Modern security software can also be avoided by using malware created by APTs (Advanced Persistent Threats), which has a history of leaking into the world of cybercriminals, as well as zero days that commercial security companies store and sell to unidentified parties. Defenders must consequently exercise caution and employ a layered defense strategy to maintain a strong security posture. One such layer in a defense-in-depth strategy is threat hunting.
We will cover the following:
- What is Threat Hunting?
- How does Threat Hunting Work?
- Types of Threat Hunting
- Process of Threat Hunting
- Threat Hunting Methodologies
- Why is Threat Hunting Important?
What is Threat Hunting?
Threat hunting is a technique used to locate attackers hiding in your network before they can launch an attack or accomplish their objectives. Threat hunting, in contrast to most security strategies, is a proactive method that combines the information and capabilities of a sophisticated security solution with the strong analytical and technical abilities of a single threat hunting specialist or team.
It is a very different activity from digital forensics and incident response. DF/IR methodologies are used to determine what exactly occurred once a data breach has already been discovered. A threat hunting team's goal is to find attacks that may have already gotten past your defenses when they engage in threat hunting.
Threat hunting is different from vulnerability analysis and penetration testing as well. Threat hunters start from the premise that an attacker is already inside the network and then look for indicators of compromise, lateral movement, and other telltale artifacts that may reveal evidence of attack behavior.
How does Threat Hunting Work?
The data fertility of an environment is the foundation of a successful threat hunting campaign. In other words, a company must first have a data-collecting enterprise security system in place. Threat hunters can use the data acquired from it as useful information.
In addition to automated solutions, cyber threat hunters add a human element to company security. They are knowledgeable IT security specialists who find, log, monitor, and eliminate risks before they can cause significant issues.
Ideally, they are security analysts who are well-versed in the operations of the company's IT department, although occasionally they are external analysts.
Finding threats in an unknown environment is the art of threat hunting. It goes beyond traditional detection systems like endpoint detection and response (EDR), security information and event management (SIEM), and others.
Security data is combed over by threat hunters. They seek patterns of questionable activity that a computer might have overlooked or considered to be resolved but isn't, as well as hidden malware or attackers. They also assist in patching a company's security system to stop similar cyberattacks from happening in the future.
Types of Threat Hunting
Threat hunters begin by making assumptions based on security information or environmental triggers. They look into potential dangers further based on this information. Let's go over a couple of potential threat-hunting investigation styles.
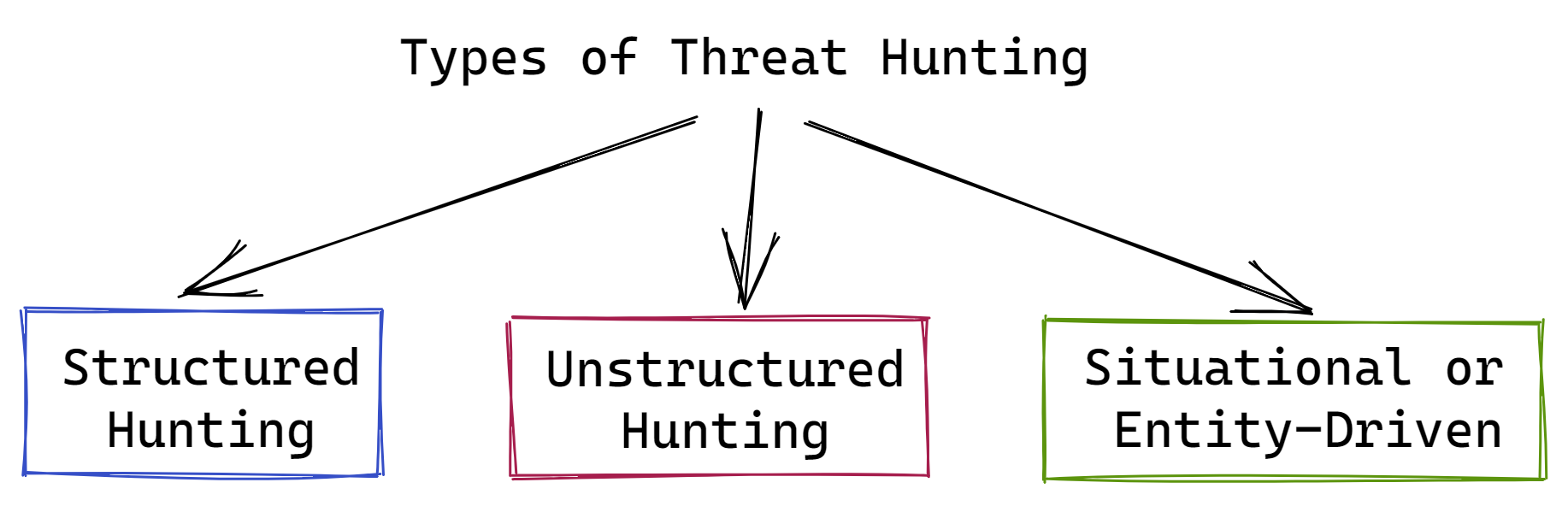
#1 Structured Hunting
Indicators of Attack (IoA) and the attacker's tactics, techniques, and procedures (TTP) serve as the foundation for structured threat hunting. Based on the TTP identified on the network, threat hunts are coordinated. Threat hunters can spot threat actors early in an attack, before they do environmental damage, by using TTP.
This kind of threat hunting is based on sources of threat intelligence like the MITRE ATT&CK Framework, which offers full information on a wide range of TTP.
#2 Unstructured Hunting
Beginning with a trigger or an indicator of compromise (IoC), unstructured threat hunting. The hunter scans the network both before and after the trigger or IoC for harmful patterns. As long as data retention restrictions allow it, threat hunters can examine historical data. Threats that have previously entered the environment but are inactive can be found using this method of threat hunting.
#3 Situational or Entity-Driven
Threat hunting that is situational or entity-driven concentrates on high-risk/high-value entities like sensitive data or vital computing resources. Its advantage is that it helps in bettering the effectiveness of threat hunting activity by helping to focus and prioritize it.
Attackers frequently go after particular high-value or high-risk assets or privileged individuals like IT administrators, domain controllers, and development managers. These high-value targets are found through focused searches for relevant threats and threat hunting.
Process of Threat Hunting
A proactive threat hunting process consists of three stages: the initial trigger phase, the investigation phase, and the resolution phase.
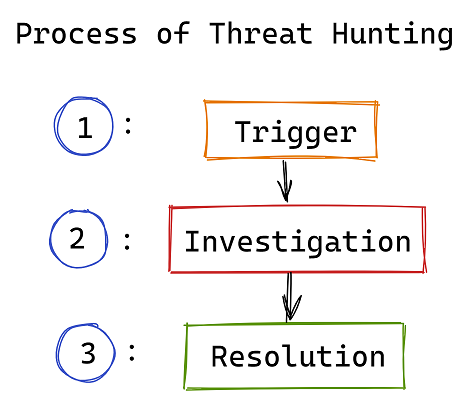
Step 1: Trigger
Hunting down threats is usually a targeted process. The hunter collects data about the surroundings and develops theories about potential threats. The hunter then selects a trigger to look into further. This could be a specific system, a network, or a theory.
Step 2: Investigation
After selecting a trigger, the hunting efforts are concentrated on actively looking for anomalies that either confirm or disprove the hypothesis. Threat hunters use a variety of tools to help them during the investigation as they look into anomalies that might or might not be malicious.
Step 3: Resolution
During the investigation stage, threat hunters collect crucial data. This information is shared with other teams and tools during the resolution phase so they can react, prioritize, examine, or store the information for later use.
Regardless of whether the data relates to lawful or unlawful action, it can be helpful in upcoming analyses and investigations. It can be used to improve your security measures, prioritize and fix vulnerabilities, and forecast trends.
Threat Hunting Methodologies
Threat hunting methods can be divided into three categories:
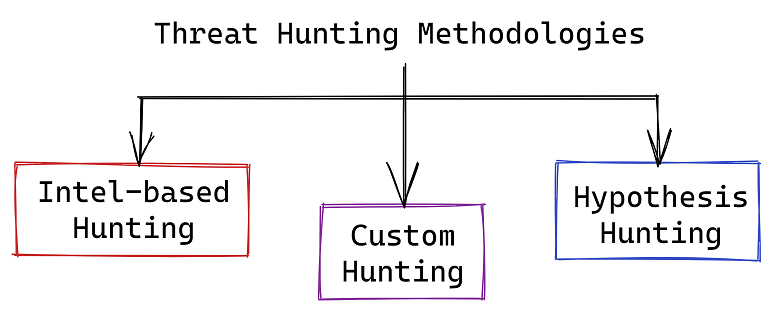
#1 Intel-based Hunting
Intel-based hunting is a reactive hunting method that makes use of IoCs from sources that gather threat intelligence. The hunt then proceeds with predetermined guidelines created by the SIEM and threat intelligence.
IoCs, hash values, IP addresses, domain names, networks, or host artifacts provided by intelligence sharing platforms like computer emergency response teams (CERT) can be used in intel-based hunts.
These platforms allow for the export of automated alerts, which can then be imported into the SIEM as trusted automated exchange of intelligence information (TAXII) and structured threat information expression (STIX).
The threat hunter can look into malicious activity that occurred before and after the warning once the SIEM has generated the alert based on an IoC to find any environmental breach.
#2 Hypothesis Hunting
A proactive hunting method called hypothesis hunting makes use of a threat hunting library. It is in line with the MITRE ATT&CK framework and employs global detection playbooks to recognize malware attacks and advanced persistent threat groups.
The IoAs and TTP of the attackers are used in hypothesis-based hunts. The hunter develops a hypothesis that is in line with the MITRE framework by identifying the threat actors based on the environment, domain, and attack behaviors used.
The threat hunter examines activity patterns after a behavior has been discovered to find, recognize, and isolate the threat. Through proactive detection of threat actors, the hunter can stop environmental harm before it occurs.
#3 Custom Hunting
Situational awareness and industry-based hunting methods are the foundation of custom hunting. It detects anomalies in SIEM and EDR tools and can be tailored to meet the needs of the customer.
Custom or situational hunts are carried out either proactively in response to conditions, such as geopolitical concerns and targeted attacks, or they are based on the requirements of the customer.
Both intelligence-based and hypothesis-based hunting models using IoA and IoC information can be used in these hunting activities.
Why is Threat Hunting Important?
The need for threat hunting arises from the fact that advanced attacks might evade cybersecurity systems.
You still need to be concerned about the remaining 20% of threats even if automated security tools and tier 1 and 2 security operations center (SOC) analysts should be able to handle most of them. Threats in the remaining 20 percent are more likely to be sophisticated and capable of doing considerable damage.
They can breach any network with enough time and resources and, on average, go undetected for up to 280 days. A faster period between intrusion and discovery decreases the amount of harm that attackers can cause.
Before being discovered, attackers may lurk for weeks or even months. They calmly wait to steal data and find enough private information or credentials to get access to more resources, creating the conditions for a significant data breach.
How much harm are potential threats capable of doing?
The "Cost of a Data Breach Report" states that a data breach often costs a corporation close to USD 4 million. And a breach's negative impacts can last for years. The more it can cost a business, the longer the interval between system breakdown and response deployment.
Conclusion
Threat hunting enables you to actively look for harmful activities to stay ahead of the most recent dangers. The majority of cyberattacks will be stopped in their tracks by cutting-edge technologies like behavioral AI, which are also necessary to provide the visibility threat hunting requires. However, criminal actors are constantly coming up with new tricks to get beyond enterprise network security.
To prevent vectors like insider threats and highly targeted attacks, organizations must take precautions. For your organization, using the knowledge of human analysts might add an extra layer of protection.
Also Read:
Threat Detection and Response (TDR)
Monitor Your Entire Application with Atatus
Atatus is a Full Stack Observability Platform that lets you review problems as if they happened in your application. Instead of guessing why errors happen or asking users for screenshots and log dumps, Atatus lets you replay the session to quickly understand what went wrong.
We offer Application Performance Monitoring, Real User Monitoring, Server Monitoring, Logs Monitoring, Synthetic Monitoring, Uptime Monitoring, and API Analytics. It works perfectly with any application, regardless of framework, and has plugins.

Atatus can be beneficial to your business, which provides a comprehensive view of your application, including how it works, where performance bottlenecks exist, which users are most impacted, and which errors break your code for your frontend, backend, and infrastructure.
If you are not yet an Atatus customer, you can sign up for a 14-day free trial.