Clear the Cache Or Get the Cache Poisoned!
There are many ways to optimize the website for better performance. One of the most common optimization techniques is caching, which is the storing of data on a server so that it can be accessed quickly.
Cache poisoning can happen when a web page tries to store data in the same memory space as another application. This can cause problems for the other application, as the data is corrupted and may cause it to crash.
To avert cache poisoning, make sure that the web pages don't try to store any data in the memory space of other applications.
This can be done by using proper caching techniques, or by using a web server that doesn't allow direct access to the memory space of other applications.
Cache poisoning results from a hacker interfering with the way a computer processes data. This can lead to all sorts of problems, from slowdowns and system crashes to unauthorized access to your personal information.
For say, cache poisoning typically occurs when a website injects malicious code into the browser cache, which is then executed each time the victim visits the website.
This makes it easy for the attacker to exploit vulnerabilities on the victim's computer, steal sensitive information, or even install malware.
What is Cache Poisoning?
Cache poisoning is a term used to describe the harm that can be done to the computer by downloading malicious files from the internet.
In short, cache poisoning can lead the computer to become infected with viruses, spyware, and other malware. This infection can damage your computer's hardware, software, and data.
Cache poisoning is an issue that can occur on computer systems when malicious software or a virus infiltrates a cache or temporary storage location on the system.
The cache contains data that has been recently used by the system, and if the data is compromised, it can be used to attackers’ advantage. This can include stealing confidential information or installing malicious software.
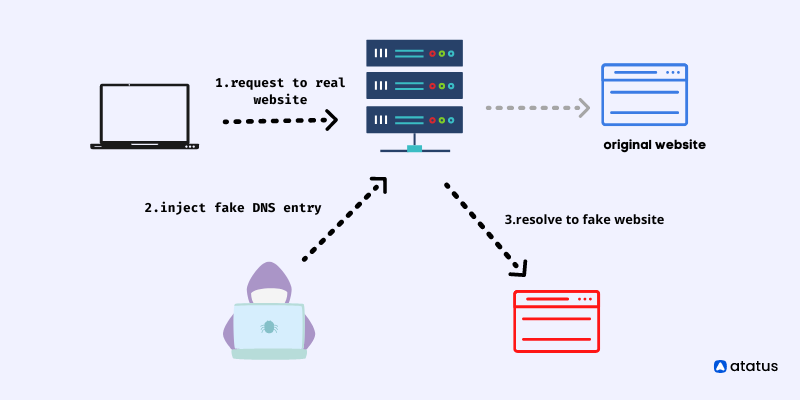
DNS poisoning is a type of attack that can disrupt online services. It happens when a malicious person tricks a computer into resolving a specific IP address instead of the correct DNS server.
This can cause serious damage to the victim's computer and online account, as well as prevent them from accessing their online resources.
How does Cache Poisoning work?
Cache poisoning happens when a browser or email program caches web pages and emails. When the user visits a cached page or email, the program stores a copy of the page or email on the computer.
If the user deletes or changes the content of the cached page or email, the program doesn’t update the cached copy on the computer. This can lead to problems if the client tries to access the cached page or email later and it’s not there anymore.
Cache poisoning might be used in a variety of modes. By temporarily taking over the source server and serving corrupted data that has been stipulated as cached for an extended duration of time, the intermediate web cache may be compromised.
The alternative way is to intrude on the HTTP request and response stream transmission ‘tween the source server and the web cache, which may be done by attacking the intermediate web cache server.
HTTP response splitting attack is used by assailants to infuse malicious material into a vulnerable web application, especially via HTTP requests. The information is thereupon transmitted to the user as a header that isn't authorized.
Examples of Cache Poisoning
Most people probably rely on the internet to do their daily tasks. But what if their favorite website or app was suddenly unavailable?
That's exactly what happened to millions of people in 2013, when malicious actors took advantage of a DNS cache poisoning attack to hijack the addresses for google.my and google.com.my.
As a result, users could not access their favorite sites, and it took days for Google to fix the issue. Always be aware of the risks and keep your browser and operating system up-to-date with the latest security patches.
DNS cache poisoning is an attempt to trick a caching DNS server into caching a forged response.
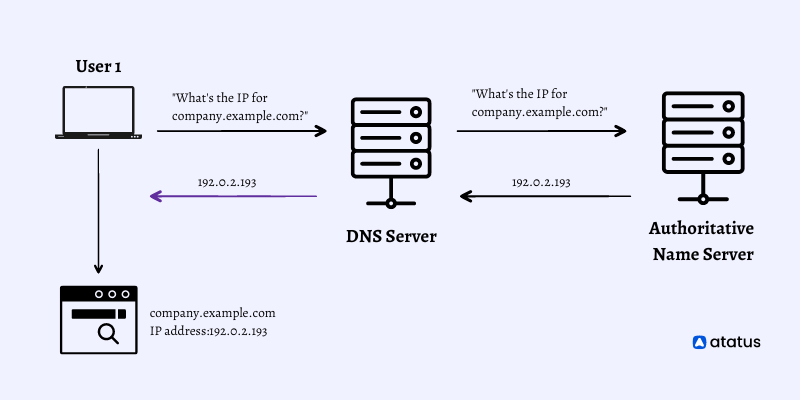
For instance, company.example.com is at 192.0.2.193, and poison.example.com is at 198.18.8.17, an assaulter can poison a DNS server’s cache by transmitting the forged response of “company.example.com is at 198.18.8.17.”
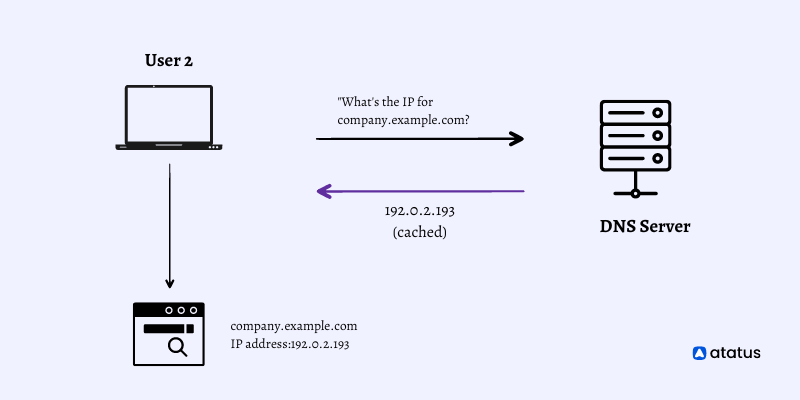
While the caching DNS name server carries the bogus response, it will respond with the poisoned response to the following company.example.com requests (til the record expires).
How to prevent from Cache Poisoning?
Cache poisoning can also lead to system crashes and other issues, so it is important to take precautions and protect your computer systems from cache poisoning.
Clearing cache poisoning via a completely disabled web cache would be the best way to prevent it. While it may not seem feasible for many websites, in other cases it might be achievable.
For an instance, if you only use caching because it has defaulted when you adopted a CDN, it might be advantageous to evaluate whether the default caching options truly fit your demands.
To avoid web cache poisoning vulnerabilities, it is important to disable caching altogether whenever possible. However, this is not always feasible, so it is also important to be aware of the different types of caching and how to disable them safely.
By following these simple tips, the website can significantly reduce the chances of being attacked via a web cache poisoning vulnerability.
Firstly, consider excluding something from the cache key for performance reasons.
If it is unable to rewrite the request, at least it can deny the request outright.
Be aware that some third party technologies may permit this default, so be sure to review your settings and make sure that caching is enabled only for trusted domains.
Finally, keep in mind that caching should be used in a responsible way and only for those resources that are required by the website.
Conclusion
Websites that suffer from cache poisoning make websites unusable while losing the trust of the businesses that run them.
It's important for a website owner to ensure that the cached content is compatible with their website's web site's needs and the priorities of their users. Adding security to the DNS using tools such as DNSSEC is one commonly used method for preventing cache poisoning.
In addition to limiting recursive queries in the DNS, ensure that only data related to the requested domain is stored and sent to users.

 +1-760-465-2330
+1-760-465-2330


