Keeping up with cybersecurity threats may be difficult, and finding security tools that can help can be even more difficult. Turning the problem over to a managed security services provider (MSSP) is an appealing alternative for some businesses. Managed SIEM (Security Information and Event Management) systems are one approach to do so.
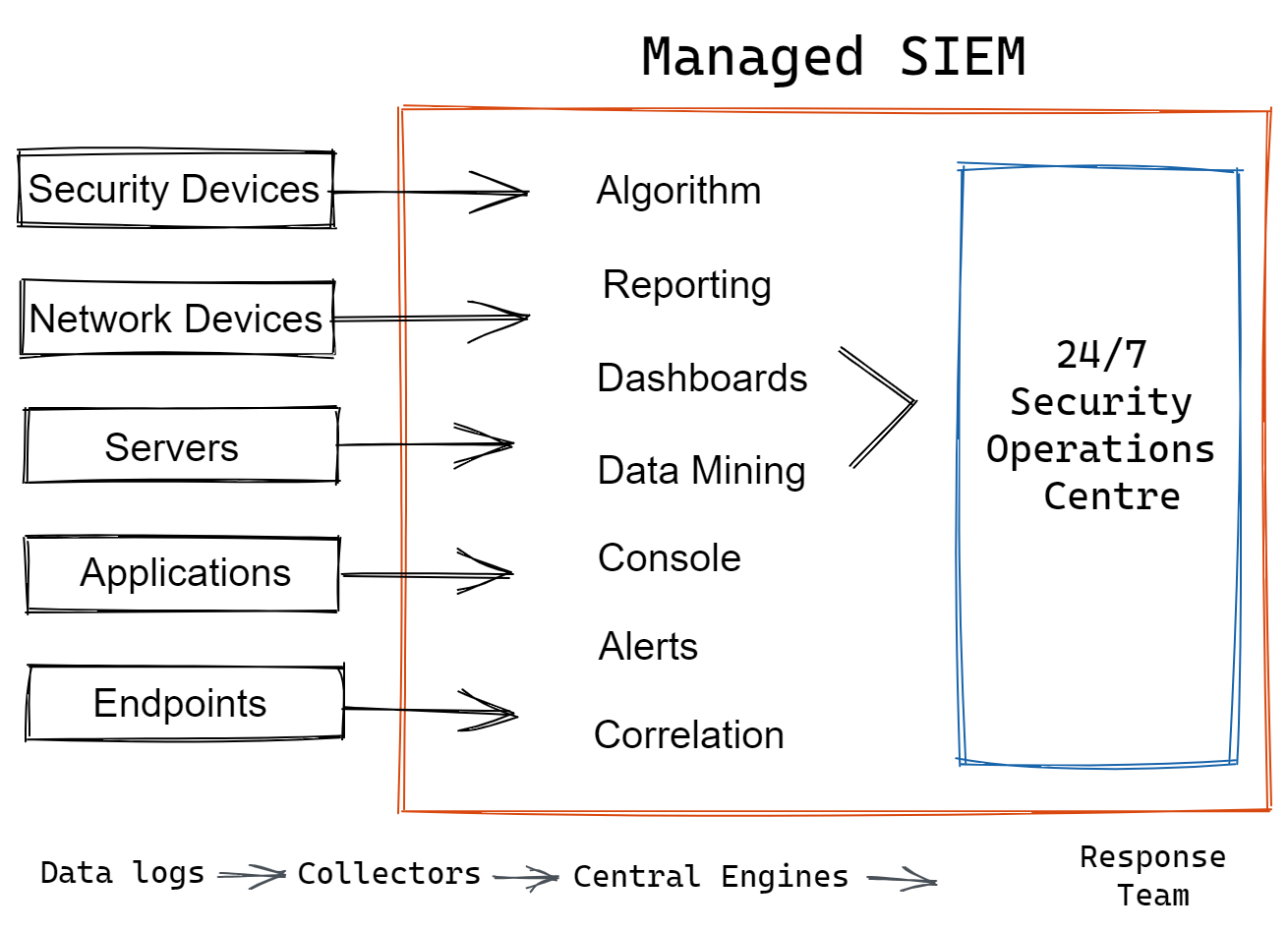
SIEM systems provide a centralised view of IT security by absorbing log and event data from a variety of security tools, hardware, and applications, as well as notifying IT security teams when security threats are detected.
We will cover the following:
- What is Managed SIEM?
- Features of Managed SIEM
- Managed SIEM Benefits
- How to Select SIEM Tool?
- Use Cases for SIEM
- Why Managed SIEM is Important?
What is Managed SIEM?
Businesses across a variety of industries utilise Security Information and Event Management (SIEM) to obtain insight into activity in their IT estate and to detect and respond to possible threats. SIEM software was originally designed to gather, analyse, and report on log data, but it has since grown into a threat management system.
Modern SIEM has more features and can give companies meaningful insights into their infrastructure's risks and vulnerabilities.
Managed SIEM is a service that allows an organisation to hire a third-party service provider to host a SIEM application on their servers and monitor the organization's network for potential security threats instead of deploying, setting up, and monitoring a SIEM software solution on-premise.
Organizations pick Managed SIEM for their corporate security needs because it allows them to deploy faster, save money on setup and training, and make use of cyber security experts' experience.
Features of Managed SIEM
A SIEM solution serves as a log and threat management platform. In order for a SIEM to be effective, it must include the following features:
- Log Aggregation and Management
The log data from systems across the entire organisation should be collected by a SIEM. The SIEM's operations are built on this foundation, which offers critical contextual data for detecting and responding to cybersecurity incidents. - Event Correlation
Most events can be discarded as false positives or valid activities on their own. SIEM solutions correlate many relevant events, allowing cyberattacks to be identified using this aggregated data. - Data Analytics and Machine Learning
The ability to recognise trends and deviations from the norm is required for the detection of cybersecurity issues. A SIEM gathers log data from across the organisation and transforms it into actionable intelligence using data analytics and machine learning techniques. - Centralized Configuration and Management
For security teams, a SIEM solution provides a single pane of the glass user interface. This increases the efficiency of security management and allows for more immediate and effective incident identification and response. - Threat Classification and Triage
All cybersecurity solutions will generate alerts and logs based on their own perspectives. A SIEM collects data, triages warnings, and prioritises them, allowing security specialists to focus on the most significant and immediate risks first.
Managed SIEM Benefits
A SIEM is an important part of a company's cybersecurity infrastructure. Here are the benefits of managed SIEM:
- Expanded Security Team
Many companies are unable to properly staff their security teams due to the current cybersecurity skills shortage. This means that a company might not have the personnel needed to get the most out of its SIEM solution. A managed SIEM gives an organisation access to the qualified personnel it needs to defend its network and systems successfully. - Round-the-Clock Monitoring
Cyberattacks do not occur only during business hours, and network monitoring is required to protect against cyber threats. A managed SIEM provider will have a security operations centre (SOC) that is open every day to ensure that an organization's network is protected at all times. - Specialized Expertise
SIEM solutions, like any other tool, have a learning curve, and analysts may need some time to master the technology. A managed SIEM provider will have cybersecurity professionals on staff who are intimately familiar with the SIEM solution, allowing them to give maximum value and protection to their customers. - Outsourced Configuration and Maintenance
It takes time to deploy, configure, and manage a SIEM solution, and it requires specific cybersecurity knowledge and skills. A managed SIEM supplier will take over these responsibilities and delegate them to professionals. - Low Total Cost of Ownership (TCO)
SIEM solutions can be expensive in terms of hardware/software, licences, and other factors. A managed SIEM provider can spread these costs across its whole client base by utilising multitenancy in its SIEM solution. This allows a company to obtain the same level of security for a fraction of the cost of implementing an in-house solution. - Rapid Deployment
Integration of a SIEM with an organization's overall security architecture can be difficult and time-consuming. A managed SIEM provider will have an onboarding process that allows their SIEM to be integrated and protect the company faster than an in-house solution.
How to Select SIEM Tool?
One of the most critical components of an organization's security architecture is a SIEM solution. When considering SIEM systems, it's critical to keep the following factors in mind:
- Cost
SIEM solutions can cost a lot of money and come with a variety of licence choices (such as standalone hardware versus a service-based model). The best solution is determined by an organization's budget and specific requirements. - Functionality
A SIEM platform should be able to manage logs and threats all in one place. If a SIEM solution lacks the qualities listed above, it won't be able to assist a company's cybersecurity program effectively. - Usability
A security team's tool for managing the organization's cybersecurity is a SIEM platform. As a result, user-friendliness is an important feature of a SIEM solution. - Scalability
SIEMs are tailored to the needs of various companies. A major corporation should utilise a solution tailored to its needs, rather than one created for small or medium-sized organizations. - Integration
A SIEM solution is built to work with an organization's whole security infrastructure. The easier it is to build and implement a SIEM solution, the more out-of-the-box products it can connect to.
Use Cases for SIEM
SIEM solutions have a wide range of applications. They usually include the items on the list below.
- Advanced Threat Protection
Expert-level monitoring for advanced threats is provided by SIEM solutions. Insider threats, unauthorised data exfiltration (massive data transfers are typical of the initial stage of a ransomware attack), and continuous external threats all suggest that cybercriminals are targeting your company. - Compliance & Audit Reporting
Many organisations' operations include compliance management since they must follow the regulations that apply to their industry. IT systems can be made compliant using SIEM tools. Organizations can use SIEM's reporting features to produce audit reports to demonstrate compliance and effective security practices. - Incident Response & Forensics
When an attack is in progress, SIEM solutions identify it and send out an alarm. Some of the tools have features that can help analyse the sort of attack and advise ways to prevent it from advancing. Historical data can be checked for past breaches and reports on what attackers accessed using forensic analysis tools within SIEM. - Security Monitoring
It provides real-time security incident monitoring as well as long-term monitoring over time. SIEM solutions are well-positioned to correlate this information and serve as the hub of an organization's security strategy and posture since they have access to so many data sources. If they have a specialised in-house cyber security staff, some people establish a security operations centre (SOC) around their preferred SIEM solution toolset.
Why Managed SIEM is Important?
Cyber security is becoming more of a worry as the number of high-profile data breaches rises year after year, and even small and medium-sized businesses are realising the importance of protecting their IT assets from external threats. Organizations can opt to set up and monitor an on-premise SIEM tool or contract with a third party for Managed SIEM services when it comes to implementing a SIEM tool.
Organizations engage with a third-party Managed SIEM supplier for a variety of strategic reasons, including:
- Outsourced Security Expertise
The major value driver for managed SIEM vendors is enterprise security. They have a plethora of cyber security expertise that they can use to help their customers improve their IT security. - Reputation
A reputable Managed SIEM service has a track record of effectively setting up and monitoring security tools to protect its clients from cybersecurity threats. Managed SIEM can provide you with the assurance that your company's security is being handled by industry specialists. - Strategic Partnerships
Within the cyber security sector, managed SIEM companies are well-connected, including with other key security technology providers. This provides them with more tools, resources, and expertise, as well as the most recent developments and timely alerts concerning the most recent risks uncovered.
Conclusion
Organizations may get a lot of cyber security capabilities from SIEM solutions. However, with the ever-increasing threat landscape and criminals targeting IT systems, they are not a "install and forget about it" solution. SIEM systems must be managed and tweaked on a regular basis in order to provide appropriate monitoring and defences.
Atatus Log Monitoring and Management
Atatus is delivered as a fully managed cloud service with minimal setup at any scale that requires no maintenance. It monitors logs from all of your systems and applications into a centralized and easy-to-navigate user interface, allowing you to troubleshoot faster.
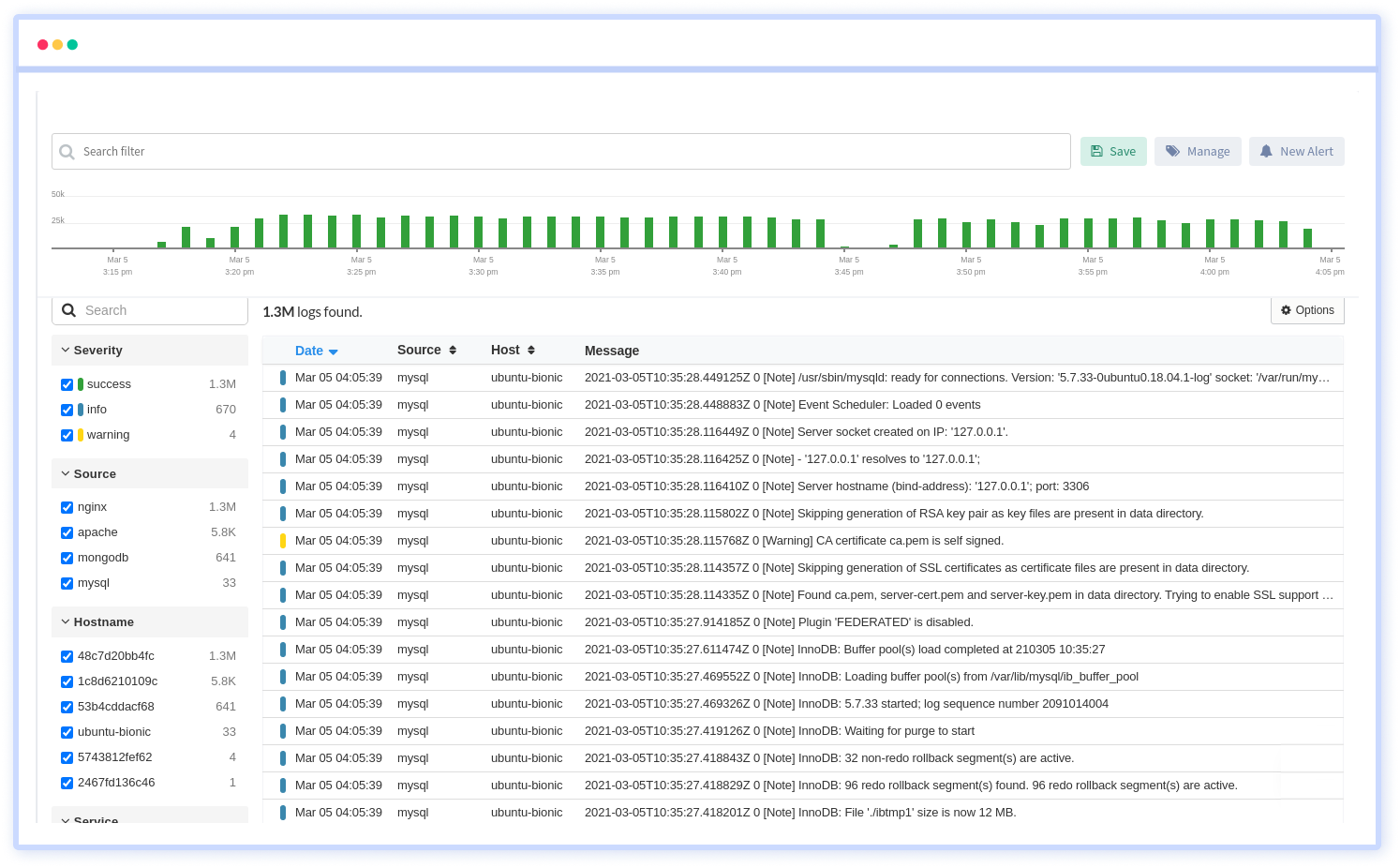
We give a cost-effective, scalable method to centralized logging, so you can obtain total insight across your complex architecture. To cut through the noise and focus on the key events that matter, you can search the logs by hostname, service, source, messages, and more. When you can correlate log events with APM slow traces and errors, troubleshooting becomes easy.





