SIEM (security information and event management) tools gather and aggregate log and event data to assist in the detection and tracking of security breaches. They're strong tools that give enterprise security professionals both real-time visibility into what's going on in their IT environment and a historical record of relevant events.
The purpose of a SIEM solution is to correlate signals in all of that data to give security professionals the knowledge they need to identify and track breaches and other issues.
We will go over the following:
What is SIEM?
Security Information and Event Management (SIEM) is a single security management system that collects and analyses data from a variety of sources throughout your IT infrastructure to offer full visibility into activity within your network in real-time. It collects, parses, and categorizes machine data from a variety of sources, then analyses it to deliver insights so you can take appropriate action.
A SIEM solution ingests and combs through large amounts of data in seconds to detect and alert on anomalous behavior, providing real-time insight to secure your business — a task that would be impossible to complete manually. SIEM offers you a snapshot of your IT infrastructure at any time, as well as the ability to store and manage log data to maintain industry compliance.
This ability to examine data in real-time from all network applications and hardware can assist organizations in staying ahead of internal and external dangers.
SIEM systems, in general, combine these two types of security information management. SEM (security event management) and SIM (security information management) are related security concepts. SIM is concerned with gathering and managing logs and other security information, whereas SEM is concerned with real-time analysis and reporting.
SIEM has been around for almost a decade and has seen significant evolution since Gartner coined the term in 2005. It may not have the excitement that AI technologies do, but in an increasingly complicated and fast-moving IT and security ecosystem, it is nevertheless vital for threat detection.
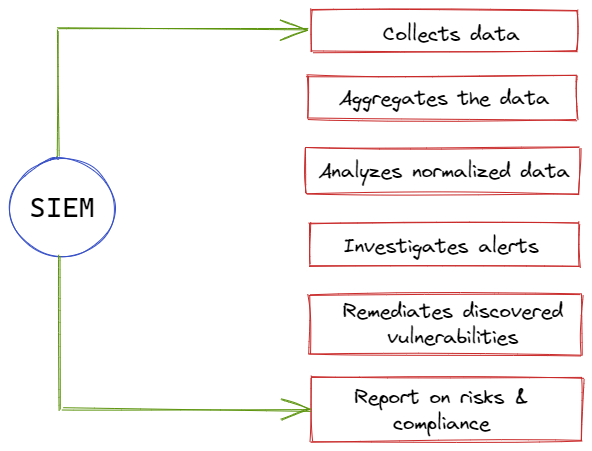
How Does SIEM Work?
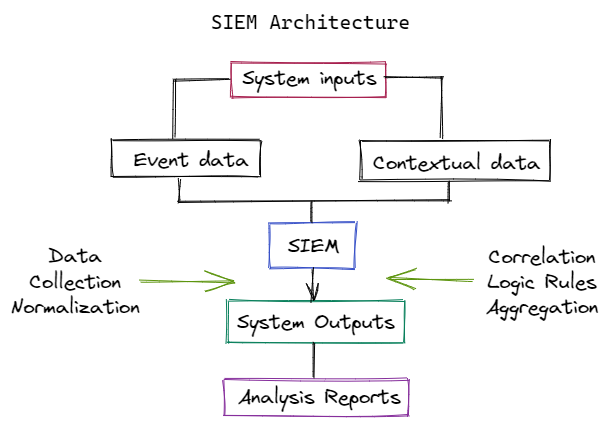
All of your security systems logs and other data must be sent to the SIEM platform. SIEM agents—programs that run on your various systems analyze and export data to the SIEM—can accomplish this; alternatively, most security systems have built-in features to export log data to a central server, from which your SIEM platform can import it.
Which choice you choose will be determined by your network topology, bandwidth capabilities, and the types of systems from which you need logs. If you don't implement things appropriately, the volume of data transported and processing power required at the endpoints can damage the performance of your systems or network.
By automatically processing some data before sending it over the network, SIEM agents at the edge can relieve some of that effort. In any case, you'll want to make sure that your entire infrastructure, both on-premises and in the cloud, is SIEM-enabled.
The amount of data created by this SIEM instrumentation is huge, far more than your employees could process. SIEM suites' main benefit is that they utilize data analysis to ensure that only relevant information is given to your security operations center. These platforms employ correlation engines to try to correlate disparate log entries or other signals that, on their own, aren't alarming, but when combined, can spell disaster.
Various SIEM companies leverage these engines, along with the specific artificial intelligence and machine learning algorithms used to detect attacks, to differentiate their products.
Threat intelligence feeds—basically, updated feeds of data regarding new forms of malware and the newest advanced persistent threats—are also used by SIEM tools. Other SIEM vendors maintain these feeds, but others are open source or managed internally by security teams at large companies, and some SIEM platforms allow you to utilize your favorites. The ability to securely link your SIEM platform with certain security products is another customization option.
SIEMs were first hailed for their ability to aid regulatory compliance; this is still a key role for these tools, and many platforms include built-in capabilities that focus on assuring and documenting your compliance with various laws and regulations. Finally, some SIEM solutions include SOAR capabilities, which can partially or completely automate responses to threats detected.
Benefits of SIEM
Taking proactive actions to check for and mitigate IT security risks is critical, regardless of how big or small your company is. SIEM solutions serve businesses in a variety of ways, and they've become a vital aspect of security process optimization. SIEM's benefits include the following:
- Advanced and Unknown Threats Detection
Organizations must be able to rely on solutions that can detect and respond to both known and new security threats, given how quickly the cybersecurity landscape changes. SIEM systems can successfully minimize modern-day security breaches by utilizing integrated threat intelligence feeds and AI technology. - AI-driven Automation
Today's next-gen SIEM solutions interact with powerful Security Orchestration, Automation, and Response (SOAR) features, allowing IT teams to manage corporate security while saving time and resources. These solutions can handle complex threat identification and incident response protocols in substantially less time than physical teams because of deep machine learning that adjusts to network behavior automatically. - Compliance Evaluation and Reporting
Many organizations find compliance audits and reporting to be both required and difficult. By offering real-time audits and on-demand reporting of regulatory compliance whenever needed, SIEM systems drastically minimize the resource expenditures required to manage this process. - Forensic Investigations
SIEM systems are capable of doing digital forensic investigations in the event of a security attack. SIEM systems enable businesses to centralize the collection and analysis of log data from all of their digital assets. This allows them to reproduce previous occurrences or evaluate fresh ones to examine suspicious activity and improve security systems. - Improved Organizational Efficiency
SIEM can be an important driver of enhancing interdepartmental efficiencies since it improves the visibility of IT environments. Teams can communicate and coordinate rapidly when responding to perceived events and security problems with a single, unified view of system data and integrated SOAR. - Real-time Threat Recognition
SIEM active monitoring solutions deployed across your whole infrastructure help to boost security posture by reducing the time it takes to identify and respond to potential network attacks and vulnerabilities. - Regulatory compliance Auditing
SIEM solutions provide for centralized compliance auditing and reporting across a company's complete infrastructure. Advanced automation reduces internal resource utilization while maintaining tight compliance reporting criteria by automating the collection and analysis of system logs and security events. - User and Application Monitoring
Organizations require the level of visibility required to manage network hazards from outside the traditional network perimeter, as remote workforces, SaaS applications, and BYOD (Bring Your Own Device) policies have grown in popularity. SIEM systems monitor all network activity across all users, devices, and applications, dramatically boosting infrastructure transparency and detecting risks regardless of where digital assets and services are used.
Best Practices for SIEM
Here are some SIEM best practices to adopt before or after you invest in your new solution:
- Set Your Scope
Establish the scope of your SIEM deployment. Create policy-based rules that specify which actions and records your SIEM software should monitor. Determine what form of a dashboard and reporting your organization requires by comparing that policy's guidelines to external compliance requirements. - Fine-tune Correlation Rules
SIEM software comes with a pre-configured set of correlation rules. By enabling everything by default, your security team can fine-tune the software to your organization's needs, analyze behavior, and uncover tuning opportunities to improve detection efficacy and reduce false positives. - Identify Compliance Requirements
Most organizations that use SIEM gain from meeting compliance obligations. To meet organizational auditing standards, an organization should assess software's capacity to support certain compliance mandates. - Monitor Critical Resource Access
A SIEM solution should keep track of privileged and administrative addresses, as well as anomalous user behavior on systems, remote login attempts, and system failure. - Defend Network Boundaries
SIEM should monitor all susceptible regions on a network, including firewalls, routers, ports, and wireless access points. - Test Your SIEM
When testing your SIEM installation and seeing how it reacts, you can get important alert metrics and see whether you need to reconfigure it. - Implement Response Plan
Only an incident response plan can deal with security incidents in a timely manner. Following a SIEM alert, organizations should prepare how they will notify employees.
Why is SIEM important?
Security information and event management (SIEM) combine security information management (SIM) with security event management (SEM) to provide real-time monitoring and analysis of occurrences, as well as tracking and logging of security data for compliance and auditing.
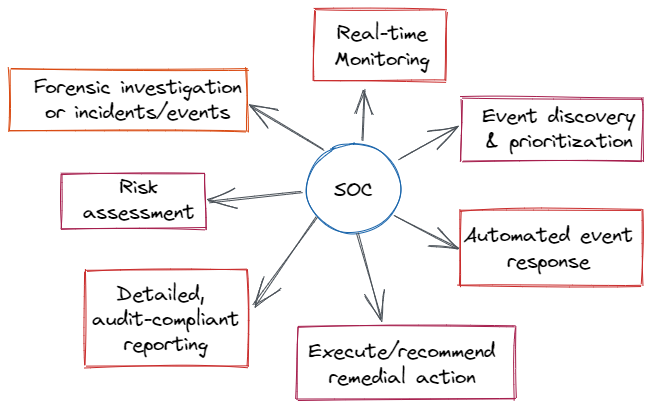
It detects unusual user behavior and employs AI to automate many of the human operations associated with threat identification and incident response. For security and compliance management use cases, it has become a standard in modern security operation centers (SOCs).
SIEM has evolved over time to become more than the log management tools that came before it. Thanks to AI and machine learning, SIEM now enables advanced user and entity behavior analytics (UEBA). It's a robust data orchestration solution for managing constantly changing risks, as well as regulatory compliance and reporting.
Conclusion
Security teams increasingly rely on SIEM technology for event correlation, threat intelligence, security data aggregation, and more in a world of increasing cyber threats – as well as escalating regulatory environments and consequences for security breaches. Enterprise security relies on quickly detecting and resolving security threats, therefore any security team would be wise to research the features of several SIEM systems to determine which one best meets their needs.
Further Reading:
Cloud Access Security Broker (CASB)
Enterprise Application Integration (EAI)
Monitor Your Entire Application with Atatus
Atatus is a Full Stack Observability Platform that lets you review problems as if they happened in your application. Instead of guessing why errors happen or asking users for screenshots and log dumps, Atatus lets you replay the session to quickly understand what went wrong.
We offer Application Performance Monitoring, Real User Monitoring, Server Monitoring, Logs Monitoring, Synthetic Monitoring, Uptime Monitoring, and API Analytics. It works perfectly with any application, regardless of framework, and has plugins.

Atatus can be beneficial to your business, which provides a comprehensive view of your application, including how it works, where performance bottlenecks exist, which users are most impacted, and which errors break your code for your frontend, backend, and infrastructure.
If you are not yet an Atatus customer, you can sign up for a 14-day free trial.