Detect Threats Before
They Become Breaches
Atatus SIEM centralizes your security logs, surfaces threats in real time, and arms your team with AI-driven insights on a single, cloud-native platform.
<1s
Threat detection latency
<500+
Built-in detection rules
99.9%
Uptime SLA
60%
Reduction in alert noise
Everything Your SIEM Actually Does
Built for detection engineers and compliance teams. No noise, only signal.
Compliance & Audit Readiness
Continuously maps log data and security controls to frameworks like SOC 2, ISO 27001, PCI-DSS, and HIPAA. Auto-generates audit-ready evidence packs, tracks control drift, and maintains a tamper-evident log trail, so audits don't turn into fire drills.
Signal Correlation & Noise Reduction
Ingests raw events from endpoints, cloud, network, and identity sources, then correlates across them using MITRE ATT&CK-aligned rules. Suppresses low-fidelity alerts and surfaces only actionable signals with full context, so analysts spend time investigating, not triaging.
Threat Detection & Response
Detects known and emerging threats in real time from lateral movement and privilege escalation to data exfiltration and insider risk. Triggers automated response playbooks, isolates affected assets, and enriches incidents with threat intelligence for faster, more decisive containment.
Built for the Way Modern Threats Move
Every capability designed around how attackers actually behave, not how legacy SIEMs were architected.
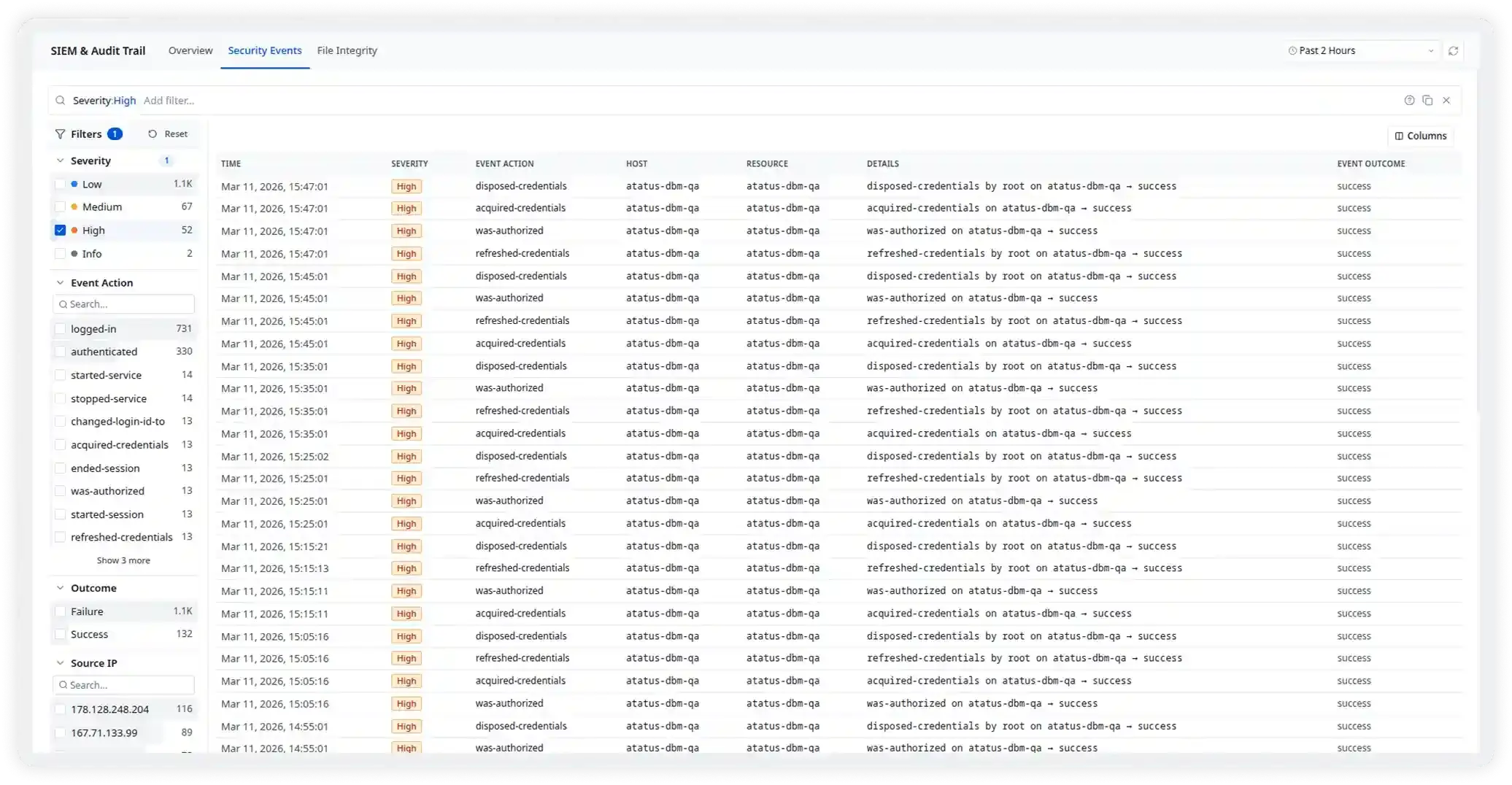
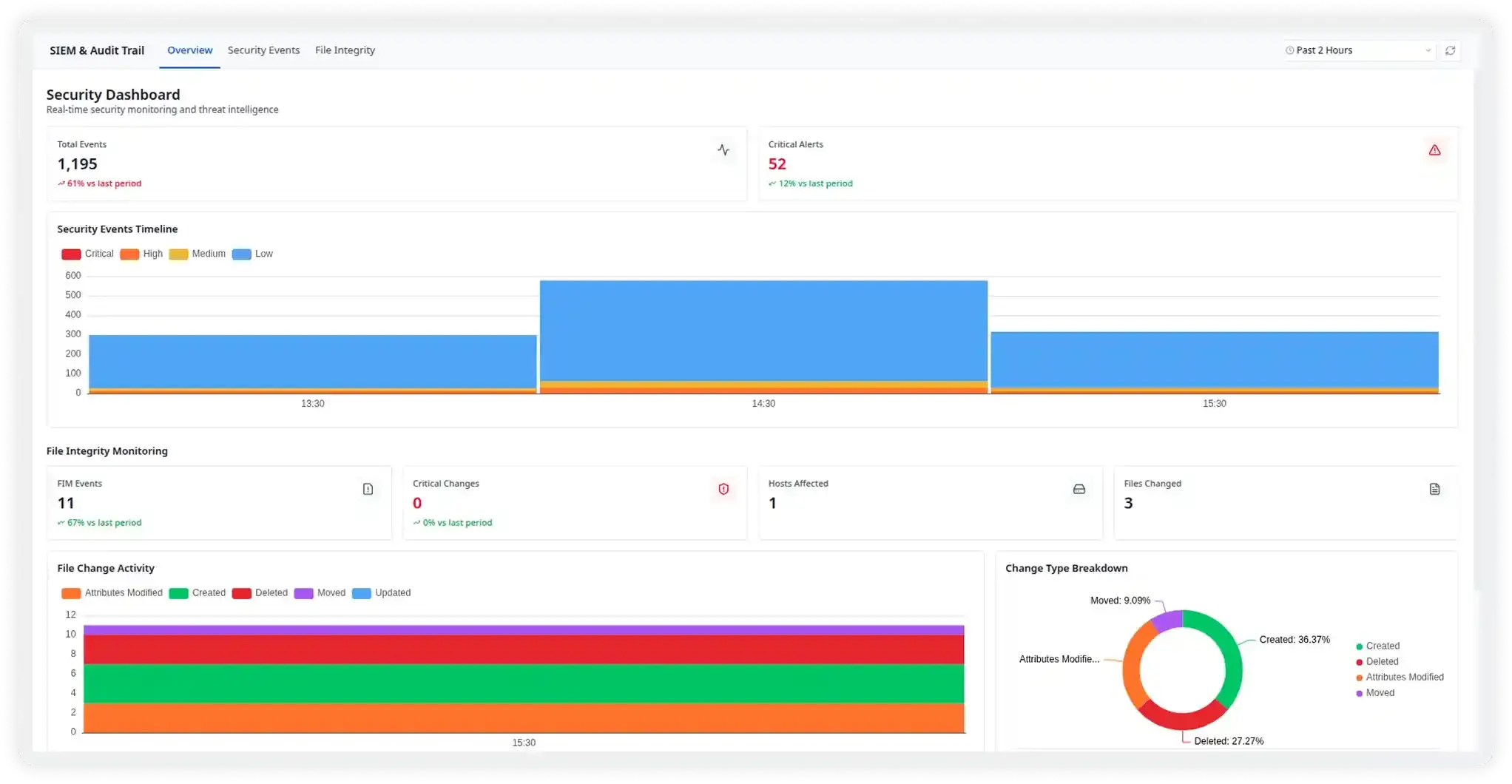
Track Security Events Across Your Infrastructure
Atatus SIEM continuously collects and analyzes security events from servers, applications, and cloud services. Security teams gain real-time visibility into authentication attempts, credential usage, and system activity, allowing them to quickly detect anomalies and potential threats.
- Monitor security events across hosts, users, and services
- Filter events by severity, source, or event type
- Identify suspicious authentication or credential activity
- Investigate incidents with structured security logs
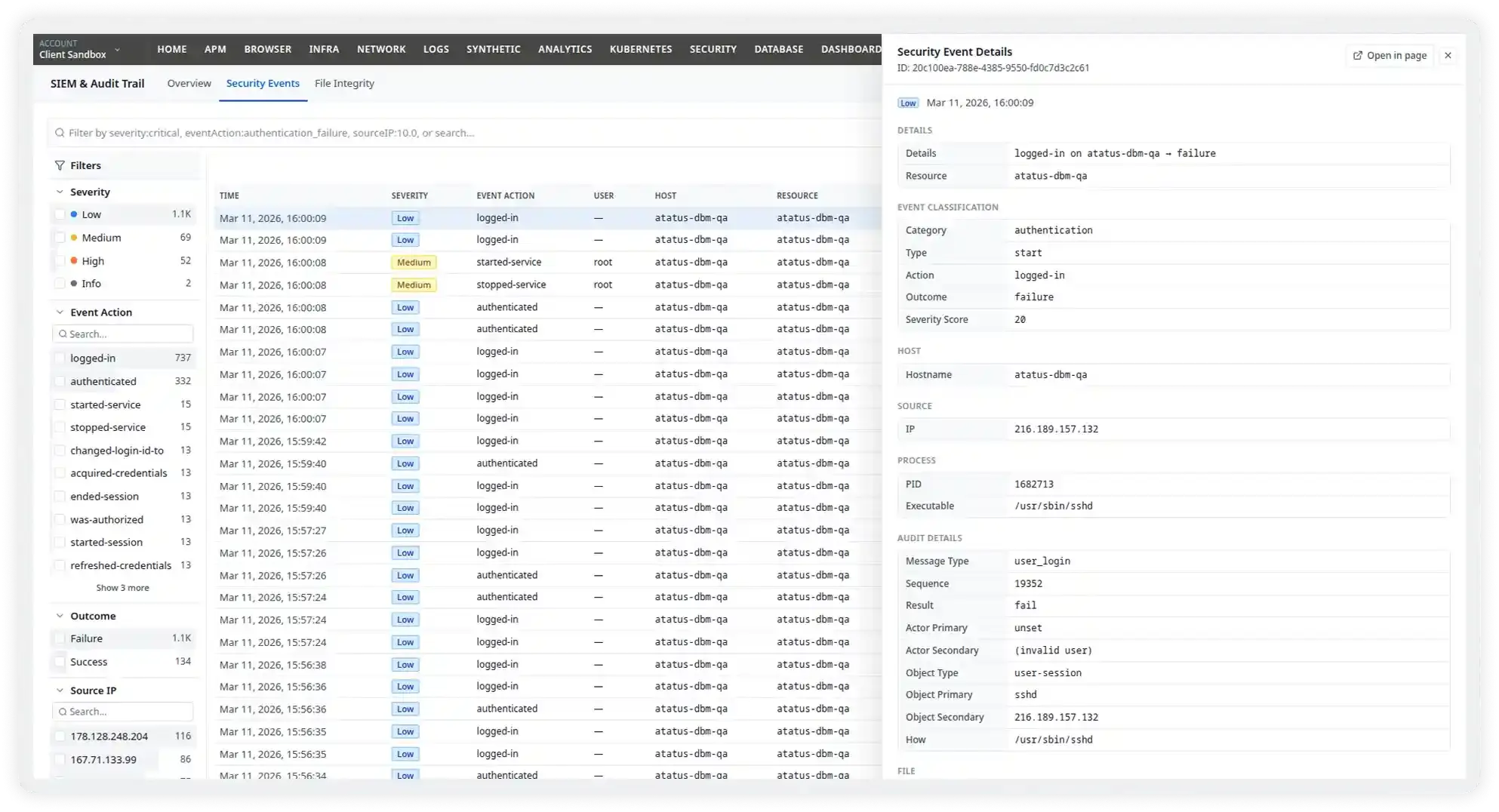
Detect and Contain Threats Before They Spread
Atatus detects known and emerging threats in real time from ransomware patterns and data exfiltration to privilege escalation and insider risk. Automated response playbooks trigger instantly to isolate assets, block activity, and enrich incidents with threat intelligence for faster containment.
- Detect lateral movement, exfiltration, and ransomware in real time
- Trigger automated SOAR playbooks on confirmed threats
- Enrich incidents with threat intelligence and asset context
- Investigate with full kill-chain timeline per incident
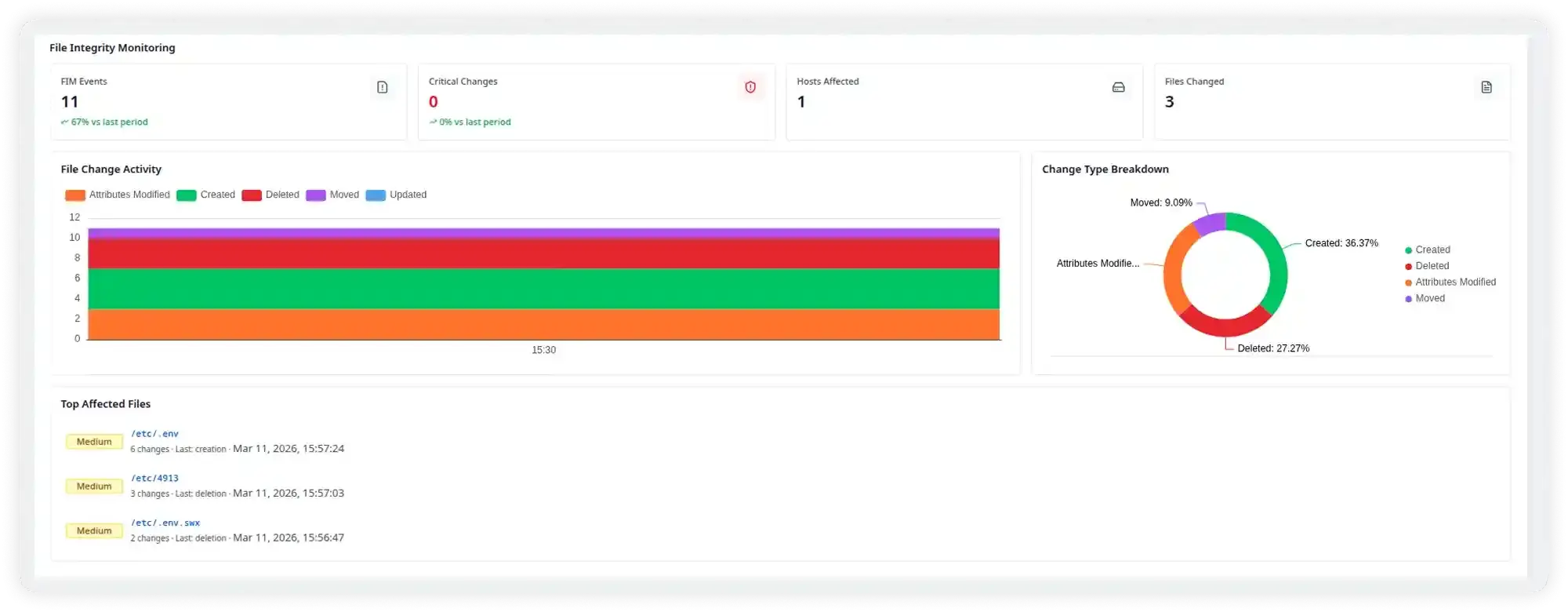
Detect Unauthorized File Changes Instantly
Atatus monitors critical system files and tracks every modification across your infrastructure. Security teams can quickly identify suspicious file changes, unauthorized access attempts, or configuration tampering that may indicate a potential security breach.
- Monitor critical files across servers and environments
- Detect file creation, modification, and deletion events
- Identify suspicious configuration changes
- Receive visibility into system file activity in real time
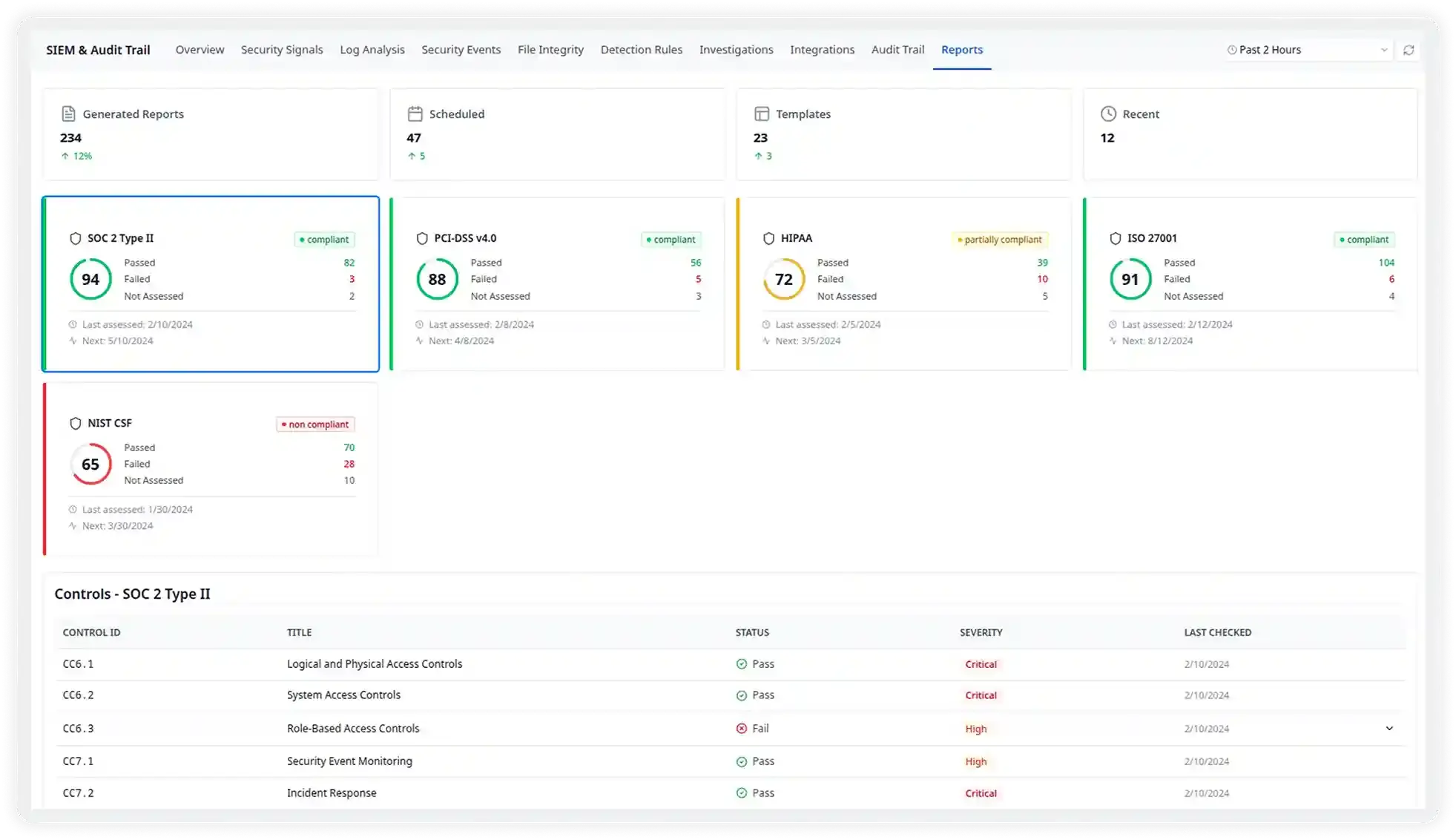
Stay Audit-Ready Across Every Framework
Atatus SIEM continuously maps your log data and security controls to SOC 2, ISO 27001, PCI-DSS, and HIPAA. Evidence packs are auto-generated, control drift is flagged instantly, and every log is stored in a tamper-evident trail, so audits never catch you off guard.
- Map controls to SOC 2, PCI-DSS, ISO 27001, and HIPAA in real time
- Auto-generate audit evidence packs on demand
- Detect and alert on control drift before auditors do
- Maintain tamper-evident, long-term log retention
From Log Data to Security Response
Atatus SIEM collects, analyzes, and correlates security logs across your infrastructure to detect threats in real time and help teams investigate and respond to incidents faster.
Ingest & Normalize at Any Scale
Connect your cloud providers, SaaS apps, endpoints, and identity providers. Atatus automatically parses, normalizes, and enriches every log — no manual configuration required.
Apply Detection Rules Instantly
500+ out-of-box rules fire against your full log stream the moment data arrives. Write custom rules with a simple, no-code editor. No proprietary query language required.
Correlate & Prioritize Signals
AI correlates signals across sources and time windows, surfaces entity risk scores, and hands analysts a ready-to-act verdict, not a pile of raw alerts to sort through.
Investigate & Respond Fast
Pivot seamlessly between security signals and full observability context including metrics, traces, and APM on one pane of glass. Trigger automated SOAR workflows instantly.
Loved by Security Teams at Scale
“Atatus SIEM gave our SOC team the visibility we always wanted but couldn't get from our legacy SIEM. We went from investigating threats in hours to minutes. The AI triage alone cut our analyst workload by 60%.”
Marcus Hayes
Head of Security Engineering
“The detection coverage we got on day one was remarkable. Within a week of onboarding, we had surfaced threats that had been sitting undetected in our environment for months. Setup was genuinely painless.”
Sarah Kowalski
Senior Security Analyst
“We process billions of events daily. Atatus handles it without flinching, and the tiered log storage means we're not burning budget on compliance logs we rarely query. Best cost-to-coverage ratio we've seen.”
James Brennan
VP of Infrastructure & Security