Detect Exploitable Risks in Production, Not Just Scan Reports
Atatus Security gives your team real-time visibility into vulnerabilities that are actually exploitable, sensitive data flowing through your stack, and application threats - unified in one place.
70%
Faster mean time to remediate
90%
Reduction in false positives
<5ms
Sensitive data scan latency at ingestion
100%
Vulnerability accountability
Security Teams Are Drowning in Noise, Not Answers
Three compounding problems across vulnerability detection, data exposure, and application security solved together by Atatus.
Thousands of CVEs, Zero Prioritization Static scanners surface 3,000+ vulnerabilities with no signal on what's actually reachable in production. Teams are paralyzed - everything looks critical.
Sensitive Data Leaking Through Logs & Traces Credit cards, JWTs, API keys, and PII end up in your observability stack before anyone notices. Retroactive cleanup is expensive and often incomplete.
Security Reviews Blocking Every Release Security happens at the end of the cycle. Developers get vulnerability reports disconnected from their workflow, context is lost, and fixes take 60+ days.
Three Products. One Security Layer
Each product solves a distinct problem. Together they give you complete coverage from code to runtime to compliance.
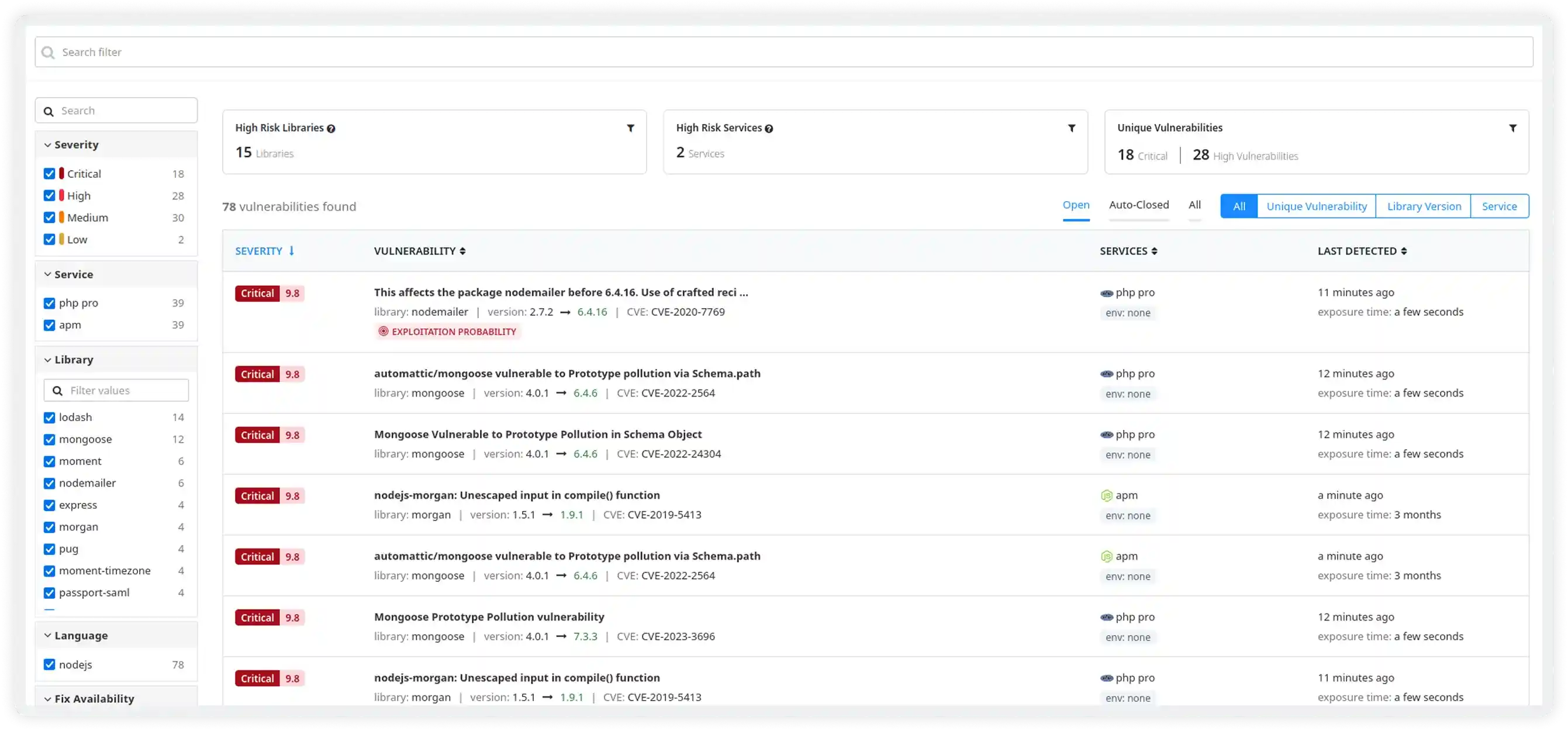
Prioritize and Fix Vulnerabilities That Matter
Atatus continuously scans your entire stack including applications, dependencies, containers, and infrastructure and surfaces only the vulnerabilities that are genuinely exploitable in your production environment. AI-powered risk scoring goes beyond CVSS to factor in runtime context, asset sensitivity, and live threat intelligence.
- Automated discovery across hosts, pods, containers, and dependencies. No manual configuration
- Risk score uses EPSS + exploitability + asset impact, not just CVE severity
- 90% reduction in false positives via ML-based context understanding
- Centralized tracking: owner, status, SLA deadline, remediation timeline in one dashboard
- Vulnerabilities detected within 1 hour of public disclosure
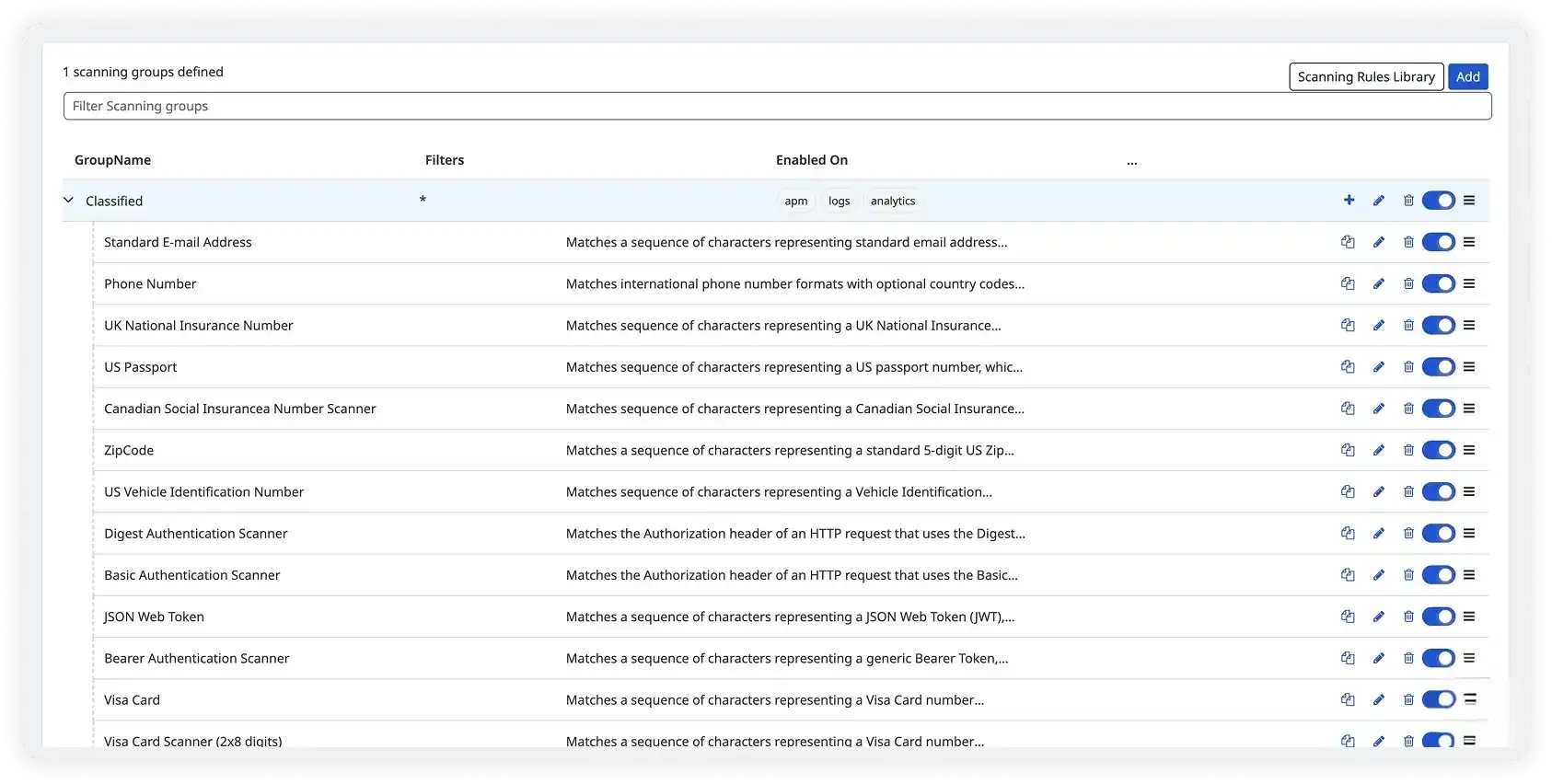
Identify and Protect Sensitive Data
PII, credentials, and regulated data flow through your logs, traces, and RUM events every day, often undetected. Atatus's Sensitive Data Classifier scans and redacts sensitive values at the point of ingestion, in real time, before they ever reach storage or third-party tools.
- Scans at ingestion in <5ms. Zero re-processing, zero retroactive exposure
- 30+ production-ready rules: credit cards, SSNs, JWTs, API keys, IBAN, OAuth tokens, AWS/GCP credentials
- Full redact, SHA-256 hash, partial mask. Configurable per rule
- Custom PCRE regex rules for internal data types
- Covers logs, APM spans, RUM events, CI pipelines, and cloud storage
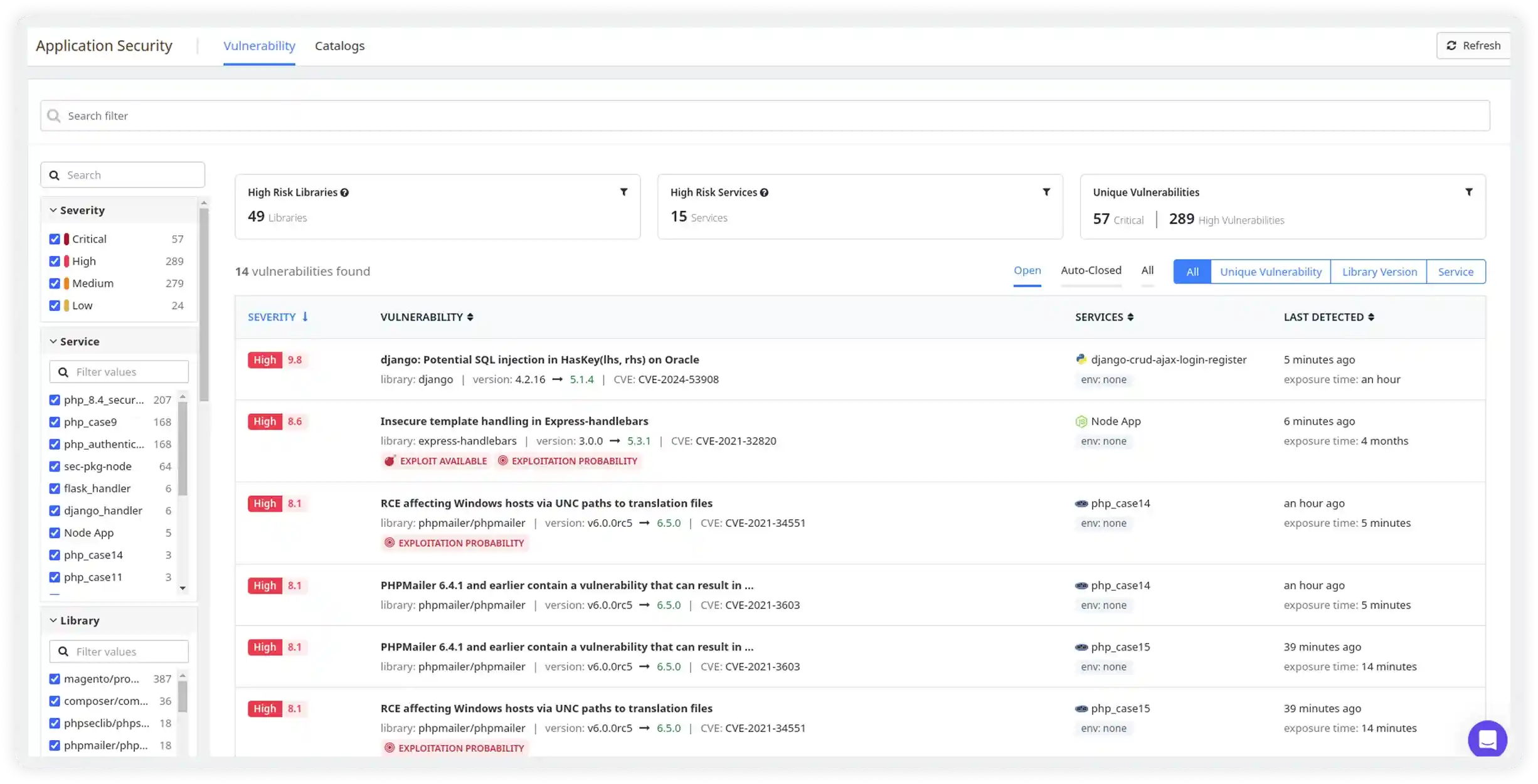
Manage Application Security in a Unified Place
Atatus ASM consolidates SAST, DAST, IAST, and SCA into one unified platform and integrates directly into developer workflows like IDE, PR, and CI/CD. Stop shipping vulnerabilities to production, without stopping your releases.
- Unified SAST + DAST + IAST + SCA. No tool sprawl, one dashboard
- CI/CD gates auto-block high-risk deployments. 90% of deploys pass without review
- IDE plugin surfaces vulnerabilities with fix suggestions at the point of coding
- PR comments and Jira tickets auto-created with exploitability context
- Executive dashboards with risk posture metrics, trends, and SLA tracking
Built for the Teams and Environments You Operate
Cloud-Native & Kubernetes
Pod-level visibility without privileged access. Auto-discover services as they scale. Track vulnerability exposure across namespaces and workloads in real time.
Microservices Security
Map attack paths across service boundaries. Identify which services expose sensitive data or sit on a path to your most critical assets before attackers do.
Zero-Day Response
When a CVE drops, know within minutes if your production environment is exposed with exploit-path evidence for your incident response team and the board.
Compliance & Regulated Industries
Continuous compliance evidence for PCI DSS, HIPAA, SOC 2, and ISO 27001. Sensitive data is redacted before it reaches your compliance scope, simplifying audits significantly.
DevSecOps Pipelines
Embed security into every PR and deployment without adding manual review cycles. 90% of deploys pass auto-gates untouched; only genuine risks require attention.
CTO & CISO Visibility
Board-ready risk posture dashboards, remediation velocity metrics, and SLA compliance reports - generated automatically from your production environment, not hand-crafted spreadsheets.
Unified Observability for Every Engineering Team
Atatus adapts to how engineering teams work across development, operations, and reliability.
Developers
Trace requests, debug errors, and identify performance issues at the code level with clear context.
DevOps
Track deployments, monitor infrastructure impact, and understand how releases affect application stability.
Release Engineer
Measure service health, latency, and error rates to maintain reliability and reduce production risk.
Milestones that spark performance excellence
Reflections from clients who've achieved unmatched excellence through innovative strategies.
Read customer stories


