecting attackers, and deleting persistence mechanisms, managed remediation returns computers to their pre-attack state. Managed remediation ensures that the network is restored to a known good state, preventing future compromise.
Benefits of Managed Detection and Response
MDR offers a variety of advantages to businesses who want to maintain continuous security monitoring and response:
- Cost-efficient
Building a SOC, hiring seasoned analysts, adopting security solutions, setting response processes, and so on would all cost a small fortune to your business. An MDR service is essentially a monthly operating cost that relieves the effort of establishing and maintaining solutions. There is no way for a company to implement the same level of threat detection and response at a lower cost than with an MDR service. - Eliminate SOC Complexity
Establishing an internal SOC will cost a significant amount of time and money; in many cases, quarters to get up and operating. MDR services include the usage of an existing world-class SOC to meet the organization's SOC requirements. - Access to Security Experts
It's likely that your team lacks skills and experience with threat monitoring, analysis, detection, and response. MDR service providers already have seasoned analysts on staff, providing you with a quick security team to supplement your internal IT team. - Improve Threat Detection and Response
Due to industry-tested security monitoring tools, automatic response orchestration, and up-to-date threat data, prospective threats are handled more accurately and quickly. - Quick Deployment
Deploying MDR services takes weeks instead of quarters when a SOC is already in place.
Challenges Managed Detection and Response can Solve
Many companies find it difficult to implement a comprehensive cybersecurity program owing to a variety of concerns. Many of the issues faced by organisations aiming to improve their security maturity and reduce their cybersecurity risk can be addressed with managed detection and response, including:
- Personnel Limitations
There is a significant talent shortage in the cybersecurity industry, with many more open positions than qualified individuals to fill them. Organizations will find it difficult and costly to fill important security responsibilities internally as a result of this. MDR enables a company to address employment gaps with outside security experts. - Limited Access to Expertise
Organizations struggle to fill specific roles requiring skills such as incident response, cloud security, and malware analysis, in addition to a general lack of cybersecurity competence. MDR enables a business to quickly access external cybersecurity knowledge when it is needed, eliminating the need to hire and retain cybersecurity professionals in-house. - Advanced Threat Identification
Many standard cybersecurity systems are unable to detect advanced persistent threats (APTs) and other skilled crooks. Through proactive threat hunting, MDR enables enterprises to discover and mitigate these risks. - Slow Threat Detection
Many cyber-attacks go unnoticed for long periods of time, increasing the cost and impact on the target company. MDR ensures that the cost paid by an organisation as a result of a cybersecurity event is minimised by providing detection and response times backed by service level agreements (SLAs). - Security Immaturity
MDR allows a business to swiftly develop a sophisticated security program that includes 24/7 threat detection and response, with many of the associated costs shared among the MDR provider's clients. This lowers the total cost of ownership (TCO) of cybersecurity and allows a company to reach a high degree of cybersecurity maturity faster than it could otherwise. - Underlying Security Flaws
Organizations might be exposed to underlying security issues as a result of poor practices. MDR keeps a constant eye on the infrastructure's attack surface, actively looking for threats and previously unknown defects. MDR services assist organisations in identifying and resolving these issues, as well as providing advice on how to do so.
Conclusion
For those organisations that are serious about monitoring and responding to threats and are considering an internal SOC, the path to adopting an MDR service is a clear choice.
An effective MDR will have the appropriate in-house experience to deal with any issue that a customer may face. This comprises a 24-hour security operations centre, incident response teams, and expertise in safeguarding various platforms, such as cloud computing and enterprise endpoint devices.
Your team can only be effective if they have the right tools. Full access into a customer's network, sophisticated data analytics, and the capacity to respond quickly to possible security incidents are all requirements for an MDR provider.
Monitor API Failures with Atatus
Monitoring API failures in production is very hard. You'll need tools like Atatus to figure out which APIs are failing, how often they're failing, and why they're failing.
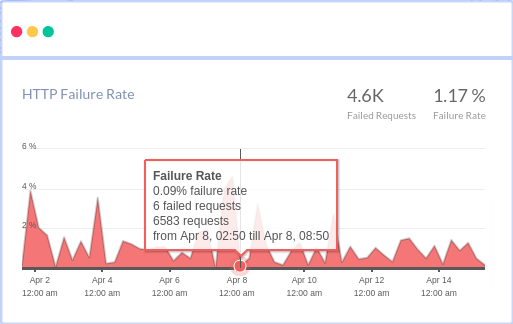
You can see the most common HTTP failures and get detailed information about each request, as well as custom data, to figure out what's causing the failures. You may also view how API failures are broken down by HTTP Status Codes and which end-users have the most impact.




