What is a Reverse Proxy Server?
A reverse proxy is an application which sits in front of backend applications and forwards clients(like a web browser) requests to those applications. The resources which are returned to the client appear as if they originated from the browser itself.
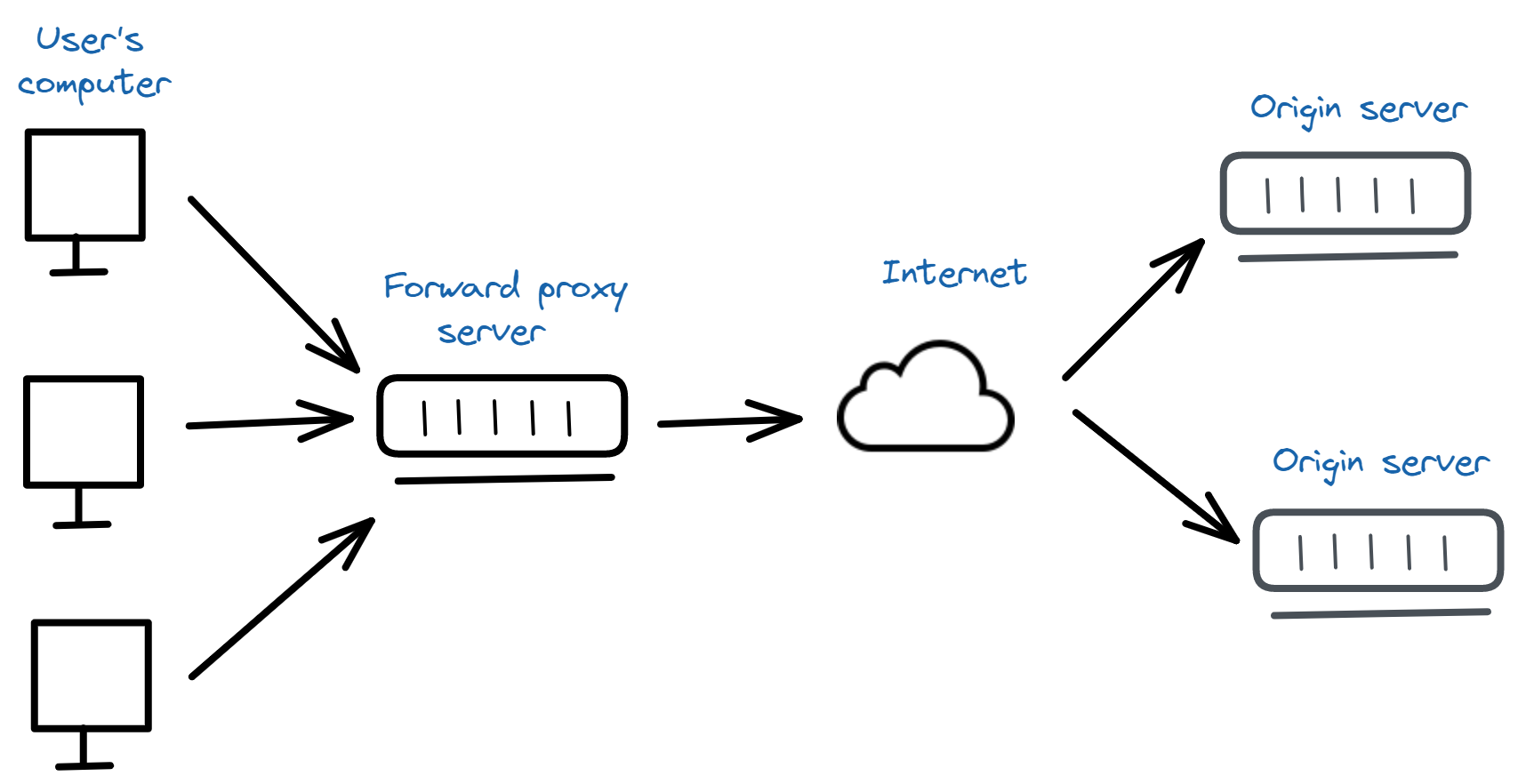
In order to understand reverse proxy servers, knowing the proxy servers is important first. A forward proxy which is also known as a web proxy is a system on the internet which accepts the incoming requests from the client and forward those requests to the destination server.

It acts as a gateway between the end-user and the internet. It allows us to access websites from a different IP address other than ours.
In a usual internet communication, the user's computer would reach out directly to the origin/target server. But since the proxy server comes to play, the user's computer reaches the proxy server first, and then the proxy server forwards the requests to the final server.
The advantages of using this proxy server are:
Identity protection: Our identity is protected in the network since the proxy server assigns the user a completely new IP address other than theirs. This is very essential for users who wanted to be anonymous on the internet.
Blocking access to certain sites: Proxies can be used to block access to certain sites. This can be useful for schools and colleges that want to enable filtering rules on the sites where students are not allowed to use social media within the campus.
How reverse proxy differs from forward proxy?
The difference between a forward proxy and a reverse proxy is that the proxy sits in front of clients whereas a reverse proxy sits in front of the servers.
In the reverse proxy, when the clients send requests to the origin server, those requests are intercepted by the reverse proxy server.
Here the requests from the user’s computer are not directly sent to the origin/target server, instead, the reverse sever receives it and sends it to the origin server.
And the requests received from the origin server are then sent back to the respective user’s computer by the reverse proxy server.
The difference between the proxy server and the reverse proxy can be put into like this. The forward proxy makes sure that no origin server directly communicates with the specific client by sitting in front of a client.
Whereas, the reverse proxy makes sure that no client directly communicates with the origin server by sitting in front of the server.
Benefits of reverse proxy server
Below are some of the uses of using a proxy server:
Balancing the load: With only one single server to handle a website with high traffic, it is difficult. So, multiple servers are needed here to handle the traffic. In this case, the reverse proxy server can be used to distribute the load among the pools of servers by avoiding a single server getting loaded.
Caching: A reverse proxy can also cache content which in turn provides faster performance.
SSL encryption: If the origin server has to encrypt and decrypt SSL(TLS) communications for the client then it may be expensive. A reverse proxy server in turn can be configured to encrypt and decrypt the incoming request and outgoing responses.
Protection from attacks: If the reverse proxy is used, then the website doesn't need to show the true IP of its origin server. So, when an attacker tries to attack the website, then they couldn’t implement it since they don't know its IP, thus ending up targeting reverse proxy.
Global Server Load Balancing: In GSLB, a website can be distributed on multiple servers around the global network and the reverse proxy will send clients which are very closest to them geographically. This will reduce the distance that the request and response need to travel, thus minimizing load times.
The reverse proxy is able to perform A/B testing and multivariate testing without the need to place Javascript or code into the pages.
A reverse proxy can add a basic HTTP access authentication to a web server that has no authentication.
A reverse proxy can optimize content by compressing which increases its loading speed.
Risks in using reverse proxy
While there are benefits in using a reverse proxy, there are some risks too which are explained below:
A reverse proxy can track all IP addresses which made requests through it, and it can also read and modify any non-encrypted traffic. So if compromised by a malicious party then it could be trouble.
Using the reverse proxy from a third party places the confidentiality, integrity, and availability in the hands of third-party that operates it.
If a reverse proxy is properly not configured to filter malicious attacks, a zero-day vulnerability can pass through, enabling attackers to gain control of the system that is behind the proxy server.
If there is no alternative way to access the backend server directly, then reverse proxies can become a single point of failure.
If reverse proxy fronts many different domains, its outage could bring down all frontend domains.
Applications specifically developed for the internal use of the company usually don't meet the public standards of safety nor do they have enough stability to withstand the hacking attempts. When these applications try to access external websites using a reverse proxy server, this may increase the risk of being attacked or hacked by the attackers.
In order to encrypt and decrypt the communication, a reverse proxy server needs SSL/TLS certificate along with its private key, extending the number of systems that have access to non-encrypted data, thus making it vulnerable target for the attackers.
Conclusion
Reverse proxy has both advantages and disadvantages. We can eliminate its disadvantages by building our own reverse proxy as many companies do or by buying from a third party.
Since building own proxy requires intensive software and hardware engineering resources and a large investment in physical hardware. Obviously, for most companies buying from a third party is the only way but we should be aware of the risks while using a third party’s reverse proxy.
Awareness is required to reduce the risks in reverse proxy and thus make the user enjoy its benefits to the full.

 +1-760-465-2330
+1-760-465-2330


