Every user action. Every change.
All in one place.
Atatus centralizes logs from your applications, servers, and databases into a single searchable stream, so your team can investigate incidents, detect anomalies, and prove compliance without chasing logs across five tools.
No credit card
Setup in minutes
SOC 2 compliant
GDPR ready
<50ms
Search latency (p99)
Hot storage · no rehydration required
99.99%
Log delivery SLA
Contractual · fully redundant ingest
14d
Free trial
Full access · no credit card needed
Scattered logs make audits harder than they should be
Centralize logs from all systems and make audits searchable, traceable, and reliable.
With Atatus
- One stream for all your logs such as app, infra, databases - searchable in a single interface
- Sub-50ms full-text search across months of logs, live. No cold starts, no rehydration fees
- One-click evidence export for SOC2, HIPAA, GDPR, and PCI-DSS. Ready in minutes, not weeks
- Anomaly detection fires within seconds of unusual activity before incidents become breaches
- Configurable retention per source including archive to S3, lock compliance-critical logs and purge on schedule
Without Atatus
- Application logs, server logs, and database logs sit in different tools. No unified view
- Searching old logs requires manual export, rehydration, or waiting on ops teams
- Compliance evidence is gathered by hand such as screenshots, exports, emails, weeks before an audit
- Suspicious activity is noticed after customers or security teams report it, not before
- Log retention policies are inconsistent. Some logs purge too early, others pile up with no controls
Everything you need to monitor, audit, and investigate
A complete audit trail platform built for security teams, DevOps, and compliance engineers.
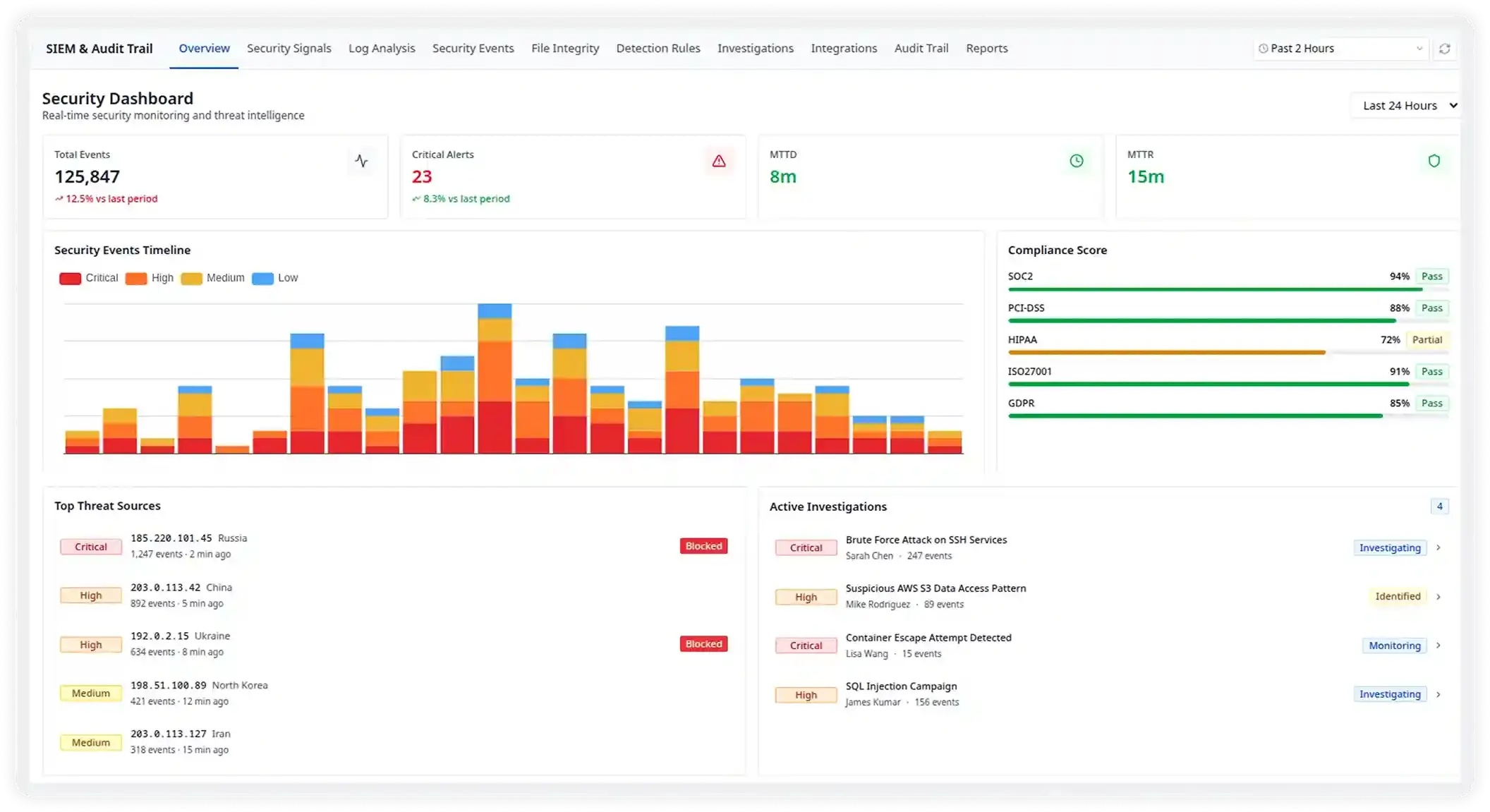
A Single Pane of Glass for Every Threat
Get an instant and unified view of your entire security posture including total events, critical alerts, MTTD, and MTTR on one live dashboard. Spot anomalies the moment they happen, not hours later.
- 125,847 events processed in the last 24 hours with sub-second latency
- Live security events timeline across Critical, High, Medium, and Low severities
- Top threat sources geo-mapped with instant block actions from the dashboard
- Active investigations surfaced with assigned analyst and real-time status
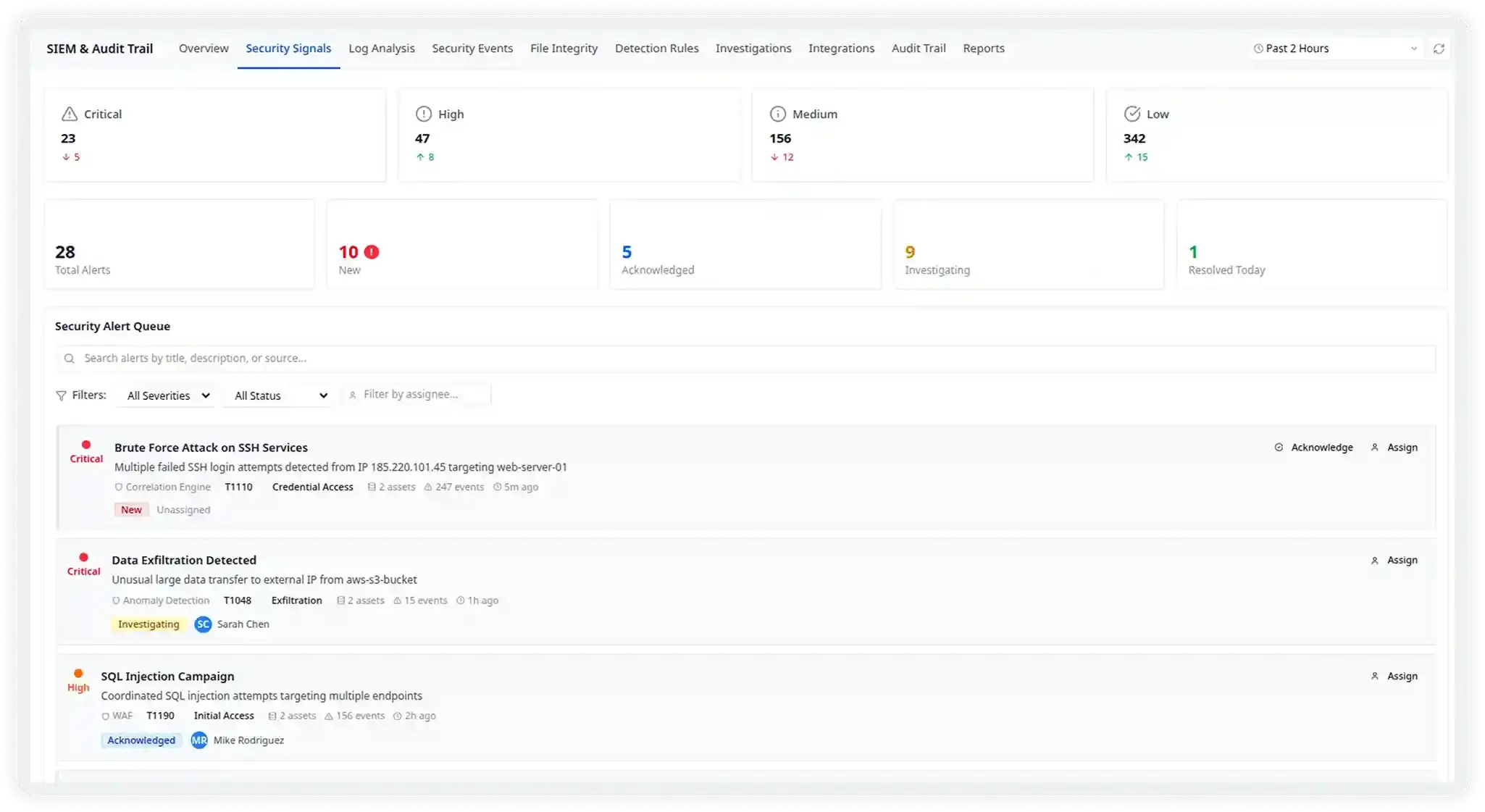
Triage Threats Before They Become Breaches
Every security alert lands in a prioritized queue - ranked by severity, enriched with MITRE ATT&CK context, and ready for your team to acknowledge, assign, or escalate in one click.
- Critical signals like brute-force SSH and data exfiltration surfaced instantly with full event context
- MITRE ATT&CK technique tags (T1110, T1048) on every alert for faster SOC response
- One-click assign to analysts with status tracking: New → Investigating → Resolved
- 28 active alerts managed across 23 critical and 47 high-severity signals
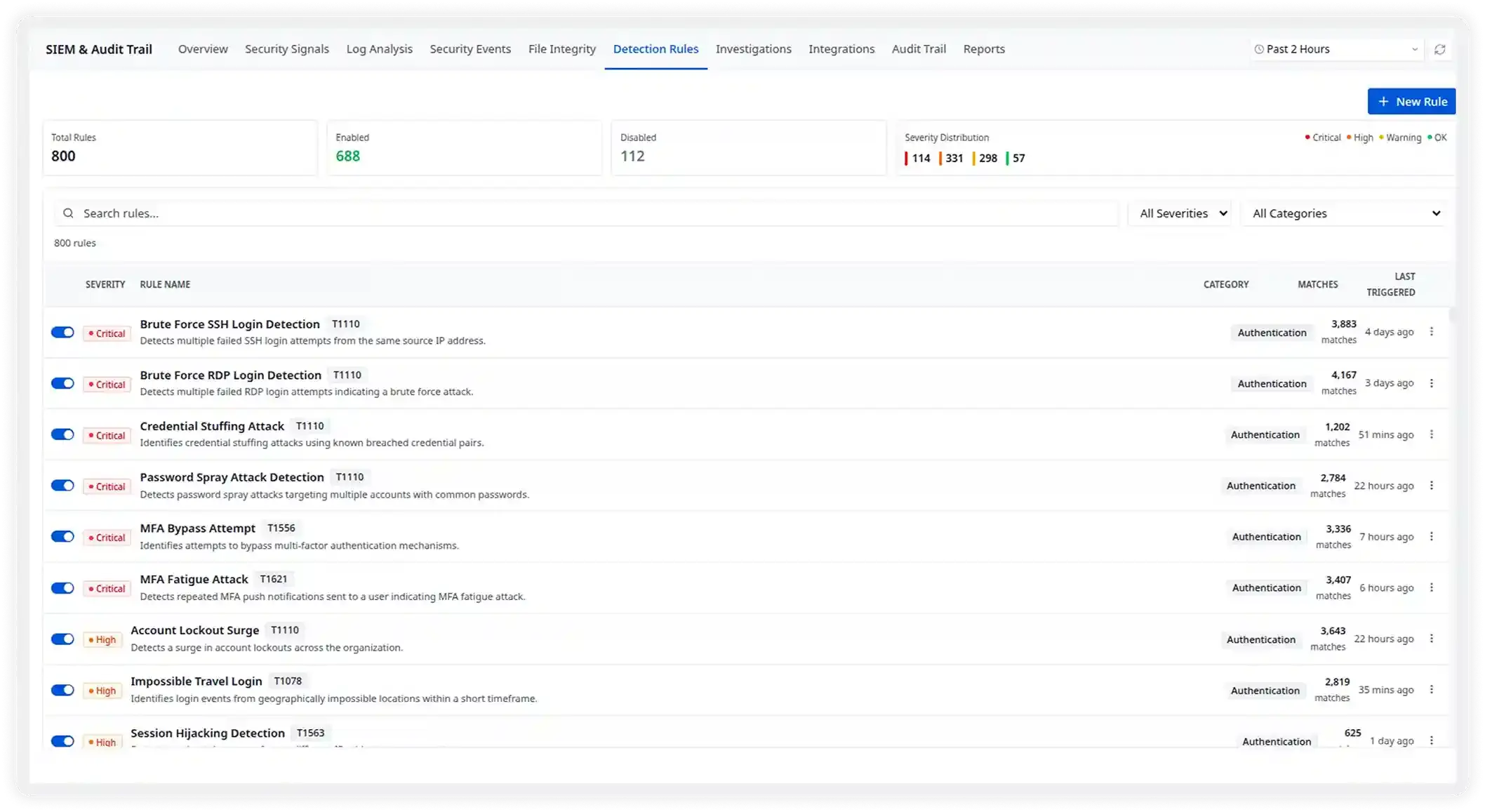
800 Pre-built Rules, Zero Configuration Needed
Start detecting threats on day one. Atatus ships with 800 battle-tested detection rules covering authentication attacks, lateral movement, data exfiltration, and more - all MITRE ATT&CK aligned.
- 688 rules enabled out-of-the-box covering authentication, network, cloud, and application layers
- 114 critical + 331 high severity rules with live match counts and last-triggered timestamps
- Detects Brute Force, MFA Fatigue, Credential Stuffing, Impossible Travel, and Session Hijacking
- Custom rule builder lets you create and tune rules without writing complex queries
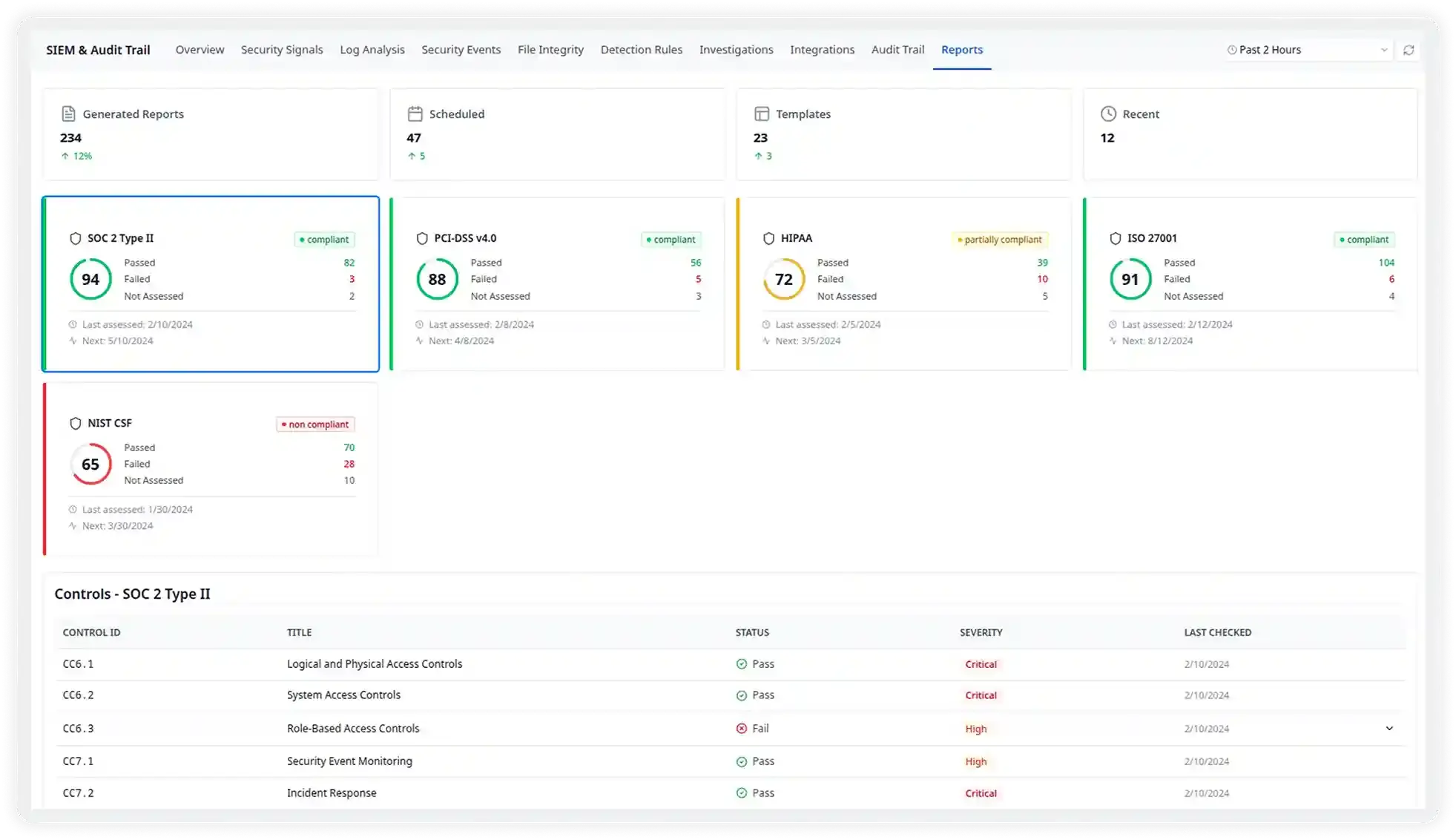
Audit-ready Reports for Every Framework
Stop scrambling before audits. Atatus continuously scores your compliance posture against SOC 2, PCI-DSS, HIPAA, and ISO 27001 and auto-generates evidence packages your auditors will love.
- SOC 2 Type II scored 94/100 compliant with granular control-level pass/fail visibility
- Pre-built frameworks for PCI-DSS v4.0, HIPAA, ISO 27001, and NIST CSF out of the box
- 234 generated reports with 47 scheduled and 23 reusable templates ready to share
- Drill into individual controls - CC6.1 through CC7.x with severity and last-checked dates
Built for Every Team That Needs Complete Audit Visibility
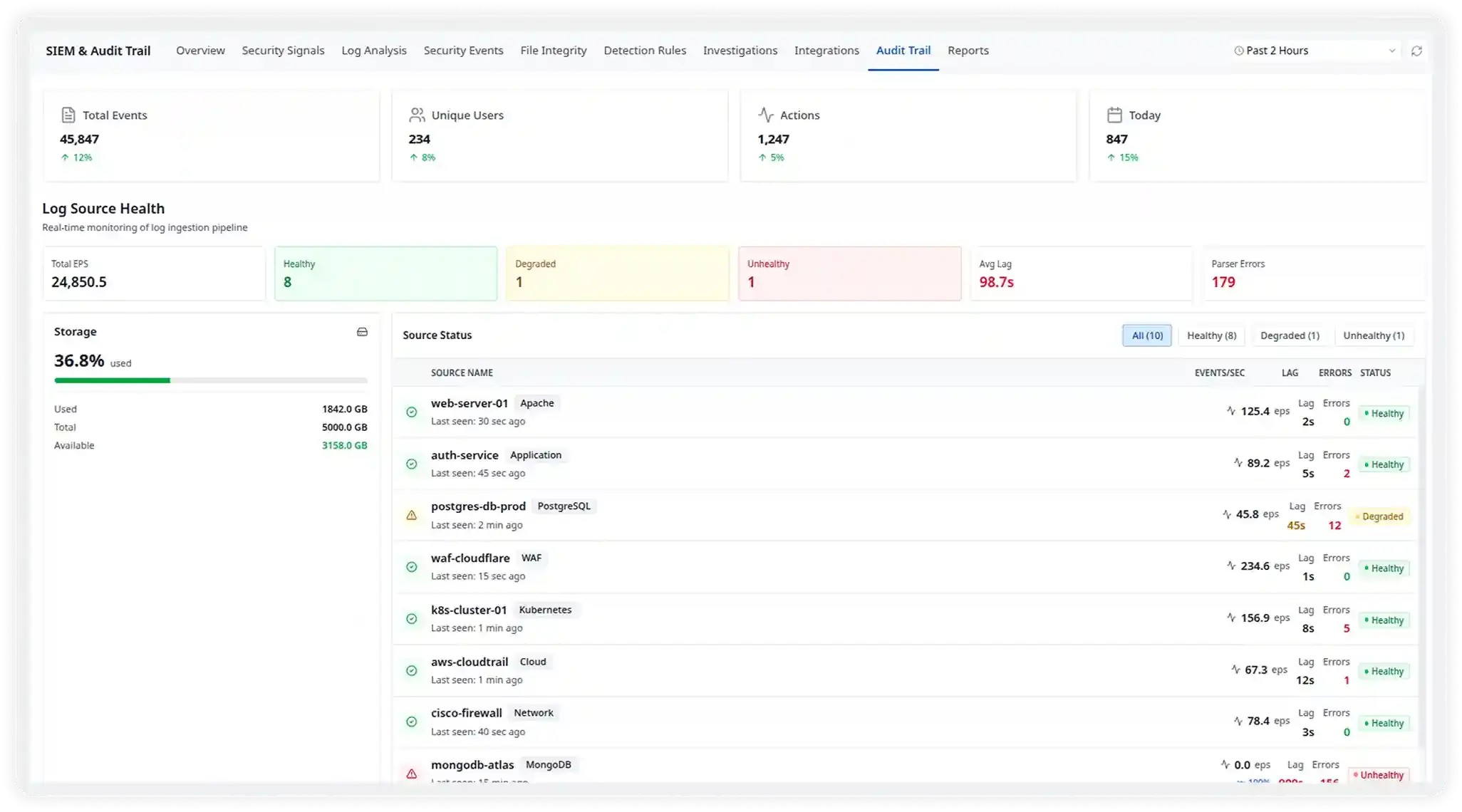
Capture and analyze every action across your systems in real time. Understand who did what, when, and where across your infrastructure and applications.
Security Monitoring & Threat Detection
Identify suspicious behavior such as unauthorized access attempts, privilege escalations, or insider threats. Correlate events across services to quickly investigate security incidents.
Compliance & Audit Readiness
Maintain a complete record of system activity to support regulatory frameworks like SOC2, HIPAA, PCI-DSS, and GDPR. Easily generate audit evidence and reduce manual compliance work.
DevOps & Infrastructure Visibility
Track deployments, configuration updates, and infrastructure changes. Quickly connect system modifications with performance issues or production incidents.
Product & User Activity Insights
Understand how users interact with your application. Analyze feature usage, debug unexpected behavior, and investigate user-reported issues with detailed activity trails.
Plugs into your existing stack
Atatus ingests from 100+ sources out of the box. No custom parsers, no brittle pipelines. Log normalization is automatic.











Up and running in under 5 minutes
No complex infrastructure. No agents to manage. Just connect, collect, and analyze.
Connect Your Sources
Plug in cloud providers, apps, and infrastructure using our SDKs or pre-built integrations.
Auto-ingest & Parse
Atatus normalizes and enriches all log formats automatically. No manual parsing rules needed.
Set Alert Policies
Define anomaly thresholds or use our pre-built security rules to get alerted on suspicious activity
Investigate & Report
Search, visualize, and export audit trails for incidents, reviews, or compliance audits in seconds.
Trusted by security-first teams
“We replaced Splunk and Datadog Audit Trail with Atatus and cut our monthly observability bill by 60%. Search is honestly faster, and having everything such as app, infra, identity in one place changed how our team investigates incidents.”
Marcus Reid
Head of Security
“Our SOC2 Type II prep used to take 3 weeks of manually exporting evidence from six different tools. With Atatus, our compliance engineer generates the full package in an afternoon. Our auditors were shocked.”
Priya Kaur
VP Compliance
“The anomaly detection caught an insider threat before any customer data left the building. We got an alert within 40 seconds of the mass export starting. That's not something our previous setup could have done.”
James Liu
CTO