Data Obfuscation
Data Obfuscation is a way of making data unreadable or unusable if data breach occurs. It is like providing security to the data by encrypting it or masking it in order to make it unreadable even when the hackers can do a successful data breach. Data breaching is very common these days and every organization must protect its own data. Even if we cannot stop the data breach completely, we can save the data we have by means of data obfuscation.
Data obfuscation means either the hacker who has successfully breached our system can see the data, but he will not be able to use it because of the data obfuscation measures we have provided. Let us see the techniques used in data obfuscation.
- Database Obfuscation techniques
- Other techniques
- Importance of Data Obfuscation
- Steps to implement Data Obfuscation
Database Obfuscation techniques
These are all the primary methods to protect our sensitive data from reaching the hands of attackers.
i.) Data Masking:
While the developing team or testing team is working on the real data, they may mess up with the personal information. So, in order to prevent it from happening, the real data is replaced with fake data. In other words, data shuffling happens.
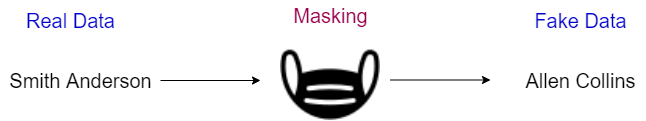
It is the process of replacing the fake version of data with the real one. This fake data can be used by people for software testing or sale demos. So even if the masked data is subject to breaching, there will be no harm since the data provided is completely fake.
ii.) Data Encryption:
Data encryption is the process of encrypting the plain data into an encrypted form so that the hackers won't be able to read it. This encrypted data is very secure, as the third party or hackers will not be able to read until it is decrypted.

The decryption key will be handed over to the receiver by the sender. So the intermediate person who is the hacker, will not be able to decrypt the message. The message will be in encrypted form until it is decrypted by the receiver.
This encrypted data will not be useful for software testing or sale demos since it will not be in the readable format.
iii.) Data Tokenization:
Tokenizing is the process of replacing the data with some meaningless values. This process is irreversible, but still the tokenized data can be mapped back to the original data by the owners.

The organization’s financial transactions like credit card details are very important and they are tokenized to avoid the data being read by the third party or the malicious attackers. In this way, the credit card data is very safe and stays within the organization rather than falling into the hands of hackers.
Other techniques
i.) Data Randomization:
This is the process of randomly juggling the values of the columns in the database. So even if the data is breached, the values will be in a shuffled manner and it will be difficult to arrange it to their respective columns. Even though this technique is not as safe as data encryption or other techniques. But still this technique plays its own role in safeguarding the data from the attackers.
ii.) Nulling:
It is the process of replacing confidential data like credit card details with a digit or code which holds no specific meaning. For example, the credit card number will look like this after nullifying.
####-####-####-1234
iii.) Blurring:
Blurring is nothing but making a slight variance to the numbers in the database so that it is hard to connect them to the real data.
For example, adding 10 days to the existing date in the database. Say the database holds a table describing the date of birth of the employee. By adding 10 days to the date or adding 5 years to the year of birth, the data is now blurred from the real date.
Thus the hacker will not be able to get the real data of birth of the person even if the data breach is successful.
iv.) Substitution:
As the word “Substitution” says, it is merely substituting the value from the real data to a value from the dictionary.
Say if a table holds the first and last names of the users. The last names can be changed by randomly picking names from the dictionary of names available.
Importance of Data Obfuscation
Following are a few of the main reasons why organizations use data obfuscation methods:
i. Protection of personal data:
Let’s say that the organization holds data of the users in a table.
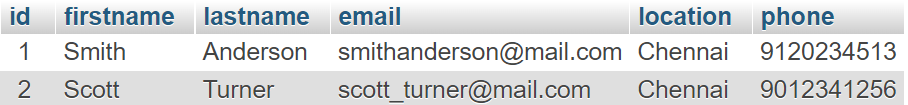
Without data obfuscation, the third party or even the testing or development team who uses the data can clearly see the person’s details without any alteration.
If we apply any data obfuscation technique, the data will look like this.
So, now the data is there but it is replaced with some fake data and it is not usable for the hackers. Even the developers or testers can use this data for their software testing purpose or for sale demos in front of common people.
Since, third-party websites are not trustable, the data must be protected by all means to prevent the personal data being used by attackers.
ii. Compliance:
Compliance means to comply with a wish or command of someone. Here we should follow the compliance provided by the government and other organizations. The compliance is we should not expose or share any kind of information of a particular individual without their permission or consent. There is a regulation called GDPR(General Data Protection Regulation) which is a regulation in the EU law on data protection and privacy. These kinds of compliances exist in other countries too and it is necessary to meet the necessary requirements to protect the data we have.
Steps to implement Data Obfuscation
The following steps are the best ways to implement data obfuscation.
a.) Analysis of data
The first and foremost step toward ensuring our data is protected is to analyze it. Almost all the data should be obfuscated for better security. But analyzing the data gives us an idea about what kind of data we are going to obfuscate.
Some data may have personal information of a person while the other has credit/debit card details of an organization. So analyzing the data is the initial step in the data obfuscation.
b.) Selection of approach
Since there are many kinds of data obfuscation, we should be able to find the appropriate approach for our data. Data encryption encrypts the data where the data is not useful for software testing and all, but data masking, randomization, substitution, and all doesn't make the data go into an unreadable format. So, selecting the correct approach is the next step in data obfuscation.
c.) Implementation
Once the technique is selected, the tools needed to implement the data obfuscation must be selected and made ready. The data obfuscation can even be automated. Thus, the implementation of data obfuscation takes place at the end.
Conclusion
A customer’s trust is based on how their data is safe in the organization’s hands. Data obfuscation provides internal and external protection of data.
Whether the data is used internally between the developers, testers, trainees or the support team, or the data is being shared outside the organization like the credit/debit card details in an e-commerce website, the data is safe by providing necessary data obfuscation techniques.
Since, there are many methods available in data obfuscation, one can easily identify the technique suitable for their organization’s data.
The data breach should be avoided at all costs but even if the hacker is successful in his data breaching and has access to our data we should be able to protect it by masking it with data obfuscation.
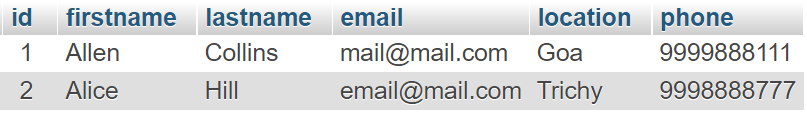
Monitor Your Database with Atatus
Atatus provides you an in-depth perspective of your database performance by uncovering slow database queries that occur within your requests, as well as transaction traces, to give you actionable insights. With normalized queries, you can see a list of all slow SQL calls to see which tables and operations have the most impact, know exactly which function was used and when it was performed, and see if your modifications improve performance over time.
Atatus can be beneficial to your business, which provides a comprehensive view of your application, including how it works, where performance bottlenecks exist, which users are most impacted, and which errors break your code for your frontend, backend, and infrastructure.
#1 Solution for Logs, Traces & Metrics
APM
Kubernetes
Logs
Synthetics
RUM
Serverless
Security
More