The process of locating and analyzing cyber threats is called threat intelligence. Threat intelligence can refer to data gathered about a prospective threat or the method used to collect, analyze, and analyze such data to comprehend risks better. Threat intelligence involves sorting through data, contextually analyzing it to identify issues, and implementing remedies according to the issues identified.
We will go over the following:
- What is Threat Intelligence?
- Why is Threat Intelligence Important?
- Types of Threat Intelligence
- Threat Intelligence Lifecycle
- Benefits of Threat Intelligence
What is Threat Intelligence?
Threat intelligence, commonly referred to as cyber threat intelligence (CTI), is data gathered regarding ongoing or possible attacks against an organization from a variety of sources. The data is subsequently processed, structured, and subjected to analysis to reduce and mitigate cybersecurity threats.
Threat intelligence's primary goal is to highlight to organizations the many threats they face from outside attacks, such as advanced persistent threats (APTs) and zero-day threats.
Threat intelligence provides detailed information and context on individual threats, such as who is attacking, their capabilities and motivations, and the indications of compromise (IOCs). Organizations can use this information to make informed choices on how to defend against the most harmful attacks.
Why is Threat Intelligence Important?
Information that supports decision-making and potentially gives an organization a strategic edge is referred to as intelligence in the military, business, or security context. A larger security intelligence plan includes threat intelligence. It provides details about safeguarding a company from both internal and external dangers, as well as the procedures, guidelines, and equipment employed in data collection and analysis.
A better understanding of the threat landscape and threat actors, as well as the most recent strategies they have employed, is provided through threat intelligence. It helps businesses to actively configure their security policies to recognize and stop sophisticated attacks and zero-day threats. Many of these adjustments can be automated to maintain security's real-time alignment with the most recent intelligence.
Types of Threat Intelligence
Threat intelligence comes in four different types: strategic, tactical, technical, and operational. To create a thorough threat assessment, all four are necessary.
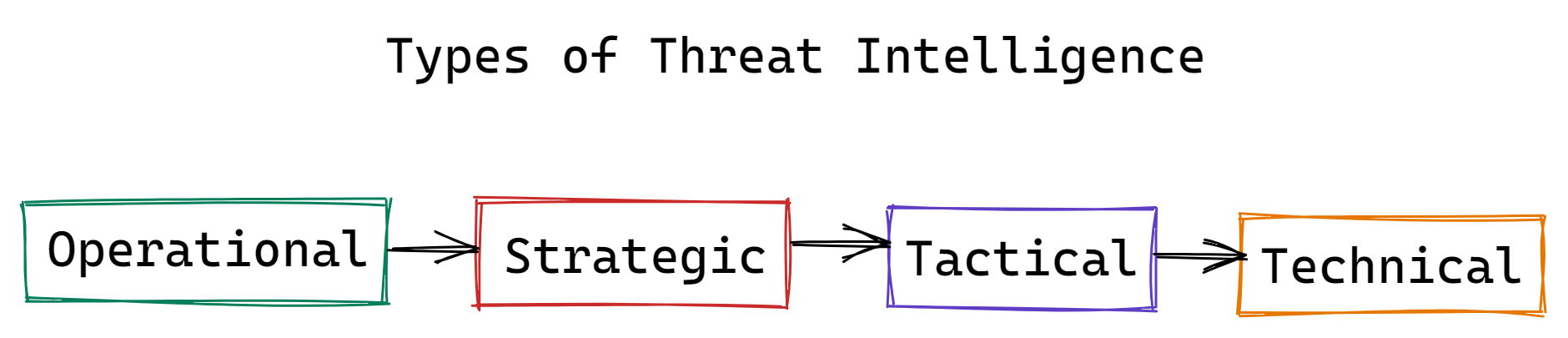
- Operational Threat Intelligence
This method gathers data from several places, such as chat rooms, social media, antivirus logs, and historical occurrences. It is employed to anticipate the type and time of upcoming attacks. Automated processing of millions of data points across many languages is frequently done using data mining and machine learning. Operational intelligence is used by security and incident response teams to modify the settings of some controls, including firewall rules, event detection rules, and access controls. As a result of the information giving a clearer understanding of what to look for, response times can also be improved. - Strategic Threat Intelligence
This analysis summarizes potential cyberattacks and their potential effects on stakeholders, non-technical audiences, and decision-makers. It is based on in-depth analyses of new risks and trends from around the world and is delivered in the form of white papers, reports, and presentations. It is intended to provide a broad perspective of the threat landscape facing a certain sector or company. - Tactical Threat Intelligence
The tactics, techniques, and procedures (TTP) that threat actors employ are disclosed through tactical intelligence. It is designed for people who are directly responsible for protecting IT and data resources. It gives information on the most effective strategies to protect against or reduce attacks and how an organization might be attacked using the most recent techniques. - Technical Threat Intelligence
This information focuses on warning indicators of an impending attack. These warning signals include spear phishing, luring, and social engineering, as well as reconnaissance, weaponization, and delivery. Social engineering attacks can be prevented in large part through technical intelligence. This form of intelligence is sometimes paired with operational threat intelligence, but it is flexible because hackers frequently change their strategies to capitalize on current events and ruses.
Threat Intelligence Lifecycle
Cyber threat intelligence is the result of a six-stage cycle of data gathering, processing, and analysis. Cyber threat intelligence is not the same as raw data. This process is circular because as new questions and knowledge gaps are discovered during the development of intelligence, new collection requirements are established. Iterative and improving over time, an effective intelligence program is iterative.
Before doing anything else, it's essential to identify your use cases and define your objectives to optimize the value of the threat intelligence you provide.
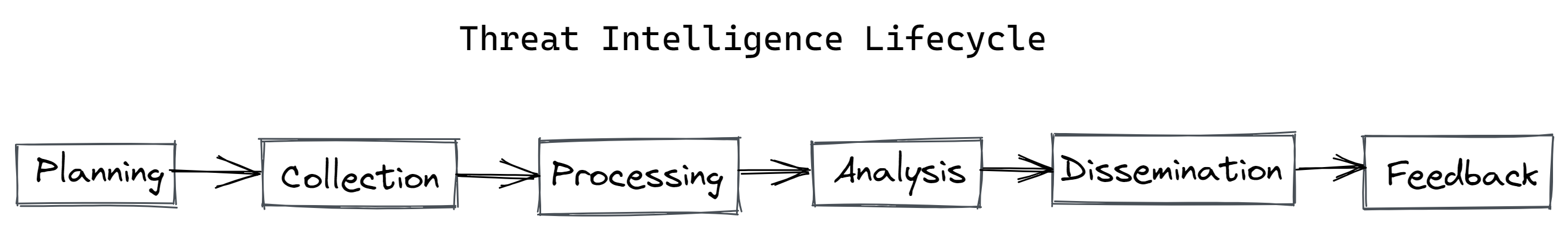
#1 Planning and Direction
Asking the appropriate questions is the first step to generating actionable threat intelligence.
Broad, open-ended questions should typically be avoided since they don't focus on a specific fact, event, or activity, which is what questions that best promote the development of actionable threat intelligence do.
Prioritize your intelligence goals based on things like how closely they conform to the guiding principles of your company, the magnitude of the decision's impact, and the decision's urgency.
Understanding who will use and benefit from the finished product is crucial at this point. Will the intelligence go to a team of technical analysts who require a quick report on a new exploit or to an executive who needs a broad overview of trends to guide their security investment decisions for the upcoming quarter?
#2 Collection
Gathering raw data that satisfies the conditions established in the first stage is the next step. It's best to gather information from a variety of sources, including technical sources, the open web, the dark web, and internal sources like network event logs and records of previous incident responses.
Threat information, which is typically thought of as lists of IoCs, can also include vulnerability information, which might include customer PHI, raw code from paste sites, and text from news sources or social media. IoCs include malicious IP addresses, domains, and file hashes.
#3 Processing
Once all the raw data has been gathered, it needs to be sorted by removing duplicate data and false positives and negatives, structuring it with metadata tags, and sorting it again.
Even small businesses today gather data every day on the order of millions of log events and hundreds of thousands of indicators. To begin making any sense of anything, data collection and processing must be automated because there is too much for human analysts to handle well.
Solutions like SIEMs are a great place to start since they make it extremely simple to structure data with correlation rules that can be set up for a few various use cases, even though they can only handle a few different types of data.
You'll need a more reliable solution if you're gathering unstructured data from numerous different internal and external sources.
Recorded Future uses machine learning and natural language processing to extract text from millions of unstructured documents in seven different languages and categorize it using language-independent ontologies and events. This allows analysts to carry out powerful and intuitive searches that go beyond simple correlation rules and keywords.
#4 Analysis
The analysis of the processed data is the next stage. Finding possible security concerns and alerting the appropriate teams in a way that satisfies the intelligence needs indicated in the planning and directing stage are the objectives of the analysis.
The purpose is to get the data into a format that the audience will understand. Threat intelligence can take different shapes based on the initial objectives and the intended audience. Simple threat lists to peer-reviewed reports are examples of this.
#5 Dissemination
After that, the finished product is given to the target market. Threat intelligence must reach the appropriate individuals at the appropriate moment to be usable.
To maintain continuity between one cycle of intelligence and the next and to prevent learning from being lost, it must also be tracked. Utilize ticketing systems that interact with your other security systems to keep track of each stage of the intelligence cycle.
This way, whenever a new intelligence request is made, tickets can be filed, prepared, reviewed, and completed centrally by numerous individuals from various departments.
#6 Feedback
The intelligence cycle completes its loop at the final stage, which is why it is closely tied to the beginning planning and directing stage. Whoever submitted the initial request analyzes the completed intelligence product after receiving it to see if their questions were addressed.
Benefits of Threat Intelligence
Threat intelligence is advantageous to everyone with a security interest. Benefits, especially if you're in business, include:
- Avoiding Data Breaches
Data breaches should be prevented with the help of a thorough cyber threat intelligence system. It accomplishes this by keeping an eye on dubious domains or IP addresses that are attempting to connect to the networks of an organization. A good CTI system will prevent questionable IP addresses from accessing the network, which could otherwise be used to steal your data. A Distributed Denial of Service (DDoS) attack could be carried out by hackers without a CTI system in place by flooding the network with fake traffic. - Reduced Costs
Data breaches are pricey. The average cost of a data breach worldwide in 2021 was $4.24 million (although this varies by sector – the highest being healthcare). These expenses cover post-incident reinstatement charges as well as things like fines and legal fees. Cyber threat information can help organizations save money by decreasing the likelihood of data breaches. - Reduced Risks
Hackers are constantly hunting for new entry points into corporate networks. By using cyber threat information, businesses can quickly spot emerging vulnerabilities, lowering their risk of data loss or disruption of normal company activities.
Conclusion
Digital processes are helping countless enterprises change the way they conduct business. They are collecting more data than ever before by shifting it from internal networks to the cloud.
Threat intelligence can give you insight into the threat environments of the third parties you collaborate with, providing you with the information you need to assess your interactions as well as real-time alerts on threats and modifications to their risks.
Explore:
IT Service Intelligence (ITSI)
Monitor Your Entire Application with Atatus
Atatus is a Full Stack Observability Platform that lets you review problems as if they happened in your application. Instead of guessing why errors happen or asking users for screenshots and log dumps, Atatus lets you replay the session to quickly understand what went wrong.
We offer Application Performance Monitoring, Real User Monitoring, Server Monitoring, Logs Monitoring, Synthetic Monitoring, Uptime Monitoring, and API Analytics. It works perfectly with any application, regardless of framework, and has plugins.

Atatus can be beneficial to your business, which provides a comprehensive view of your application, including how it works, where performance bottlenecks exist, which users are most impacted, and which errors break your code for your frontend, backend, and infrastructure.
If you are not yet an Atatus customer, you can sign up for a 14-day free trial.


